

Cybersecurity |
Sponsored by |

|
 New data on DNS abuse reveals most malicious domains remain active beyond 24 hours, while a handful of registrars host the bulk of infrastructure, leaving India's population of first-generation internet users uniquely exposed to fraud.
New data on DNS abuse reveals most malicious domains remain active beyond 24 hours, while a handful of registrars host the bulk of infrastructure, leaving India's population of first-generation internet users uniquely exposed to fraud.
 As AI agents automate phishing, impersonation and domain abuse at machine scale, the Brand Registry Group argues that dotBrand domains are evolving from marketing assets into trust infrastructure underpinning cybersecurity, identity and interactions across the internet.
As AI agents automate phishing, impersonation and domain abuse at machine scale, the Brand Registry Group argues that dotBrand domains are evolving from marketing assets into trust infrastructure underpinning cybersecurity, identity and interactions across the internet.
 As power grids depend on microsecond precision, states must treat time synchronization as sovereign infrastructure, hardening satellite, fiber and orbital defenses against hybrid attacks that could trigger catastrophic blackouts through resilient sovereign time defense frameworks.
As power grids depend on microsecond precision, states must treat time synchronization as sovereign infrastructure, hardening satellite, fiber and orbital defenses against hybrid attacks that could trigger catastrophic blackouts through resilient sovereign time defense frameworks.
 As AI reshapes the digital world, online safety depends on balancing smarter protection with growing risks. From cybersecurity to privacy concerns, understanding AI's role can help users stay secure, informed, and resilient online.
As AI reshapes the digital world, online safety depends on balancing smarter protection with growing risks. From cybersecurity to privacy concerns, understanding AI's role can help users stay secure, informed, and resilient online.
 Fake news spreads quickly online, fueling distrust, manipulation, and conflict. As AI-generated content grows more sophisticated, media literacy, fact-checking, and vigilance are essential to protecting online safety and preserving trust in information.
Fake news spreads quickly online, fueling distrust, manipulation, and conflict. As AI-generated content grows more sophisticated, media literacy, fact-checking, and vigilance are essential to protecting online safety and preserving trust in information.
 As cross-border cyber enforcement falters, critics argue Article 19's DNS abuse framework prioritizes procedural purity over user protection, leaving courts too slow to counter AI-driven phishing, rapid-flux domains, and increasingly automated online threats.
As cross-border cyber enforcement falters, critics argue Article 19's DNS abuse framework prioritizes procedural purity over user protection, leaving courts too slow to counter AI-driven phishing, rapid-flux domains, and increasingly automated online threats.
 As Africa digitises rapidly, control over data is emerging as a strategic contest. Foreign infrastructure dominance exposes economic and cybersecurity vulnerabilities, pushing governments to prioritise digital capability, regional cooperation, and stronger sovereignty over the systems powering the continent's future.
As Africa digitises rapidly, control over data is emerging as a strategic contest. Foreign infrastructure dominance exposes economic and cybersecurity vulnerabilities, pushing governments to prioritise digital capability, regional cooperation, and stronger sovereignty over the systems powering the continent's future.
 Fake recruitment websites exploiting India's young job seekers are proliferating, exposing millions to identity theft, financial fraud and malware while regulators, registrars and digital literacy programs struggle to keep pace with a growing labor market.
Fake recruitment websites exploiting India's young job seekers are proliferating, exposing millions to identity theft, financial fraud and malware while regulators, registrars and digital literacy programs struggle to keep pace with a growing labor market.
 As states chase digital sovereignty through clouds, AI and localized infrastructure, the internet's globally coordinated foundations reveal a harder truth: operational continuity depends less on control than on interoperable systems built on trust and governance.
As states chase digital sovereignty through clouds, AI and localized infrastructure, the internet's globally coordinated foundations reveal a harder truth: operational continuity depends less on control than on interoperable systems built on trust and governance.
 Recent court rulings in Europe and America are reshaping access to technical standards, weakening paywalls and strengthening the principle that publicly mandated knowledge belongs to citizens, regulators and increasingly AI systems that depend on machine-readable information.
Recent court rulings in Europe and America are reshaping access to technical standards, weakening paywalls and strengthening the principle that publicly mandated knowledge belongs to citizens, regulators and increasingly AI systems that depend on machine-readable information.
 Africa's digital boom is accelerating, but safeguards lag. Governments and firms deploy systems at speed, while weak enforcement and fragmented oversight leave economies exposed to mounting cyber risks.
Africa's digital boom is accelerating, but safeguards lag. Governments and firms deploy systems at speed, while weak enforcement and fragmented oversight leave economies exposed to mounting cyber risks.
 Subsea cables underpin global data flows, yet resilience, control and deep sea access now define digital sovereignty as governance fragments, hyperscalers consolidate ownership, and states prioritize survivability over efficiency in an increasingly contested geopolitical seabed.
Subsea cables underpin global data flows, yet resilience, control and deep sea access now define digital sovereignty as governance fragments, hyperscalers consolidate ownership, and states prioritize survivability over efficiency in an increasingly contested geopolitical seabed.
 TNN proposes a contractual chain of indemnity to shift legal risk in global takedowns, replacing patchy statutory protections with enforceable accountability and a fund that makes good-faith action commercially viable for smaller intermediaries.
TNN proposes a contractual chain of indemnity to shift legal risk in global takedowns, replacing patchy statutory protections with enforceable accountability and a fund that makes good-faith action commercially viable for smaller intermediaries.
 Community networks, locally built and governed, are emerging across Africa as cost-effective tools to extend connectivity, bolster digital sovereignty, and improve cyber resilience, despite regulatory, financial, and technical constraints that hinder broader adoption.
Community networks, locally built and governed, are emerging across Africa as cost-effective tools to extend connectivity, bolster digital sovereignty, and improve cyber resilience, despite regulatory, financial, and technical constraints that hinder broader adoption.
 Third-party domains exploiting brand names are proliferating, with 88% of homoglyphs externally owned. Many remain dormant yet email-enabled, creating scalable phishing risks as attackers increasingly target trust rather than infrastructure.
Third-party domains exploiting brand names are proliferating, with 88% of homoglyphs externally owned. Many remain dormant yet email-enabled, creating scalable phishing risks as attackers increasingly target trust rather than infrastructure.
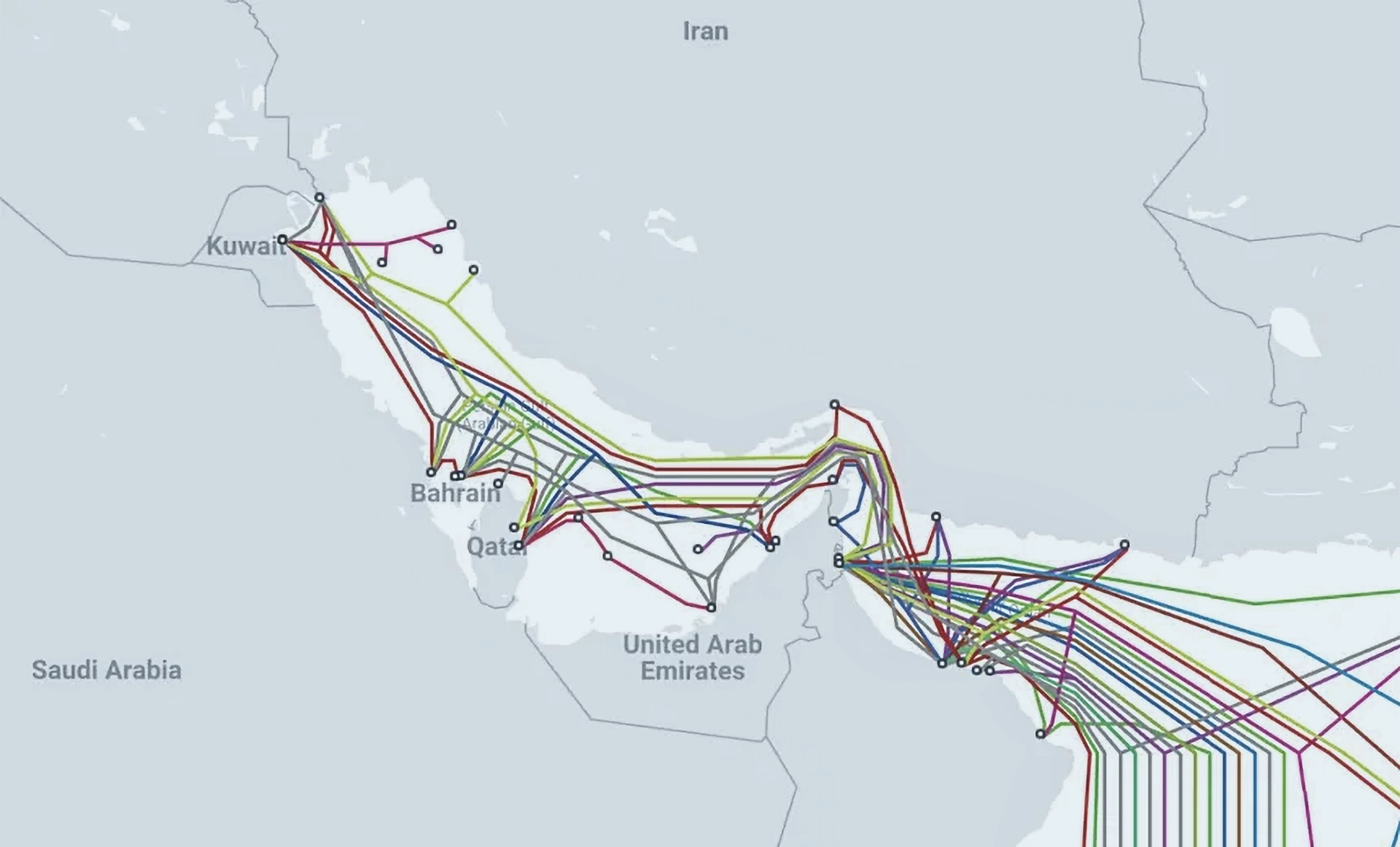 Iran Threatens Subsea Internet Cables in the Strait of Hormuz
Iran Threatens Subsea Internet Cables in the Strait of Hormuz U.S. Blocks Foreign-Made Routers Over Cybersecurity Fears
U.S. Blocks Foreign-Made Routers Over Cybersecurity Fears Iran Targeted by Self-Propagating Malware in Supply-Chain Cyberattacks
Iran Targeted by Self-Propagating Malware in Supply-Chain Cyberattacks Iran Expands Digital Dragnet After Crushing Protests
Iran Expands Digital Dragnet After Crushing Protests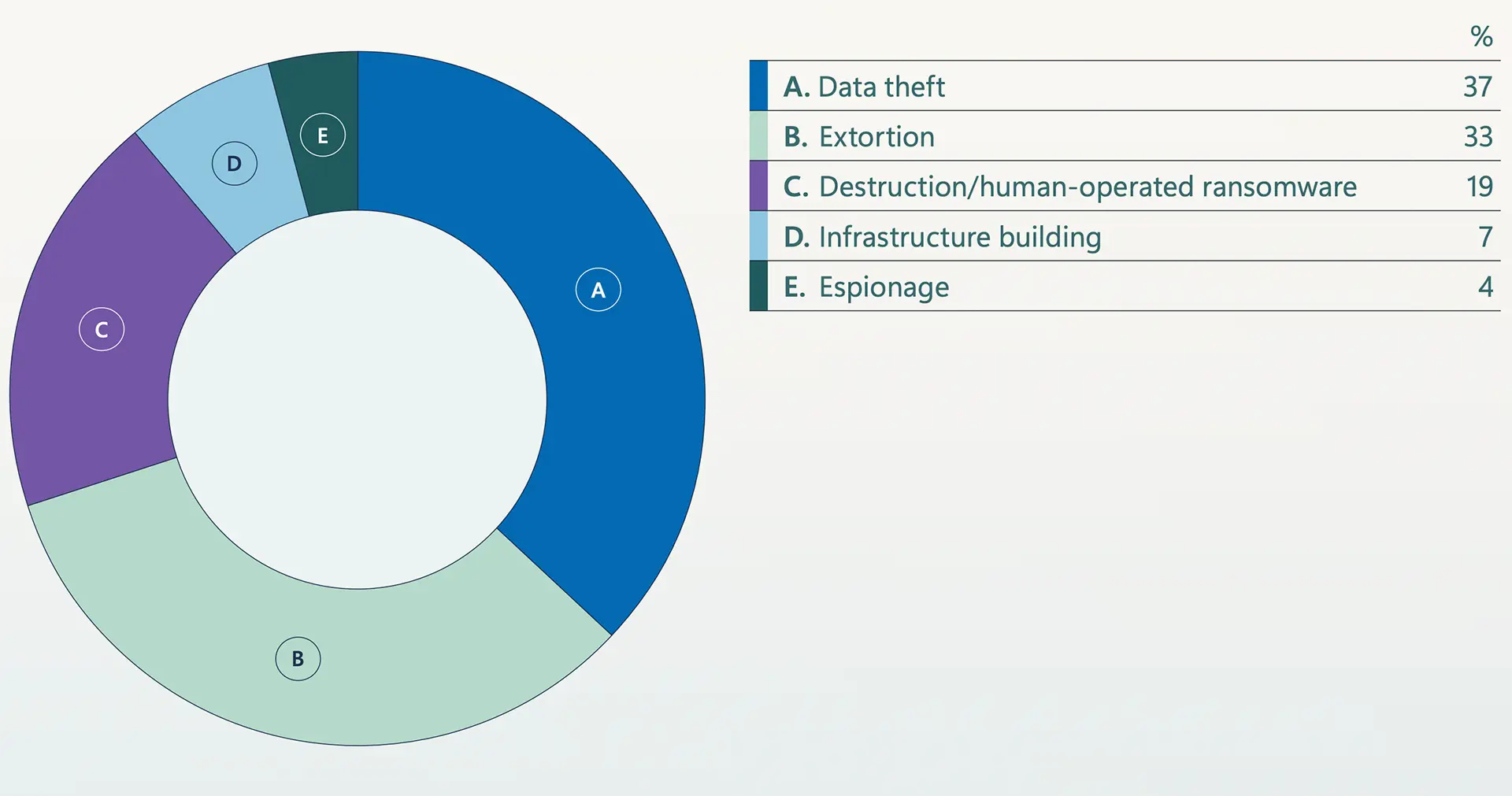 Microsoft Warns Extortion Drives Majority of Attacks Amid AI Escalation, Identity Collapse, and Global Fragmentation
Microsoft Warns Extortion Drives Majority of Attacks Amid AI Escalation, Identity Collapse, and Global Fragmentation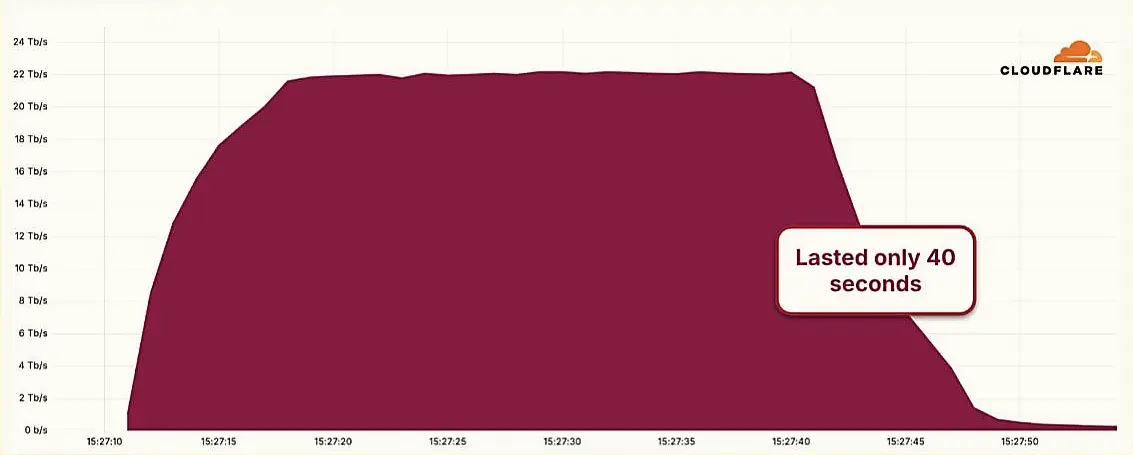 Hyper-Volumetric DDoS Attack Sets New Benchmark at 22.2 Tbps
Hyper-Volumetric DDoS Attack Sets New Benchmark at 22.2 Tbps European Airports Still Reeling from Ransomware Attack as Software Fix Nears
European Airports Still Reeling from Ransomware Attack as Software Fix Nears Chinese APT Groups Exploit Global Domains in Sweeping Cyber Campaign
Chinese APT Groups Exploit Global Domains in Sweeping Cyber CampaignAddressing DNS abuse and maintaining a healthy DNS ecosystem are important components of Verisign's commitment to being a responsible steward of the internet. We continuously engage with the Internet Corporation for Assigned Names and Numbers (ICANN) and other industry partners to help ensure the secure, stable and resilient operation of the DNS. more
Verisign just released its Q2 2018 DDoS Trends Report, which represents a unique view into the attack trends unfolding online, through observations and insights derived from distributed denial of service (DDoS) attack mitigations enacted on behalf of customers of Verisign DDoS Protection Services. more
Currently scheduled for October 11, 2018, the Internet Corporation for Assigned Names and Numbers (ICANN) plans to change the cryptographic key that helps to secure the internet's Domain Name System (DNS) by performing a Root Zone Domain Name System Security Extensions (DNSSEC) key signing key (KSK) rollover. more
Verisign has released its Q1 2018 DDoS Trends Report, which represents a unique view into the attack trends unfolding online, through observations and insights derived from distributed denial of service (DDoS) attack mitigations enacted on behalf of Verisign DDoS Protection Services, and security research conducted by Verisign Security Services. more
As DNS attacks grow in frequency and impact, organizations can no longer afford to overlook DNS security as part of their overall defense-in-depth strategy. As with IT security in general, no single tactic can address the entire DNS threat landscape or secure the complete DNS ecosystem. more
Verisign has released its Q4 2017 DDoS Trends Report, which represents a unique view into the attack trends unfolding online, through observations and insights derived from distributed denial of service (DDoS) attack mitigations enacted on behalf of Verisign DDoS Protection Services and security research conducted by Verisign Security Services. more
Cybercriminals recognize the value of DNS availability and look for ways to compromise DNS uptime and the DNS servers that support it. As such, DNS becomes an important point of security enforcement and a potential point in the Cyber Kill Chain for many cyber-attacks. more