

 An official-looking renewal notice reveals how open namespaces shift verification burdens onto users. Restricted government domains like .gov.au function as trust infrastructure, embedding authority into the namespace and reducing fraud, confusion, and verification costs.
An official-looking renewal notice reveals how open namespaces shift verification burdens onto users. Restricted government domains like .gov.au function as trust infrastructure, embedding authority into the namespace and reducing fraud, confusion, and verification costs.
 Mounting signs of consumer distress, from unpaid utility bills to rising loan delinquencies, are raising uncomfortable questions for internet providers about whether broadband remains recession-proof as households increasingly trade home connections for cheaper wireless alternatives.
Mounting signs of consumer distress, from unpaid utility bills to rising loan delinquencies, are raising uncomfortable questions for internet providers about whether broadband remains recession-proof as households increasingly trade home connections for cheaper wireless alternatives.
 ICANN's Smart Africa engagement shows how proposals can gain authority without formal endorsement, raising harder questions about CAIGA, ICP-2 and whether regional partnerships need earlier safeguards when RIR governance begins to shift under institutional cover.
ICANN's Smart Africa engagement shows how proposals can gain authority without formal endorsement, raising harder questions about CAIGA, ICP-2 and whether regional partnerships need earlier safeguards when RIR governance begins to shift under institutional cover.
 As cross-border cyber enforcement falters, critics argue Article 19's DNS abuse framework prioritizes procedural purity over user protection, leaving courts too slow to counter AI-driven phishing, rapid-flux domains, and increasingly automated online threats.
As cross-border cyber enforcement falters, critics argue Article 19's DNS abuse framework prioritizes procedural purity over user protection, leaving courts too slow to counter AI-driven phishing, rapid-flux domains, and increasingly automated online threats.
 As Africa digitises rapidly, control over data is emerging as a strategic contest. Foreign infrastructure dominance exposes economic and cybersecurity vulnerabilities, pushing governments to prioritise digital capability, regional cooperation, and stronger sovereignty over the systems powering the continent's future.
As Africa digitises rapidly, control over data is emerging as a strategic contest. Foreign infrastructure dominance exposes economic and cybersecurity vulnerabilities, pushing governments to prioritise digital capability, regional cooperation, and stronger sovereignty over the systems powering the continent's future.
 An ICANN-backed African internet-governance initiative exposed a deeper institutional problem: whether global coordinators must warn when regional policy processes drift into RIR governance, before facilitation, silence and funding harden into implied legitimacy for contested reforms.
An ICANN-backed African internet-governance initiative exposed a deeper institutional problem: whether global coordinators must warn when regional policy processes drift into RIR governance, before facilitation, silence and funding harden into implied legitimacy for contested reforms.
 Universal Acceptance Day 2026 marks progress toward a multilingual internet, as UNESCO and ICANN deepen cooperation. Yet unresolved implementation failures and weak registry stewardship still hinder truly inclusive digital access worldwide.
Universal Acceptance Day 2026 marks progress toward a multilingual internet, as UNESCO and ICANN deepen cooperation. Yet unresolved implementation failures and weak registry stewardship still hinder truly inclusive digital access worldwide.
 Fake recruitment websites exploiting India's young job seekers are proliferating, exposing millions to identity theft, financial fraud and malware while regulators, registrars and digital literacy programs struggle to keep pace with a growing labor market.
Fake recruitment websites exploiting India's young job seekers are proliferating, exposing millions to identity theft, financial fraud and malware while regulators, registrars and digital literacy programs struggle to keep pace with a growing labor market.
 This essay argues that Internet governance has drifted from technical coordination into unaccountable institutional power, and proposes "Running-Code Primacy" as a post-RIR framework grounded in distributed validation, interoperability, and voluntary adoption rather than registry authority.
This essay argues that Internet governance has drifted from technical coordination into unaccountable institutional power, and proposes "Running-Code Primacy" as a post-RIR framework grounded in distributed validation, interoperability, and voluntary adoption rather than registry authority.
 As AI devours ever more information, the world faces a costly data-storage crisis. Researchers are betting etched silica glass could preserve vast archives for centuries while consuming far less energy than today's hard drives and magnetic tapes.
As AI devours ever more information, the world faces a costly data-storage crisis. Researchers are betting etched silica glass could preserve vast archives for centuries while consuming far less energy than today's hard drives and magnetic tapes.
 Geopolitical fragmentation is colliding with the internet's distributed architecture, exposing how sovereign cloud concentration and AI infrastructure can weaken resilience, amplify strategic vulnerabilities, and challenge whether governance can preserve interoperability while managing dependency under stress.
Geopolitical fragmentation is colliding with the internet's distributed architecture, exposing how sovereign cloud concentration and AI infrastructure can weaken resilience, amplify strategic vulnerabilities, and challenge whether governance can preserve interoperability while managing dependency under stress.
 As states chase digital sovereignty through clouds, AI and localized infrastructure, the internet's globally coordinated foundations reveal a harder truth: operational continuity depends less on control than on interoperable systems built on trust and governance.
As states chase digital sovereignty through clouds, AI and localized infrastructure, the internet's globally coordinated foundations reveal a harder truth: operational continuity depends less on control than on interoperable systems built on trust and governance.
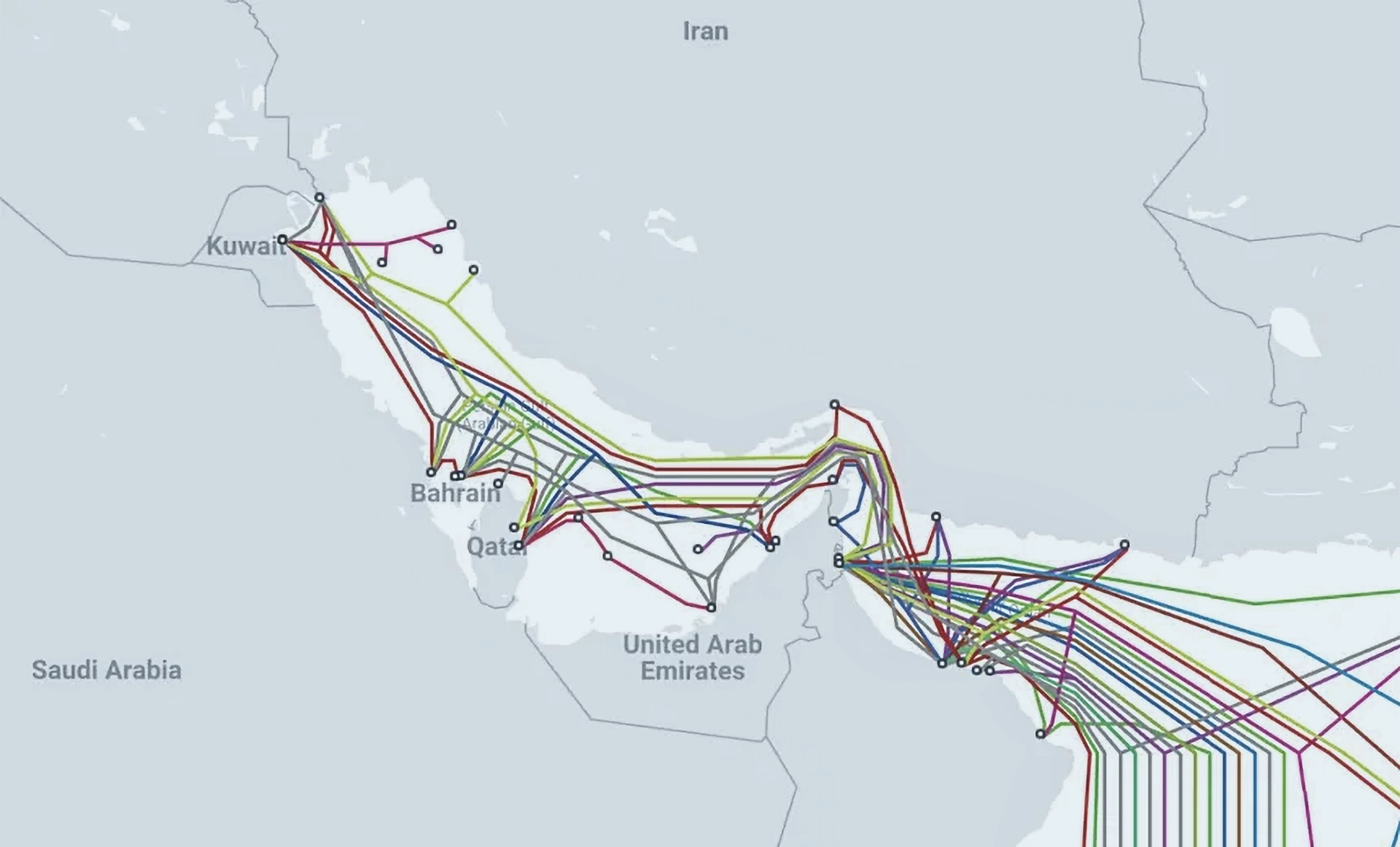
 Missile strikes on Gulf data centres exposed a deeper contradiction at the heart of digital sovereignty: governments seek territorial control over internet infrastructure whose resilience still depends upon globally distributed coordination and interdependence across borders.
Missile strikes on Gulf data centres exposed a deeper contradiction at the heart of digital sovereignty: governments seek territorial control over internet infrastructure whose resilience still depends upon globally distributed coordination and interdependence across borders.
 Recent court rulings in Europe and America are reshaping access to technical standards, weakening paywalls and strengthening the principle that publicly mandated knowledge belongs to citizens, regulators and increasingly AI systems that depend on machine-readable information.
Recent court rulings in Europe and America are reshaping access to technical standards, weakening paywalls and strengthening the principle that publicly mandated knowledge belongs to citizens, regulators and increasingly AI systems that depend on machine-readable information.
 Three decades after Iridium's costly collapse, falling launch costs and improved signal processing are reviving satellite-to-phone ambitions, as Starlink, Amazon and AST SpaceMobile race to build direct-to-device networks that could reshape mobile coverage and competition.
Three decades after Iridium's costly collapse, falling launch costs and improved signal processing are reviving satellite-to-phone ambitions, as Starlink, Amazon and AST SpaceMobile race to build direct-to-device networks that could reshape mobile coverage and competition.
 Iran Threatens Subsea Internet Cables in the Strait of Hormuz
Iran Threatens Subsea Internet Cables in the Strait of Hormuz Inside Iran’s Shift From Internet Shutdowns to Tiered Connectivity
Inside Iran’s Shift From Internet Shutdowns to Tiered Connectivity ICANN Opens New gTLD Applications for First Time Since 2012, With $227K Entry Fee and 27 Scripts
ICANN Opens New gTLD Applications for First Time Since 2012, With $227K Entry Fee and 27 Scripts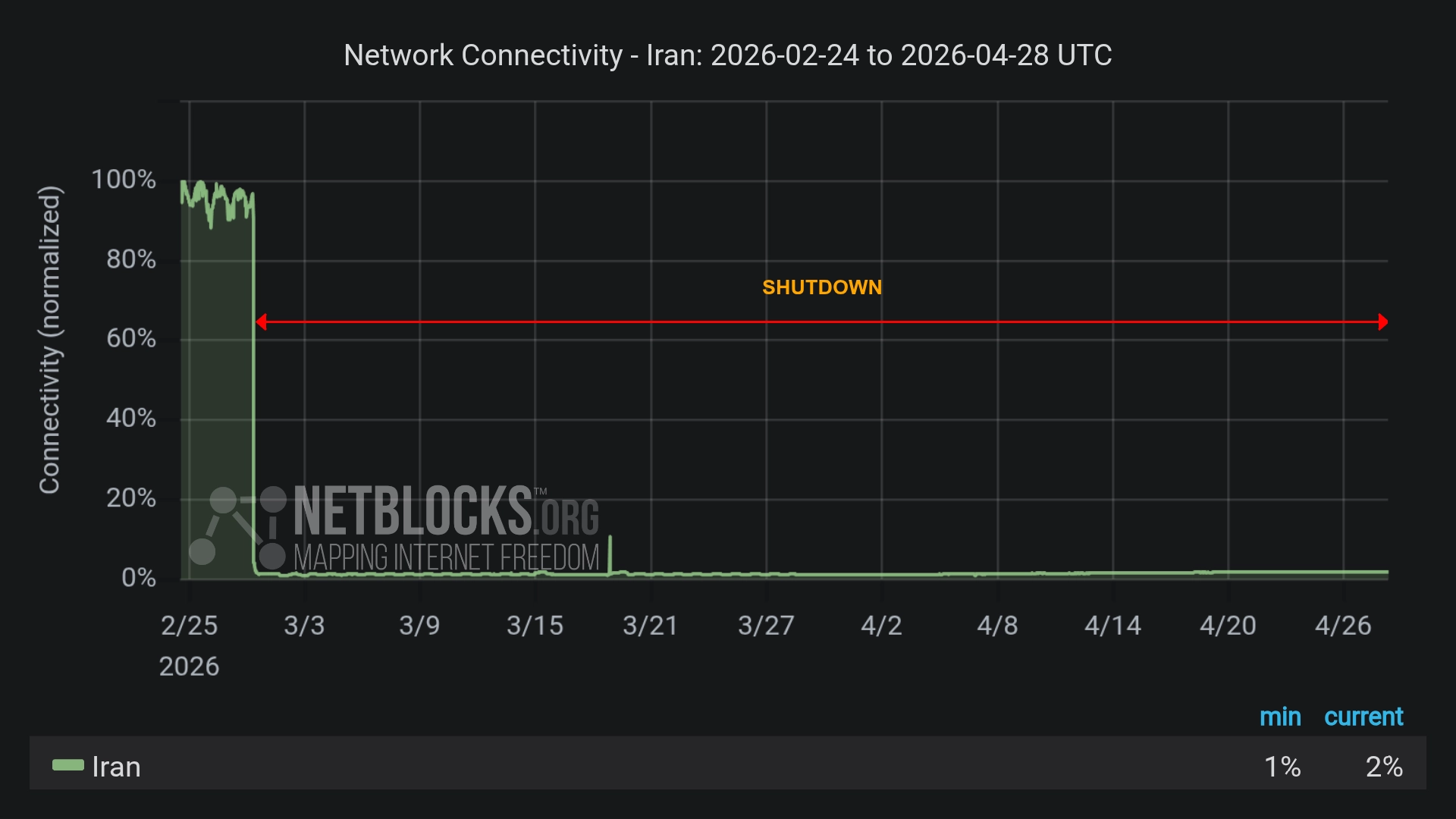 Iran’s Internet Blackout Hits 60 Days - Deepening Economic Crisis, Two-Tier Access
Iran’s Internet Blackout Hits 60 Days - Deepening Economic Crisis, Two-Tier Access U.S. Blocks Foreign-Made Routers Over Cybersecurity Fears
U.S. Blocks Foreign-Made Routers Over Cybersecurity Fears Iran Targeted by Self-Propagating Malware in Supply-Chain Cyberattacks
Iran Targeted by Self-Propagating Malware in Supply-Chain Cyberattacks Iranians Outsmart Internet Blackout to Broadcast Airstrikes
Iranians Outsmart Internet Blackout to Broadcast Airstrikes Iran Expands Digital Dragnet After Crushing Protests
Iran Expands Digital Dragnet After Crushing Protests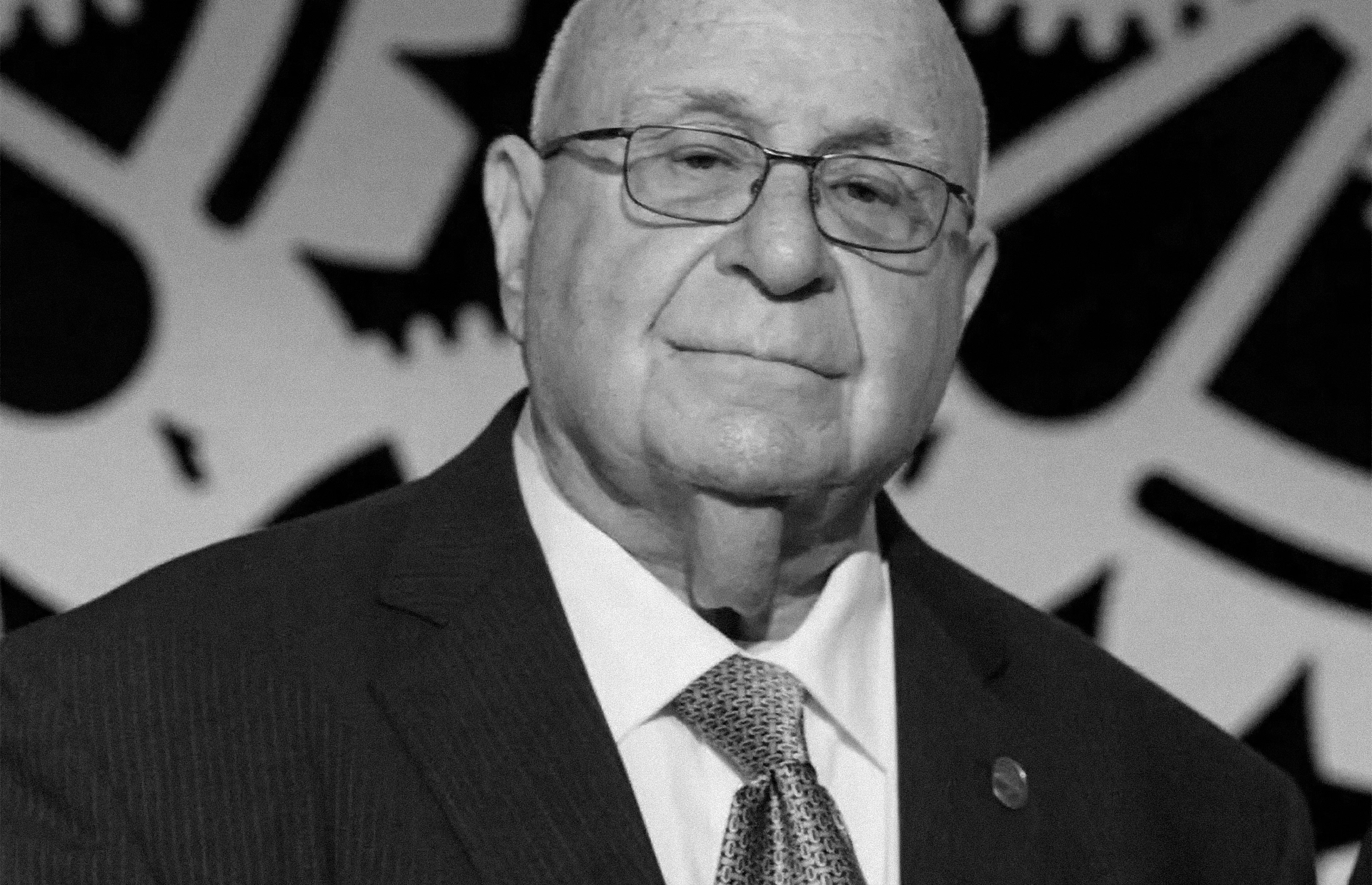 David J. Farber, Early Architect of the Internet, Dies at 91
David J. Farber, Early Architect of the Internet, Dies at 91