

|
||
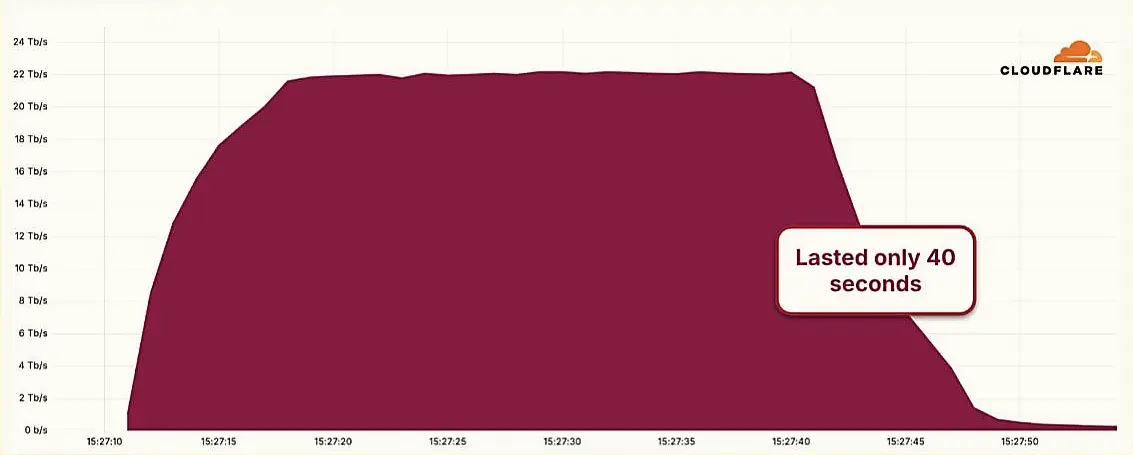
A distributed denial-of-service (DDoS) attack has redefined the upper bounds of volumetric assault, briefly peaking at 22.2 terabits per second (Tbps) and 10.6 billion packets per second (Bpps). Though lasting only 40 seconds, the incident, reported by Cloudflare, represents a structural escalation in the scale, precision, and automation of denial-of-service tactics.
Attack method: The target, a European network infrastructure provider, was subjected to a UDP-based carpet bombing campaign—an increasingly common method in which multiple ports on a single host are saturated simultaneously. This particular attack targeted an average of 31,000 destination ports per second, peaking at 47,000, making it both a volumetric and port exhaustion event.
Analysis points to the Aisuru botnet, which leverages large swathes of compromised IoT devices—routers, digital video recorders, and other embedded systems—many of which are exploitable via known CVEs or unpatched zero-days. The attack traffic was traced to over 404,000 unique, non-spoofed IPs across 14 autonomous system numbers (ASNs), suggesting a well-coordinated botnet with high geographic distribution and sufficient command-and-control efficiency.
Capability shift: While volumetric DDoS attacks are not novel, this event marks a qualitative shift in attacker capabilities. At over twice the size of the previously recorded peak (11.5 Tbps), the assault likely reflects both advances in botnet orchestration and growing aggregate bandwidth available to compromised nodes, particularly in residential and small-office networks connected via fibre.
Cybersecurity researchers warn that such hyper-volumetric attacks are increasingly employed not as standalone events, but as part of composite threat operations—either as diversionary tactics during data exfiltration or as probes for broader infrastructure mapping.
Sponsored byWhoisXML API

Sponsored byIPv4.Global

Sponsored byCSC

Sponsored byVerisign

Sponsored byVerisign

Sponsored byDNIB.com

Sponsored byRadix
