

 As Africa digitises rapidly, control over data is emerging as a strategic contest. Foreign infrastructure dominance exposes economic and cybersecurity vulnerabilities, pushing governments to prioritise digital capability, regional cooperation, and stronger sovereignty over the systems powering the continent's future.
As Africa digitises rapidly, control over data is emerging as a strategic contest. Foreign infrastructure dominance exposes economic and cybersecurity vulnerabilities, pushing governments to prioritise digital capability, regional cooperation, and stronger sovereignty over the systems powering the continent's future.
 An ICANN-backed African internet-governance initiative exposed a deeper institutional problem: whether global coordinators must warn when regional policy processes drift into RIR governance, before facilitation, silence and funding harden into implied legitimacy for contested reforms.
An ICANN-backed African internet-governance initiative exposed a deeper institutional problem: whether global coordinators must warn when regional policy processes drift into RIR governance, before facilitation, silence and funding harden into implied legitimacy for contested reforms.
 Universal Acceptance Day 2026 marks progress toward a multilingual internet, as UNESCO and ICANN deepen cooperation. Yet unresolved implementation failures and weak registry stewardship still hinder truly inclusive digital access worldwide.
Universal Acceptance Day 2026 marks progress toward a multilingual internet, as UNESCO and ICANN deepen cooperation. Yet unresolved implementation failures and weak registry stewardship still hinder truly inclusive digital access worldwide.
 Fake recruitment websites exploiting India's young job seekers are proliferating, exposing millions to identity theft, financial fraud and malware while regulators, registrars and digital literacy programs struggle to keep pace with a growing labor market.
Fake recruitment websites exploiting India's young job seekers are proliferating, exposing millions to identity theft, financial fraud and malware while regulators, registrars and digital literacy programs struggle to keep pace with a growing labor market.
 This essay argues that Internet governance has drifted from technical coordination into unaccountable institutional power, and proposes "Running-Code Primacy" as a post-RIR framework grounded in distributed validation, interoperability, and voluntary adoption rather than registry authority.
This essay argues that Internet governance has drifted from technical coordination into unaccountable institutional power, and proposes "Running-Code Primacy" as a post-RIR framework grounded in distributed validation, interoperability, and voluntary adoption rather than registry authority.
 Geopolitical fragmentation is colliding with the internet's distributed architecture, exposing how sovereign cloud concentration and AI infrastructure can weaken resilience, amplify strategic vulnerabilities, and challenge whether governance can preserve interoperability while managing dependency under stress.
Geopolitical fragmentation is colliding with the internet's distributed architecture, exposing how sovereign cloud concentration and AI infrastructure can weaken resilience, amplify strategic vulnerabilities, and challenge whether governance can preserve interoperability while managing dependency under stress.
 As states chase digital sovereignty through clouds, AI and localized infrastructure, the internet's globally coordinated foundations reveal a harder truth: operational continuity depends less on control than on interoperable systems built on trust and governance.
As states chase digital sovereignty through clouds, AI and localized infrastructure, the internet's globally coordinated foundations reveal a harder truth: operational continuity depends less on control than on interoperable systems built on trust and governance.
 Missile strikes on Gulf data centres exposed a deeper contradiction at the heart of digital sovereignty: governments seek territorial control over internet infrastructure whose resilience still depends upon globally distributed coordination and interdependence across borders.
Missile strikes on Gulf data centres exposed a deeper contradiction at the heart of digital sovereignty: governments seek territorial control over internet infrastructure whose resilience still depends upon globally distributed coordination and interdependence across borders.
 Recent court rulings in Europe and America are reshaping access to technical standards, weakening paywalls and strengthening the principle that publicly mandated knowledge belongs to citizens, regulators and increasingly AI systems that depend on machine-readable information.
Recent court rulings in Europe and America are reshaping access to technical standards, weakening paywalls and strengthening the principle that publicly mandated knowledge belongs to citizens, regulators and increasingly AI systems that depend on machine-readable information.
 As AFRINIC rebuilds after years of litigation, the Number Resource Society is urging members to sign powers of attorney, raising fears that coordinated advocacy, commercial interests and geopolitical pressures could reshape African control over critical internet resources.
As AFRINIC rebuilds after years of litigation, the Number Resource Society is urging members to sign powers of attorney, raising fears that coordinated advocacy, commercial interests and geopolitical pressures could reshape African control over critical internet resources.
 As cross-border enforcement falters, dynamic injunctions are reshaping internet governance, allowing authorities to update blocking lists in real time and prioritize access deterrence over slow, often futile source takedowns across fragmented global legal regimes.
As cross-border enforcement falters, dynamic injunctions are reshaping internet governance, allowing authorities to update blocking lists in real time and prioritize access deterrence over slow, often futile source takedowns across fragmented global legal regimes.
 Africa's digital boom is accelerating, but safeguards lag. Governments and firms deploy systems at speed, while weak enforcement and fragmented oversight leave economies exposed to mounting cyber risks.
Africa's digital boom is accelerating, but safeguards lag. Governments and firms deploy systems at speed, while weak enforcement and fragmented oversight leave economies exposed to mounting cyber risks.
 April's satellite sector saw Amazon's $10.8bn Globalstar bid, surging plans for orbital data centres, intensifying SpaceX rivalry, regulatory friction, and doubts over broadband promises, underscoring a crowded, contested race to control next-generation connectivity infrastructure global.
April's satellite sector saw Amazon's $10.8bn Globalstar bid, surging plans for orbital data centres, intensifying SpaceX rivalry, regulatory friction, and doubts over broadband promises, underscoring a crowded, contested race to control next-generation connectivity infrastructure global.
 Africa's internet governance faces parallel tracks as AFRINIC's community-led reforms unfold alongside a continent-wide blueprint, raising questions over whether legitimacy will stem from participatory processes or increasingly coordinated external alignment.
Africa's internet governance faces parallel tracks as AFRINIC's community-led reforms unfold alongside a continent-wide blueprint, raising questions over whether legitimacy will stem from participatory processes or increasingly coordinated external alignment.
 Jan Žorž reflects on SEE RIPE's role in uniting a fragmented region, where trust built through informal exchange now underpins internet resilience and helps align engineers with policymakers as regulatory pressures intensify.
Jan Žorž reflects on SEE RIPE's role in uniting a fragmented region, where trust built through informal exchange now underpins internet resilience and helps align engineers with policymakers as regulatory pressures intensify.
 Inside Iran’s Shift From Internet Shutdowns to Tiered Connectivity
Inside Iran’s Shift From Internet Shutdowns to Tiered Connectivity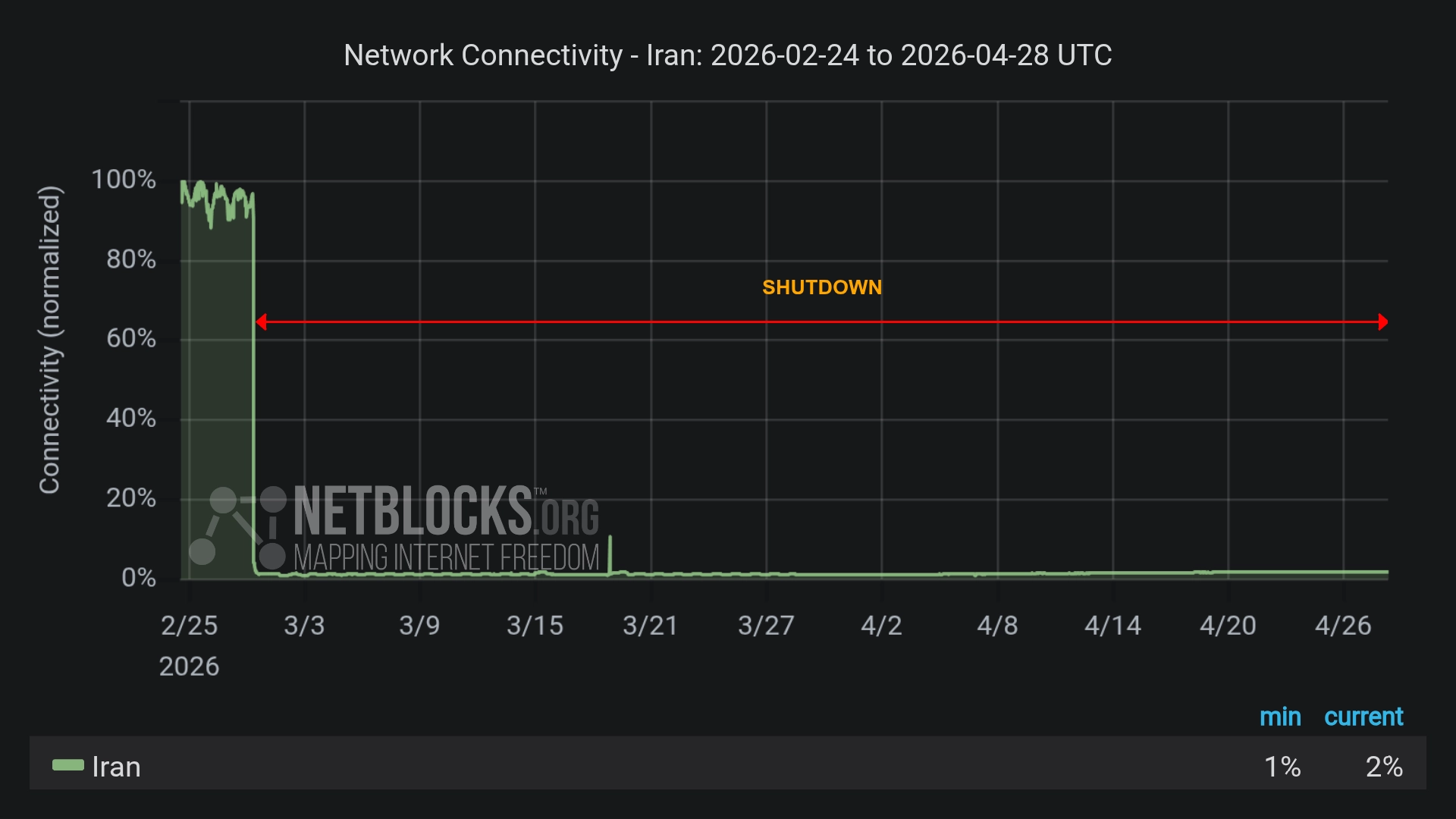 Iran’s Internet Blackout Hits 60 Days - Deepening Economic Crisis, Two-Tier Access
Iran’s Internet Blackout Hits 60 Days - Deepening Economic Crisis, Two-Tier Access U.S. Blocks Foreign-Made Routers Over Cybersecurity Fears
U.S. Blocks Foreign-Made Routers Over Cybersecurity Fears US Senators Move to Shield Undersea Internet Cables from Global Threats
US Senators Move to Shield Undersea Internet Cables from Global Threats Digital Rights Defender Steps Aside: Cindy Cohn to Leave EFF After 25 Years
Digital Rights Defender Steps Aside: Cindy Cohn to Leave EFF After 25 Years Chat Control Proposal Advances Despite Rising Opposition in Europe
Chat Control Proposal Advances Despite Rising Opposition in Europe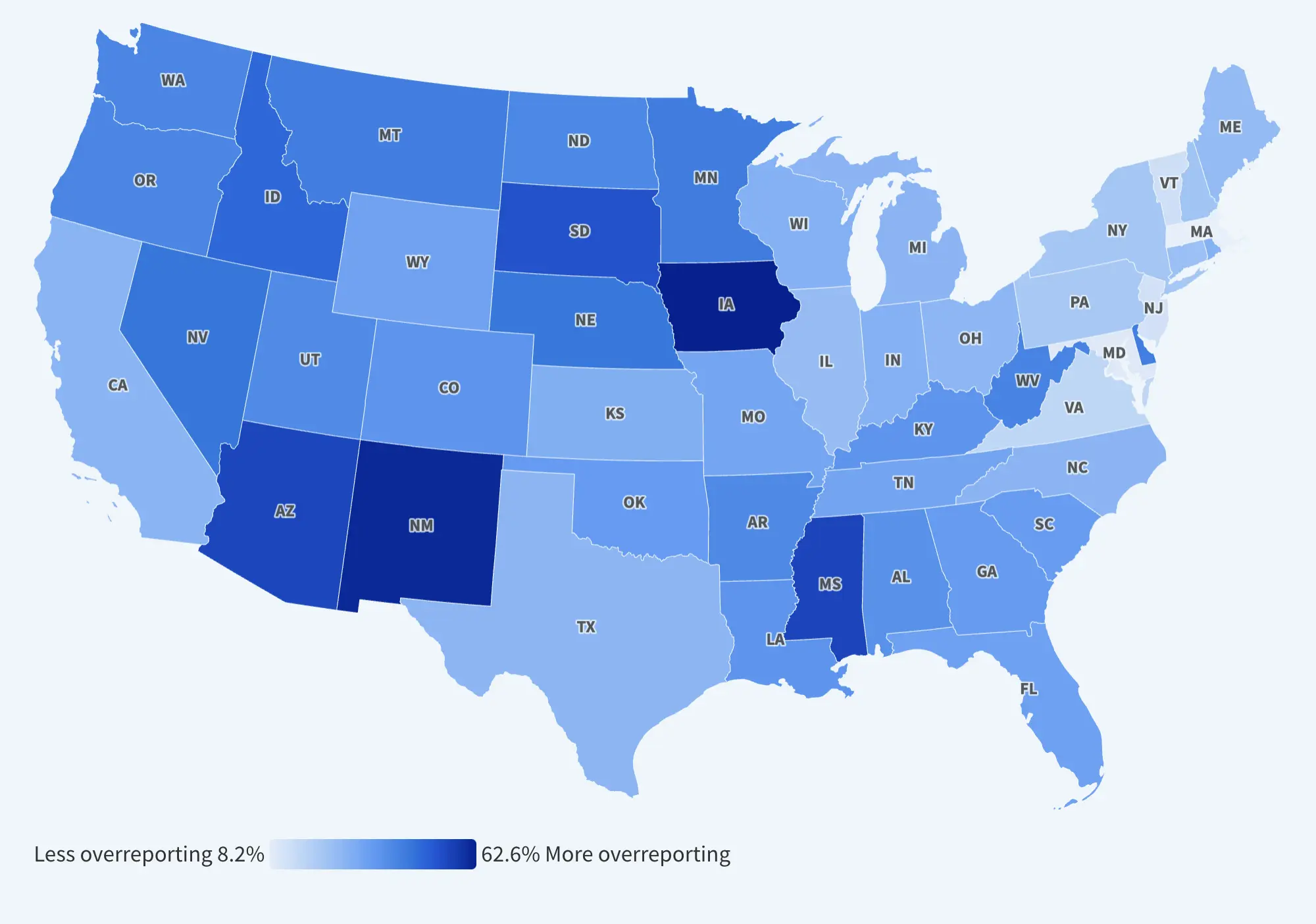 America’s Broadband Blind Spot: Audit Reveals Millions More Offline Than FCC Reports
America’s Broadband Blind Spot: Audit Reveals Millions More Offline Than FCC Reports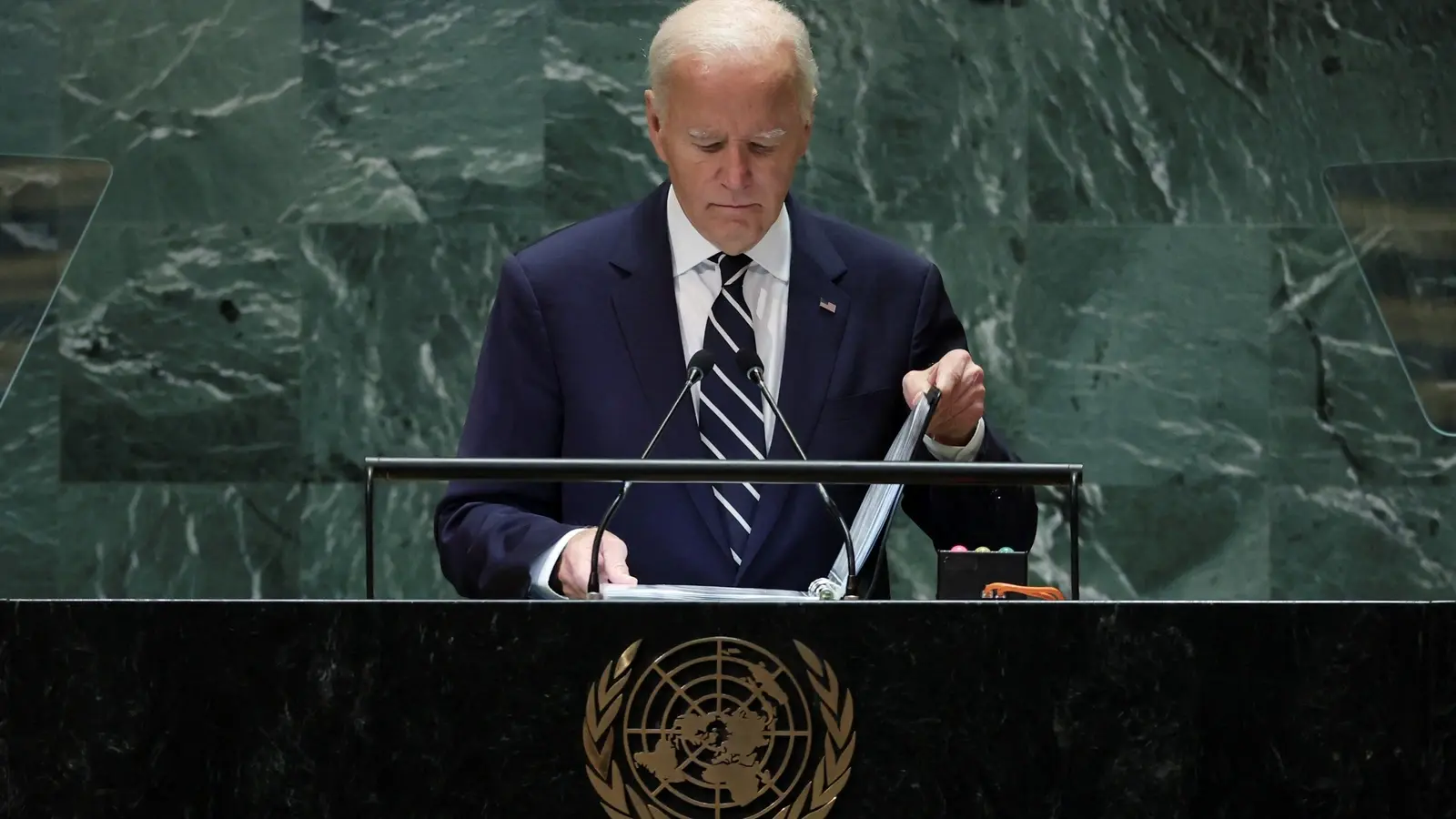 Biden Administration to Back UN Cybercrime Treaty Amid Controversy
Biden Administration to Back UN Cybercrime Treaty Amid Controversy EU Internet Advocates Push Back Against Telecom “Fair-Share” Fees
EU Internet Advocates Push Back Against Telecom “Fair-Share” Fees