

 When rolling out a new protocol such as IPv6, it is useful to consider the changes to security posture, particularly the network's attack surface. While protocol security discussions are widely available, there is often not "one place" where you can go to get information about potential attacks, references to research about those attacks, potential counters, and operational challenges. more
When rolling out a new protocol such as IPv6, it is useful to consider the changes to security posture, particularly the network's attack surface. While protocol security discussions are widely available, there is often not "one place" where you can go to get information about potential attacks, references to research about those attacks, potential counters, and operational challenges. more
 In 1998 the idea of "Newco," ICANN's informal predecessor name, was dreamlike. It was so new, so unprecedented, that it was constantly being referred to as an "experiment." It was not every day that one came across an organization conceived by one nation (e.g., the U.S.), that was available for globally shared ownership. One that was defined, in large part, by international participation. more
In 1998 the idea of "Newco," ICANN's informal predecessor name, was dreamlike. It was so new, so unprecedented, that it was constantly being referred to as an "experiment." It was not every day that one came across an organization conceived by one nation (e.g., the U.S.), that was available for globally shared ownership. One that was defined, in large part, by international participation. more
 Despite headlines now at least a couple of years old, the InfoSec world is still (largely) playing lip-service to the lack of security talent and the growing skills gap. The community is apt to quote and brandish the dire figures, but unless you're actually a hiring manager striving to fill low to mid-level security positions, you're not feeling the pain -- in fact, there's a high probability many see problem as a net positive in terms of their own employment potential and compensation. more
Despite headlines now at least a couple of years old, the InfoSec world is still (largely) playing lip-service to the lack of security talent and the growing skills gap. The community is apt to quote and brandish the dire figures, but unless you're actually a hiring manager striving to fill low to mid-level security positions, you're not feeling the pain -- in fact, there's a high probability many see problem as a net positive in terms of their own employment potential and compensation. more
 One of the fallouts of disruptive inventions is the need for new laws to counter their unexpected consequences. As it concerned the Internet, these consequences included a new tort of registering domain names identical or confusingly similar to trademarks and service marks with the intention of taking unlawful advantage of rights owners. Prior to 2000 the only civil remedy for "cybersquatting" or "cyber piracy" was expensive and time-consuming plenary actions in courts of competent jurisdiction under national trademark laws. more
One of the fallouts of disruptive inventions is the need for new laws to counter their unexpected consequences. As it concerned the Internet, these consequences included a new tort of registering domain names identical or confusingly similar to trademarks and service marks with the intention of taking unlawful advantage of rights owners. Prior to 2000 the only civil remedy for "cybersquatting" or "cyber piracy" was expensive and time-consuming plenary actions in courts of competent jurisdiction under national trademark laws. more
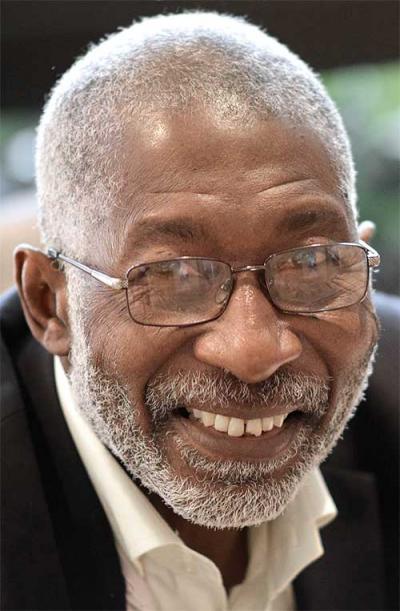
 Peter Harrison has been named among four finalists to contest elections for two seats on the American Registry for Internet Numbers (ARIN) board of trustees in October 2018. ARIN is one of five Internet registries worldwide that coordinate the distribution and administration of number resources. The registry serves the United States, Canada and several territories in the Caribbean. more
Peter Harrison has been named among four finalists to contest elections for two seats on the American Registry for Internet Numbers (ARIN) board of trustees in October 2018. ARIN is one of five Internet registries worldwide that coordinate the distribution and administration of number resources. The registry serves the United States, Canada and several territories in the Caribbean. more
 So far this year I think I've attended 20+ security conferences around the world - speaking at many of them. Along the way, I got to chat with hundreds of attendees and gather their thoughts on what they hoped to achieve or learn at each of these conferences. In way too many cases I think the conference organizers have missed the mark. I'd like to offer the following thoughts and feedback to the people organizing and facilitating these conferences (especially those catering to local security professionals). more
So far this year I think I've attended 20+ security conferences around the world - speaking at many of them. Along the way, I got to chat with hundreds of attendees and gather their thoughts on what they hoped to achieve or learn at each of these conferences. In way too many cases I think the conference organizers have missed the mark. I'd like to offer the following thoughts and feedback to the people organizing and facilitating these conferences (especially those catering to local security professionals). more
 At NANOG on the Road (NotR) in September of 2018, I participated in a panel on BGP security -- specifically the deployment of Route Origin Authentication (ROA), with some hints and overtones of path validation by carrying signatures in BGP updates (BGPsec). This is an area I have been working in for... 20 years? ... at this point, so I have seen the argument develop across these years many times, and in many ways. more
At NANOG on the Road (NotR) in September of 2018, I participated in a panel on BGP security -- specifically the deployment of Route Origin Authentication (ROA), with some hints and overtones of path validation by carrying signatures in BGP updates (BGPsec). This is an area I have been working in for... 20 years? ... at this point, so I have seen the argument develop across these years many times, and in many ways. more
 A split Panel in an early decision under the Uniform Domain Name Dispute Resolution Policy (UDRP) held that parties deserve more than "[i]t depends [on] what panelist you draw." Time Inc. v. Chip Cooper, D2000-1342 (WIPO February 13, 2001). That's one side of the paradigm; the other side makes demands on the parties to prove their contentions, either of cybersquatting (one element of which is proving that respondent lacks rights or legitimate interests) or rebutting the claim (one element of which is respondent demonstrating it has rights or legitimate interests). more
A split Panel in an early decision under the Uniform Domain Name Dispute Resolution Policy (UDRP) held that parties deserve more than "[i]t depends [on] what panelist you draw." Time Inc. v. Chip Cooper, D2000-1342 (WIPO February 13, 2001). That's one side of the paradigm; the other side makes demands on the parties to prove their contentions, either of cybersquatting (one element of which is proving that respondent lacks rights or legitimate interests) or rebutting the claim (one element of which is respondent demonstrating it has rights or legitimate interests). more
 In a little over two weeks, precisely in 17 days (on 11 October 2018 at 16:00 UTC), ICANN will roll the Domain Name System Security Extensions (DNSSEC) root Key Signing Key (KSK). If you are a Domain Name System (DNS) and DNSSEC expert already engaged globally on the topic, you are certainly both well aware and ready for the rollover. This article is probably not for you! If however, you are out there focused on your day to day running or managing a DNS infrastructure... more
In a little over two weeks, precisely in 17 days (on 11 October 2018 at 16:00 UTC), ICANN will roll the Domain Name System Security Extensions (DNSSEC) root Key Signing Key (KSK). If you are a Domain Name System (DNS) and DNSSEC expert already engaged globally on the topic, you are certainly both well aware and ready for the rollover. This article is probably not for you! If however, you are out there focused on your day to day running or managing a DNS infrastructure... more
This is a one hour podcast giving all details about what the .BEST social network is going to be and how users will be able to generate an income from it... Cyril Fremont gives lots of details on how his social network, focusing on reviews, is going to be different from Google Reviews, Facebook, Yelp and TripAdvisors. If one would be tempted to think that ... well, "that's just going to be another social network", then, I strongly suggest to listen carefully the part of the interview on the decentralization of this network. more
 Last week an ICANN registrar, Namejuice, went off the air for the better part of the day -- disappearing off the internet at approximately 8:30 am, taking all domains delegated to its nameservers with it, and did not come back online until close to 11 pm ET. That was a full business day and more of complete outage for all businesses, domains, websites, and email who were using the Namejuice nameservers -- something many of them were doing. more
Last week an ICANN registrar, Namejuice, went off the air for the better part of the day -- disappearing off the internet at approximately 8:30 am, taking all domains delegated to its nameservers with it, and did not come back online until close to 11 pm ET. That was a full business day and more of complete outage for all businesses, domains, websites, and email who were using the Namejuice nameservers -- something many of them were doing. more
 Brandsight recently concluded their Second Annual Domain Management Survey. Respondents to the survey were corporate domain name professionals. Of those that responded, 35% had portfolios that were between 3,000-10,000 domains and another 30% had portfolios greater than 10,000 domains. Fifty-seven percent of respondents reported that they manage domains out of the legal department, with the remaining respondents' portfolios managed out of IT, marketing and other groups. more
Brandsight recently concluded their Second Annual Domain Management Survey. Respondents to the survey were corporate domain name professionals. Of those that responded, 35% had portfolios that were between 3,000-10,000 domains and another 30% had portfolios greater than 10,000 domains. Fifty-seven percent of respondents reported that they manage domains out of the legal department, with the remaining respondents' portfolios managed out of IT, marketing and other groups. more
 Three Caribbean candidates -- Peter Harrison, Kerrie-Ann Richards and Alicia Trotman -- have been named among the final candidates to contest elections for leadership roles at the American Registry for Internet Numbers (ARIN) in October. ARIN is one of five Internet registries worldwide that coordinate the distribution and administration of number resources. The registry serves the United States, Canada and several territories in the Caribbean. more
Three Caribbean candidates -- Peter Harrison, Kerrie-Ann Richards and Alicia Trotman -- have been named among the final candidates to contest elections for leadership roles at the American Registry for Internet Numbers (ARIN) in October. ARIN is one of five Internet registries worldwide that coordinate the distribution and administration of number resources. The registry serves the United States, Canada and several territories in the Caribbean. more
 As part of my job, I manage an incident response team that was engaged by a significant organization in Georgia whose network was infected by the QBOT (a.k.a. QAKBOT) malware. The customer had been infected for over a year, several teams before ours had failed to solve the problem, and they continued to get reinfected by the malware when they thought they had eradicated it. Over time it had spread to more than 1,000 computers in their ecosystem stealing user credentials along the way. more
As part of my job, I manage an incident response team that was engaged by a significant organization in Georgia whose network was infected by the QBOT (a.k.a. QAKBOT) malware. The customer had been infected for over a year, several teams before ours had failed to solve the problem, and they continued to get reinfected by the malware when they thought they had eradicated it. Over time it had spread to more than 1,000 computers in their ecosystem stealing user credentials along the way. more
 DNS-over-TLS has recently become a welcome addition to the range of security protocols supported by DNS. It joins TSIG, SIG(0) and DNSSEC to add privacy, and, in the absence of validating stub resolvers, necessary data integrity on the link between a full-service resolver and the users' stub resolver. (The authenticated source feature of TLS may also offer some additional benefits for those of a nervous disposition.) Good stuff. What is not good stuff is... more
DNS-over-TLS has recently become a welcome addition to the range of security protocols supported by DNS. It joins TSIG, SIG(0) and DNSSEC to add privacy, and, in the absence of validating stub resolvers, necessary data integrity on the link between a full-service resolver and the users' stub resolver. (The authenticated source feature of TLS may also offer some additional benefits for those of a nervous disposition.) Good stuff. What is not good stuff is... more
Sponsored byWhoisXML API

Sponsored byIPv4.Global

Sponsored byVerisign

Sponsored byCSC

Sponsored byRadix

Sponsored byDNIB.com

Sponsored byVerisign
