

 The internet is fragmenting across cables, routing systems and governance. Most network engineers, focused on regional operations, are missing how technical infrastructure and state power are reshaping a once interoperable network.
The internet is fragmenting across cables, routing systems and governance. Most network engineers, focused on regional operations, are missing how technical infrastructure and state power are reshaping a once interoperable network.
 This essay argues that Internet governance has drifted from technical coordination into unaccountable institutional power, and proposes "Running-Code Primacy" as a post-RIR framework grounded in distributed validation, interoperability, and voluntary adoption rather than registry authority.
This essay argues that Internet governance has drifted from technical coordination into unaccountable institutional power, and proposes "Running-Code Primacy" as a post-RIR framework grounded in distributed validation, interoperability, and voluntary adoption rather than registry authority.
 As AI agents scale, IP reputation emerges as a hidden constraint, shaping access to external systems and degrading performance. Managing network identity, not just models, is becoming essential for reliable data collection.
As AI agents scale, IP reputation emerges as a hidden constraint, shaping access to external systems and degrading performance. Managing network identity, not just models, is becoming essential for reliable data collection.
 Regional internet registries, once coordinators of technical scarcity, now effectively cap liability at $100 while retaining control over national numbering systems, shifting risk to states and entrenching a governance model critics argue today inverts sovereignty.
Regional internet registries, once coordinators of technical scarcity, now effectively cap liability at $100 while retaining control over national numbering systems, shifting risk to states and entrenching a governance model critics argue today inverts sovereignty.
 Fifteen years after IPv4 exhaustion, a transfer market has reallocated scarce address space, enabling internet growth, despite uneven registry policies, opaque fees, and lingering resistance to a system that proved more pragmatic than planned reclamation.
Fifteen years after IPv4 exhaustion, a transfer market has reallocated scarce address space, enabling internet growth, despite uneven registry policies, opaque fees, and lingering resistance to a system that proved more pragmatic than planned reclamation.
 Regional Internet registries, built for coordination, now sit atop scarce IPv4 assets while bearing little liability, suppressing capitalization and imposing "double extraction" that weakens operators, distorts markets and threatens the stability of global internet uniqueness.
Regional Internet registries, built for coordination, now sit atop scarce IPv4 assets while bearing little liability, suppressing capitalization and imposing "double extraction" that weakens operators, distorts markets and threatens the stability of global internet uniqueness.
 IPv4 scarcity turned regional internet registries from clerks into gatekeepers of a valuable resource. Yet liability caps remain trivial, leaving powerful institutions with little accountability and incentives for conflict and structural breakdown ahead.
IPv4 scarcity turned regional internet registries from clerks into gatekeepers of a valuable resource. Yet liability caps remain trivial, leaving powerful institutions with little accountability and incentives for conflict and structural breakdown ahead.
 As IP addresses move across borders, outdated geolocation guesses cause service failures and regulatory risks. Geofeed and Signed Geofeed replace inference with verified declarations, promising accurate, resilient and sovereign foundations for global internet infrastructure governance.
As IP addresses move across borders, outdated geolocation guesses cause service failures and regulatory risks. Geofeed and Signed Geofeed replace inference with verified declarations, promising accurate, resilient and sovereign foundations for global internet infrastructure governance.
 As geopolitical tensions expose the fragility of subsea cables, Low Earth Orbit satellites and the QUIC protocol promise a more resilient internet by diversifying routes, preserving session continuity, and redefining control over global data flows.
As geopolitical tensions expose the fragility of subsea cables, Low Earth Orbit satellites and the QUIC protocol promise a more resilient internet by diversifying routes, preserving session continuity, and redefining control over global data flows.
 DNSSEC promised to secure DNS with cryptographic proof, yet messy rollouts, outages, and hype backlash ruined its reputation. This piece argues that storytelling and emotions shape adoption as much as specs, and that automation enables a reset.
DNSSEC promised to secure DNS with cryptographic proof, yet messy rollouts, outages, and hype backlash ruined its reputation. This piece argues that storytelling and emotions shape adoption as much as specs, and that automation enables a reset.
 The Internet Society is accepting nominations for two seats on the 2026 Board of the Public Interest Registry, the non-profit behind .ORG and other domains serving civil society. Deadline: 30 January 2026.
The Internet Society is accepting nominations for two seats on the 2026 Board of the Public Interest Registry, the non-profit behind .ORG and other domains serving civil society. Deadline: 30 January 2026.
 The Internet is evolving far beyond screens and smartphones. A proposed seven-stage framework anticipates a future shaped by autonomous agents, sensory wearables, global connectivity, and quantum networks redefining how humans interact with the digital world.
The Internet is evolving far beyond screens and smartphones. A proposed seven-stage framework anticipates a future shaped by autonomous agents, sensory wearables, global connectivity, and quantum networks redefining how humans interact with the digital world.
 A revised governance document for Regional Internet Registries aims to replace outdated policy, enhancing transparency, continuity, and oversight in managing IP resources while preparing for future disruptions across the global Internet infrastructure.
A revised governance document for Regional Internet Registries aims to replace outdated policy, enhancing transparency, continuity, and oversight in managing IP resources while preparing for future disruptions across the global Internet infrastructure.
 The Internet has evolved from a scarcity-driven system into one defined by abundance, reshaping infrastructure, governance, and economic models while challenging long-held assumptions about addressing, network roles, and the future of protocol design.
The Internet has evolved from a scarcity-driven system into one defined by abundance, reshaping infrastructure, governance, and economic models while challenging long-held assumptions about addressing, network roles, and the future of protocol design.
 The Internet Society is seeking nominations for its 2026 Board of Trustees. Four seats are open across its global stakeholder communities, offering an opportunity to help steer the future of a trusted, open Internet.
The Internet Society is seeking nominations for its 2026 Board of Trustees. Four seats are open across its global stakeholder communities, offering an opportunity to help steer the future of a trusted, open Internet.
 David J. Farber, Early Architect of the Internet, Dies at 91
David J. Farber, Early Architect of the Internet, Dies at 91 Internet Visionaries Honored with Postel Service Award
Internet Visionaries Honored with Postel Service Award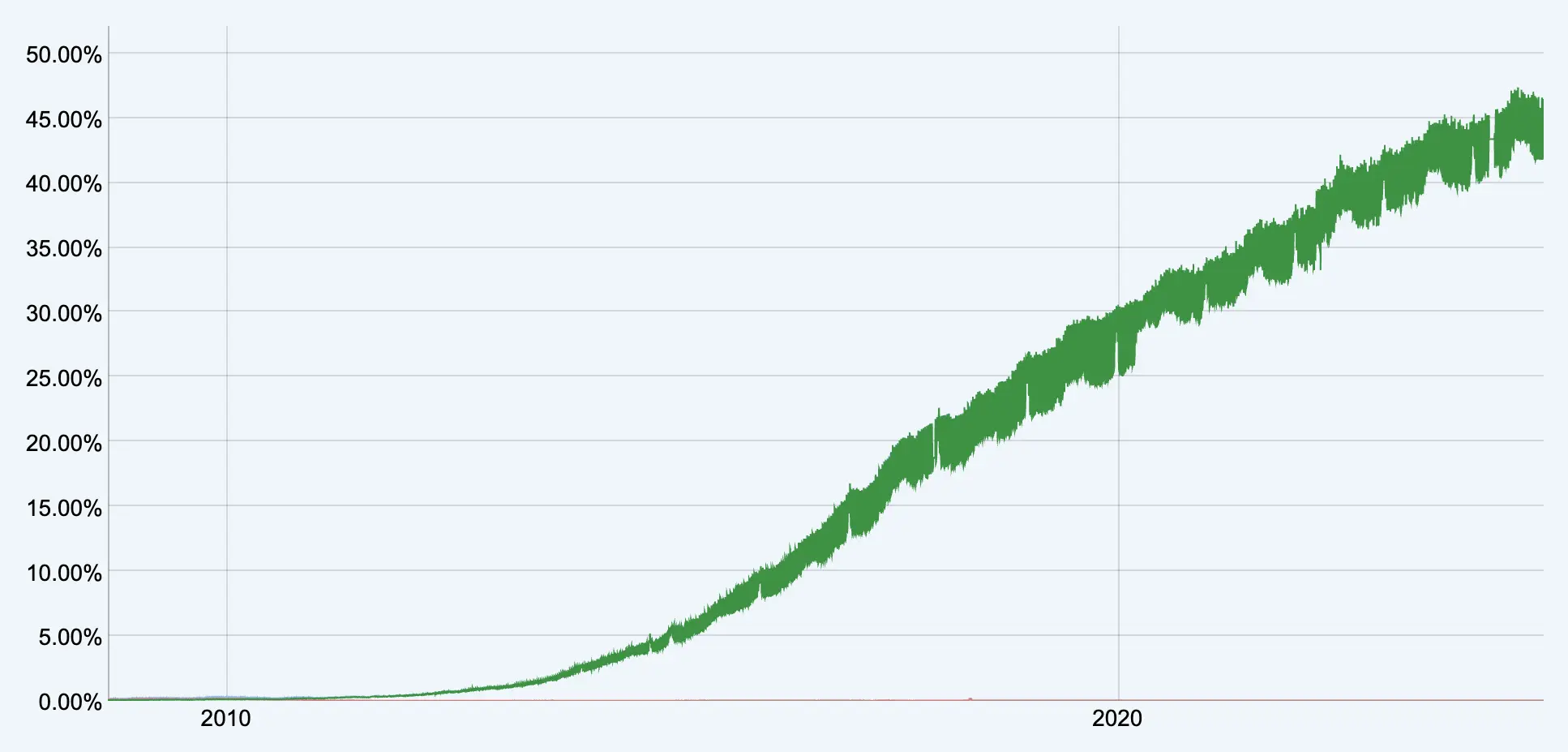 IPv6 Transition Stalls as Internet Moves Beyond IP Addresses
IPv6 Transition Stalls as Internet Moves Beyond IP Addresses Internet’s 50th Anniversary Celebrated Worldwide with IEEE Event
Internet’s 50th Anniversary Celebrated Worldwide with IEEE Event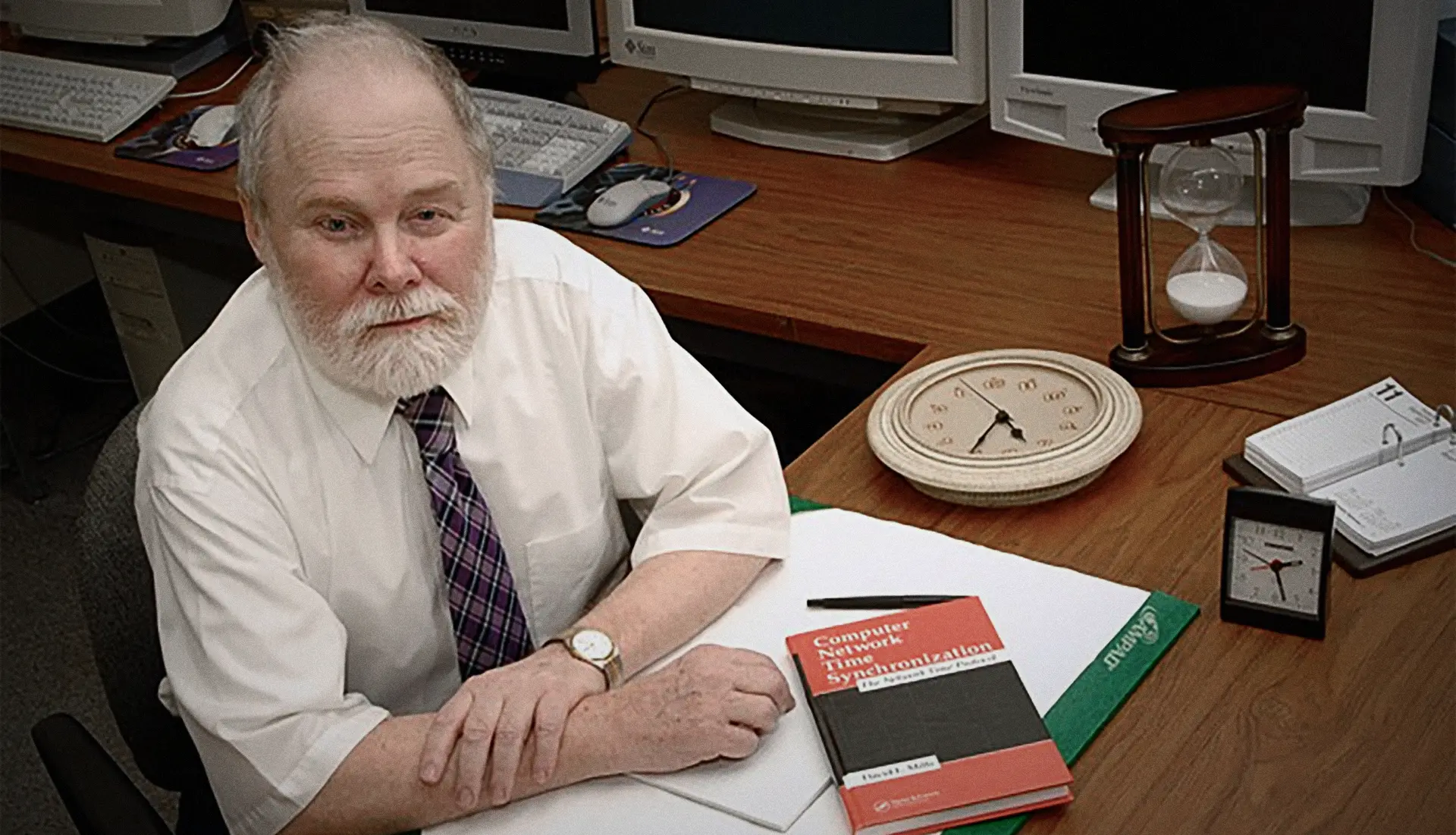 In Memoriam: Dave Mills (1938-2024)
In Memoriam: Dave Mills (1938-2024)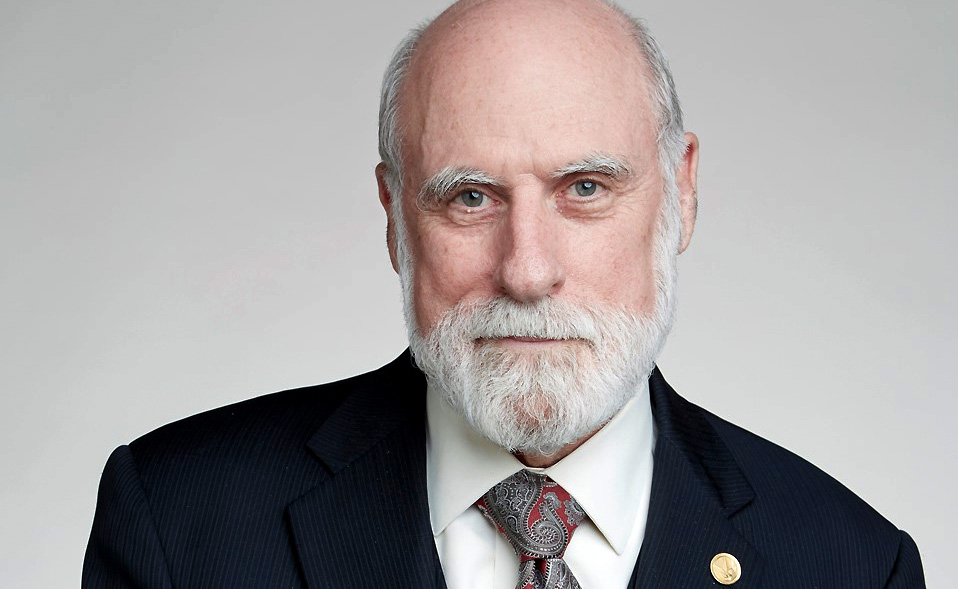 Vint Cerf Receives IEEE Medal of Honor
Vint Cerf Receives IEEE Medal of Honor U.S. Department of Energy Unveils Blueprint for the Quantum Internet
U.S. Department of Energy Unveils Blueprint for the Quantum Internet “lo” and Behold
“lo” and Behold