

 Domains and DNS underpin modern business operations, yet security gaps remain widespread. CSC's latest research shows why stronger domain protections are essential to resilience, helping companies reduce disruption, safeguard trust, and maintain continuity when attacks strike.
Domains and DNS underpin modern business operations, yet security gaps remain widespread. CSC's latest research shows why stronger domain protections are essential to resilience, helping companies reduce disruption, safeguard trust, and maintain continuity when attacks strike.
 New data on DNS abuse reveals most malicious domains remain active beyond 24 hours, while a handful of registrars host the bulk of infrastructure, leaving India's population of first-generation internet users uniquely exposed to fraud.
New data on DNS abuse reveals most malicious domains remain active beyond 24 hours, while a handful of registrars host the bulk of infrastructure, leaving India's population of first-generation internet users uniquely exposed to fraud.
 As AI agents automate phishing, impersonation and domain abuse at machine scale, the Brand Registry Group argues that dotBrand domains are evolving from marketing assets into trust infrastructure underpinning cybersecurity, identity and interactions across the internet.
As AI agents automate phishing, impersonation and domain abuse at machine scale, the Brand Registry Group argues that dotBrand domains are evolving from marketing assets into trust infrastructure underpinning cybersecurity, identity and interactions across the internet.
 As power grids depend on microsecond precision, states must treat time synchronization as sovereign infrastructure, hardening satellite, fiber and orbital defenses against hybrid attacks that could trigger catastrophic blackouts through resilient sovereign time defense frameworks.
As power grids depend on microsecond precision, states must treat time synchronization as sovereign infrastructure, hardening satellite, fiber and orbital defenses against hybrid attacks that could trigger catastrophic blackouts through resilient sovereign time defense frameworks.
 As AI reshapes the digital world, online safety depends on balancing smarter protection with growing risks. From cybersecurity to privacy concerns, understanding AI's role can help users stay secure, informed, and resilient online.
As AI reshapes the digital world, online safety depends on balancing smarter protection with growing risks. From cybersecurity to privacy concerns, understanding AI's role can help users stay secure, informed, and resilient online.
 As cross-border cyber enforcement falters, critics argue Article 19's DNS abuse framework prioritizes procedural purity over user protection, leaving courts too slow to counter AI-driven phishing, rapid-flux domains, and increasingly automated online threats.
As cross-border cyber enforcement falters, critics argue Article 19's DNS abuse framework prioritizes procedural purity over user protection, leaving courts too slow to counter AI-driven phishing, rapid-flux domains, and increasingly automated online threats.
 Fake recruitment websites exploiting India's young job seekers are proliferating, exposing millions to identity theft, financial fraud and malware while regulators, registrars and digital literacy programs struggle to keep pace with a growing labor market.
Fake recruitment websites exploiting India's young job seekers are proliferating, exposing millions to identity theft, financial fraud and malware while regulators, registrars and digital literacy programs struggle to keep pace with a growing labor market.
 Geofeed data, long reliant on unverifiable self-assertions, faces mounting security risks. Integrating RPKI could transform it into a trusted, cryptographically validated infrastructure, strengthening routing integrity, regulatory compliance, and digital sovereignty across an increasingly contested internet.
Geofeed data, long reliant on unverifiable self-assertions, faces mounting security risks. Integrating RPKI could transform it into a trusted, cryptographically validated infrastructure, strengthening routing integrity, regulatory compliance, and digital sovereignty across an increasingly contested internet.
 Unicorn firms lead in DNS-based security adoption, signaling technical maturity, while Global 2000 rely on enterprise registrars. Gaps in redundancy and brand protection expose supply chain risks as cyberattacks intensify across industries globally today.
Unicorn firms lead in DNS-based security adoption, signaling technical maturity, while Global 2000 rely on enterprise registrars. Gaps in redundancy and brand protection expose supply chain risks as cyberattacks intensify across industries globally today.
 Africa's cybersecurity failures stem less from sophisticated hackers than from insecure system design, weak governance and limited skills, leaving institutions exposed and shifting the challenge from external threats to internal accountability and resilience.
Africa's cybersecurity failures stem less from sophisticated hackers than from insecure system design, weak governance and limited skills, leaving institutions exposed and shifting the challenge from external threats to internal accountability and resilience.
 Africa's looming AI rules expose a deeper problem: foreign-controlled infrastructure, weak enforcement capacity and externally governed data flows are eroding digital sovereignty, leaving states unable to regulate, protect citizens or meet global obligations.
Africa's looming AI rules expose a deeper problem: foreign-controlled infrastructure, weak enforcement capacity and externally governed data flows are eroding digital sovereignty, leaving states unable to regulate, protect citizens or meet global obligations.
 A flawed abuse-response system shifts costs from perpetrators to intermediaries, overwhelming enforcement. The Trusted Notifier Network seeks to realign incentives, curb low-quality reporting, and restore efficiency by embedding trust, accountability, and cost redistribution.
A flawed abuse-response system shifts costs from perpetrators to intermediaries, overwhelming enforcement. The Trusted Notifier Network seeks to realign incentives, curb low-quality reporting, and restore efficiency by embedding trust, accountability, and cost redistribution.
 Threat intelligence is shifting from a passive feed to a core operational layer, helping infrastructure defenders connect fragmented signals, identify recurring attack patterns, and prioritise responses in an increasingly modular and fast-moving cybercrime ecosystem.
Threat intelligence is shifting from a passive feed to a core operational layer, helping infrastructure defenders connect fragmented signals, identify recurring attack patterns, and prioritise responses in an increasingly modular and fast-moving cybercrime ecosystem.
 A once-trusted internet protocol is showing its age. DNSXplore, a global DNSSEC archive, exposes weaknesses, improves diagnostics and nudges adoption, helping secure the cryptographic chain underpinning online trust.
A once-trusted internet protocol is showing its age. DNSXplore, a global DNSSEC archive, exposes weaknesses, improves diagnostics and nudges adoption, helping secure the cryptographic chain underpinning online trust.
 Bad actors are exploiting DNS with growing sophistication. New domains dominate threat infrastructure, daily user exposures are rising, and AI is accelerating attack creation, making DNS intelligence an increasingly critical early-warning system for modern cyber defence.
Bad actors are exploiting DNS with growing sophistication. New domains dominate threat infrastructure, daily user exposures are rising, and AI is accelerating attack creation, making DNS intelligence an increasingly critical early-warning system for modern cyber defence.
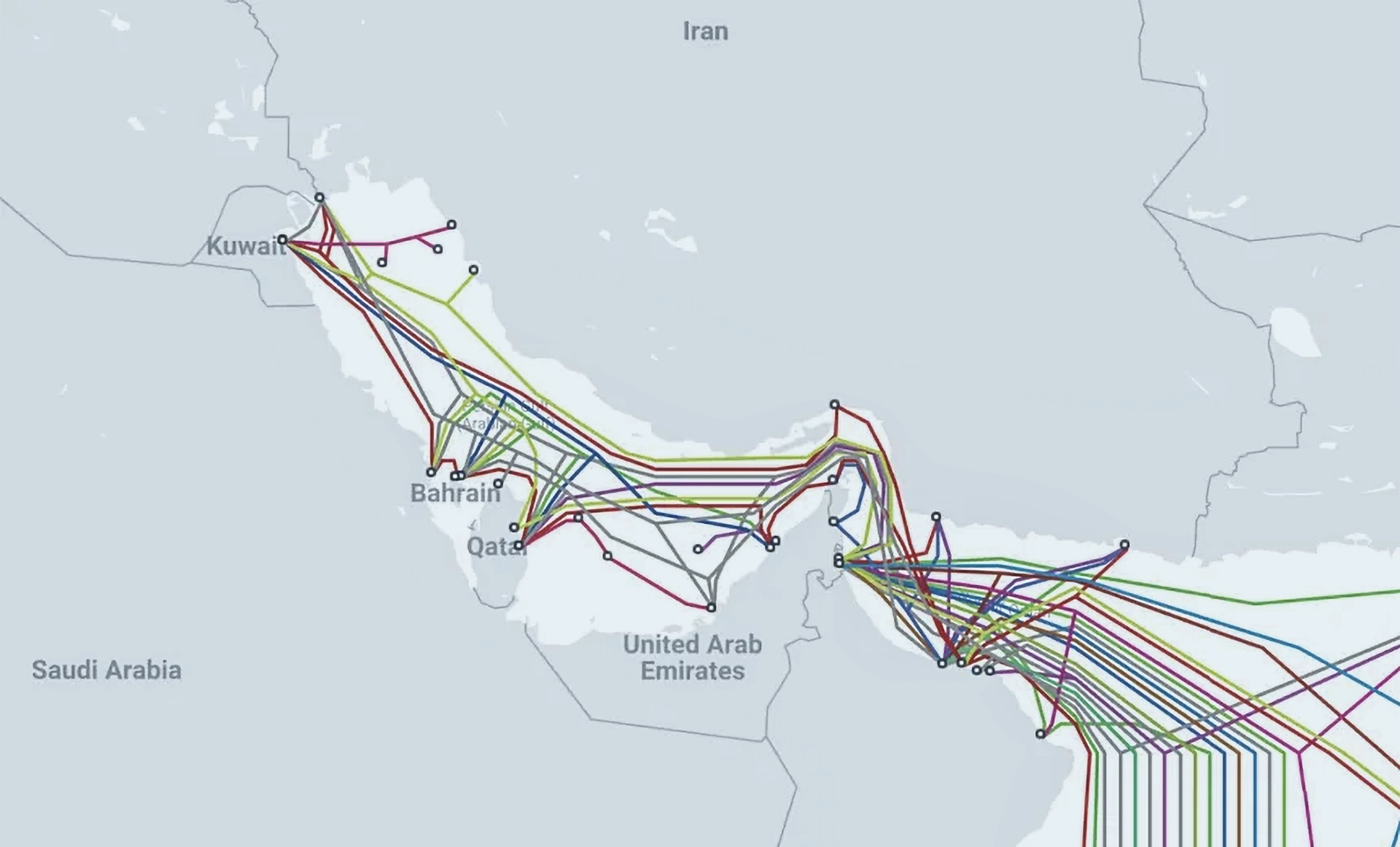 Iran Threatens Subsea Internet Cables in the Strait of Hormuz
Iran Threatens Subsea Internet Cables in the Strait of Hormuz Iran Targeted by Self-Propagating Malware in Supply-Chain Cyberattacks
Iran Targeted by Self-Propagating Malware in Supply-Chain Cyberattacks Backlash Over Potential Firing of U.S. Election Cybersecurity’s Top Official
Backlash Over Potential Firing of U.S. Election Cybersecurity’s Top Official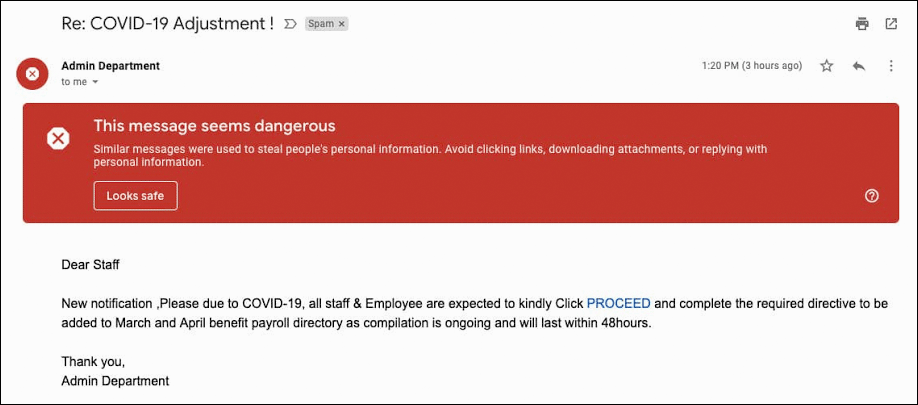 Google Reports 18 Million Daily COVID-19 Related Malware, Phishing Emails Per Day
Google Reports 18 Million Daily COVID-19 Related Malware, Phishing Emails Per Day Zoom Faces Class-Action Lawsuit, Accused of Overstating Its Privacy Standards
Zoom Faces Class-Action Lawsuit, Accused of Overstating Its Privacy Standards