


|
||
|
||
The Hacker News reported that the alleged leader of the BlackBasta Ransomware Gang, 35-year-old Russian national Oleg Evgenievich Nefedov, has been added to the EU’s Most Wanted and INTERPOL’s Red Notice lists.
Over time, Black Basta affiliates have become known for using common initial access techniques like phishing and exploiting known vulnerabilities and then employing a double-extortion model. They not only encrypted systems but also exfiltrated data. In addition, their ransom notes did not generally include initial ransom demands or payment instructions. Instead, these provided victims with unique codes and instructed them to contact the ransomware group via a .onion URL reachable through the Tor browser. The actors typically gave victims 10—12 days to pay the ransom before they published the stolen data on the Black Basta TOR site dubbed “Basta News.”
Security researchers publicized 27 network IoCs related to one of the most recent Black Basta campaigns. We analyzed 18 of these IoCs and uncovered these findings:
Note that we focused on only three of the 12 domains the researchers identified as IoCs after checking their legitimacy and current state of responsiveness via Jake AI. We did, however, keep the list of 15 IP addresses tagged as IoCs as is.
A sample of the additional artifacts obtained from our analysis is available for download from our website.
As mentioned earlier, we zoomed in on three domains identified as IoCs in our analysis. Our WHOIS API queries for them revealed that:
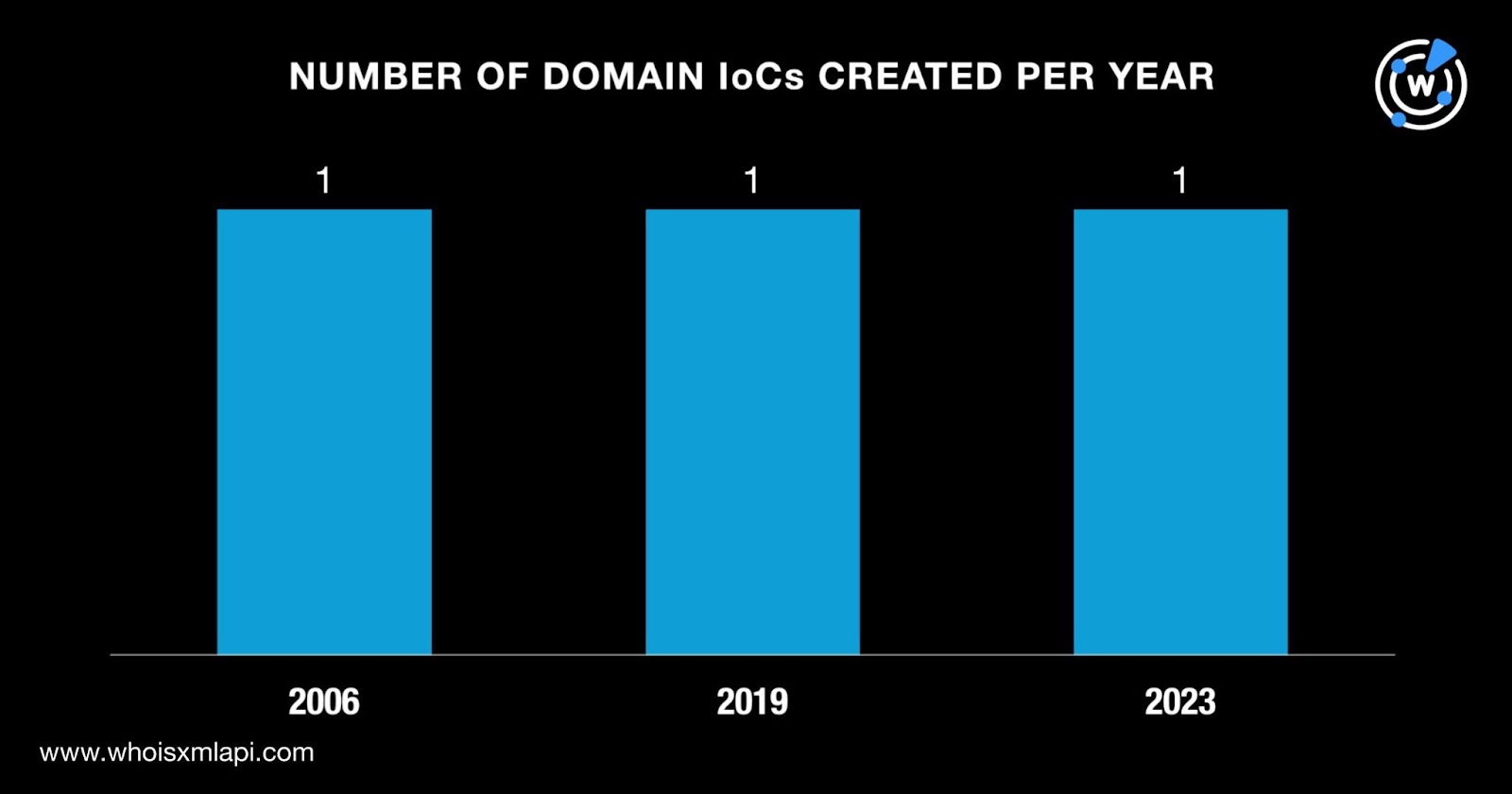
Each of them was administered by a different registrar.
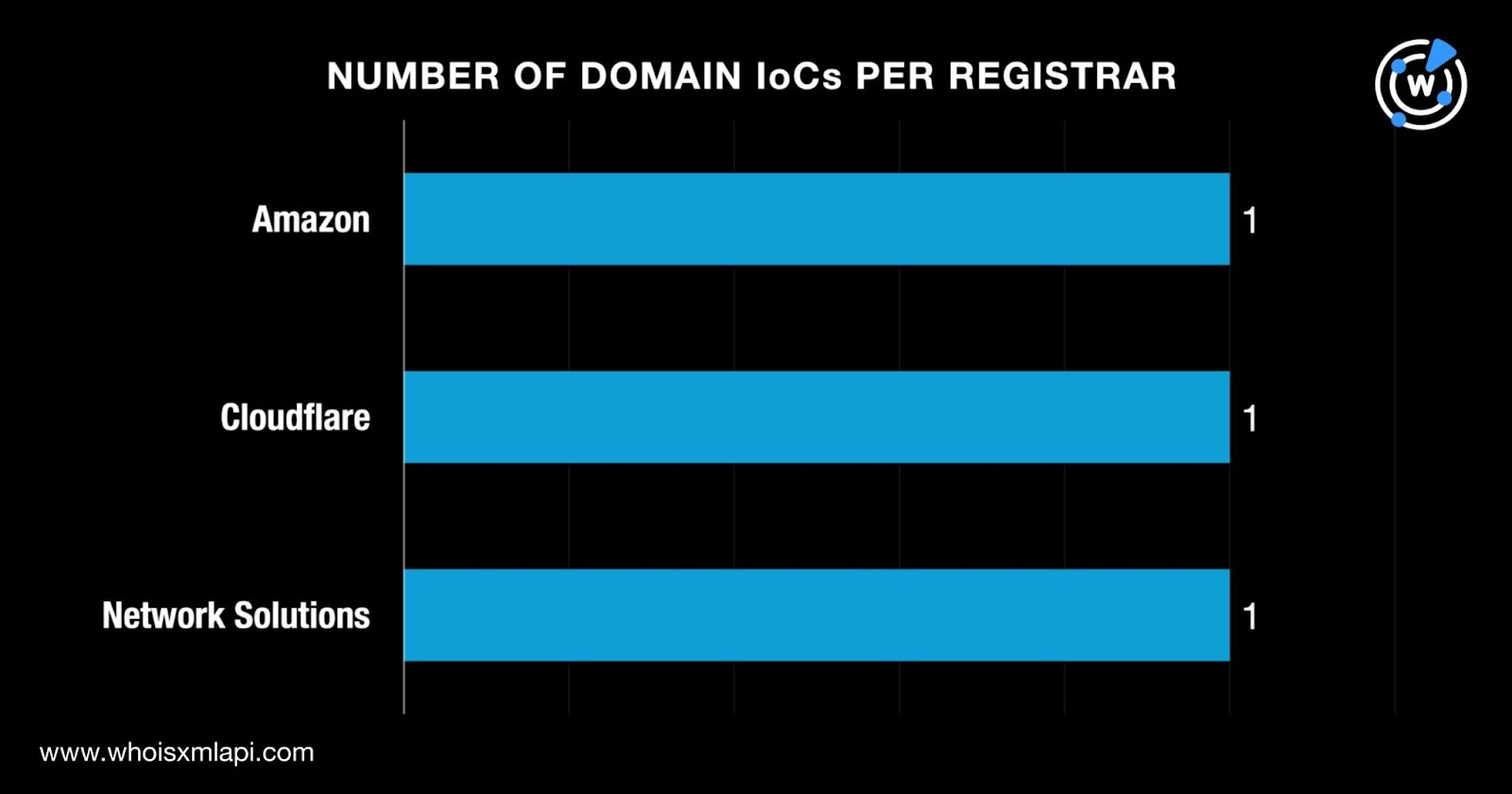
And similarly, they were registered in three different countries.
DNS Chronicle API queries for the three domains tagged as IoCs showed that together, they recorded 418 domain-to-IP resolutions over time. The domain vulnerableapp[.]com posted the oldest resolution on 7 February 2017. It also recorded 301 resolutions until 18 January 2026.
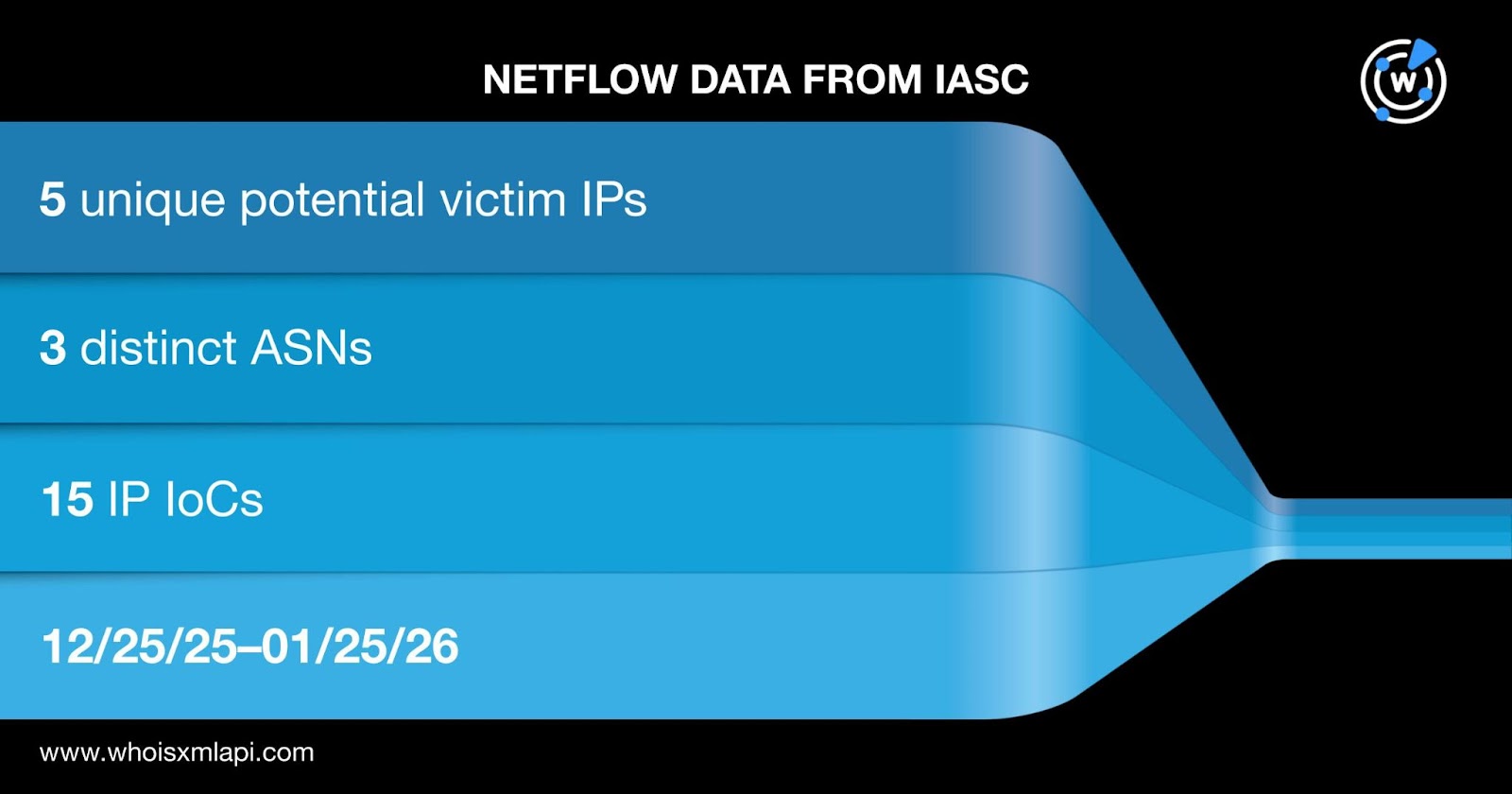
Sample network traffic data from the IASC revealed that five unique potential victim IP addresses under three distinct ASNs communicated with the 15 IP addresses identified as IoCs between 25 December 2025 and 25 January 2026.
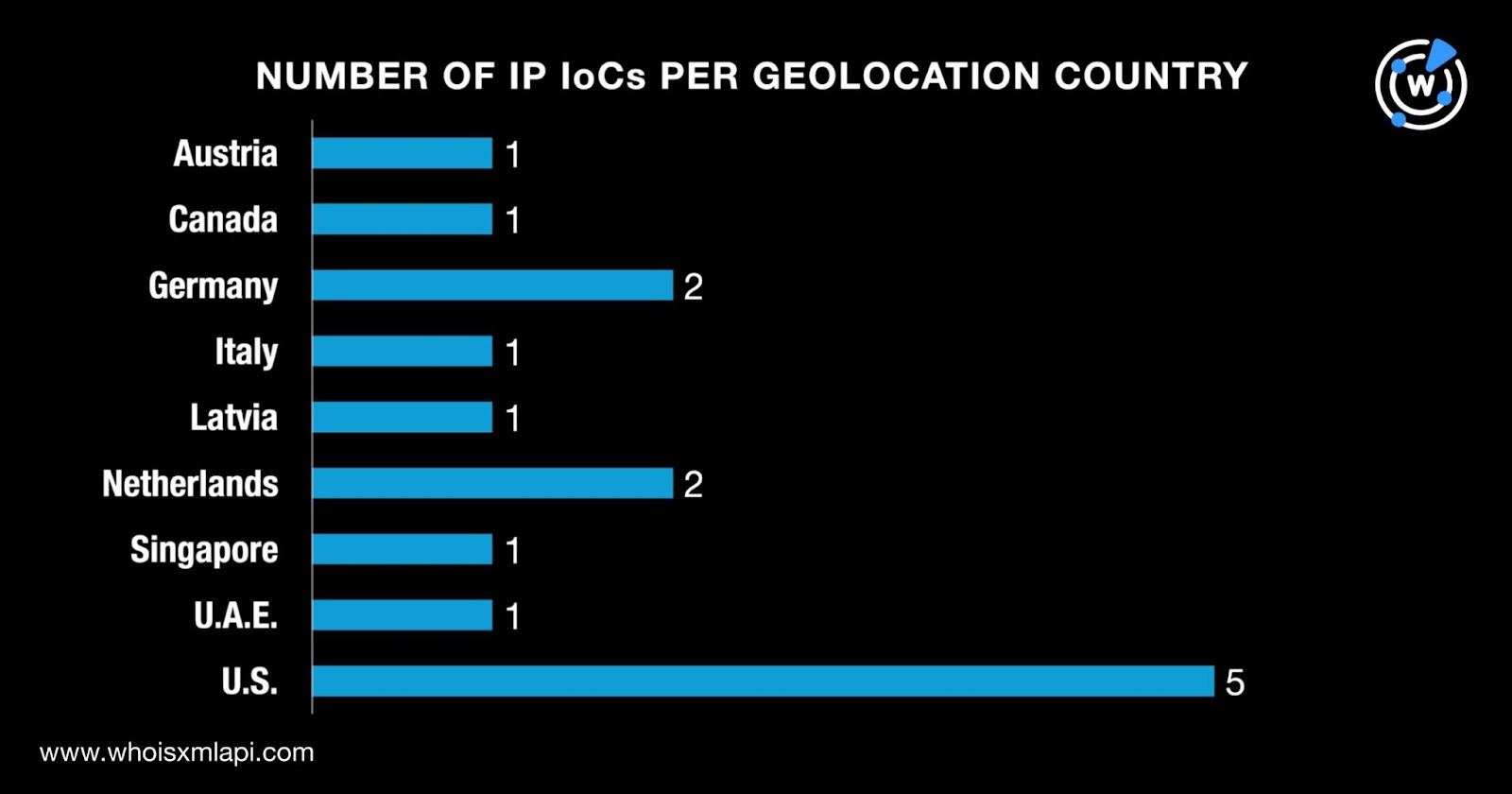
We then queried the 15 IP addresses tagged as IoCs on Bulk IP Geolocation Lookup and discovered that:
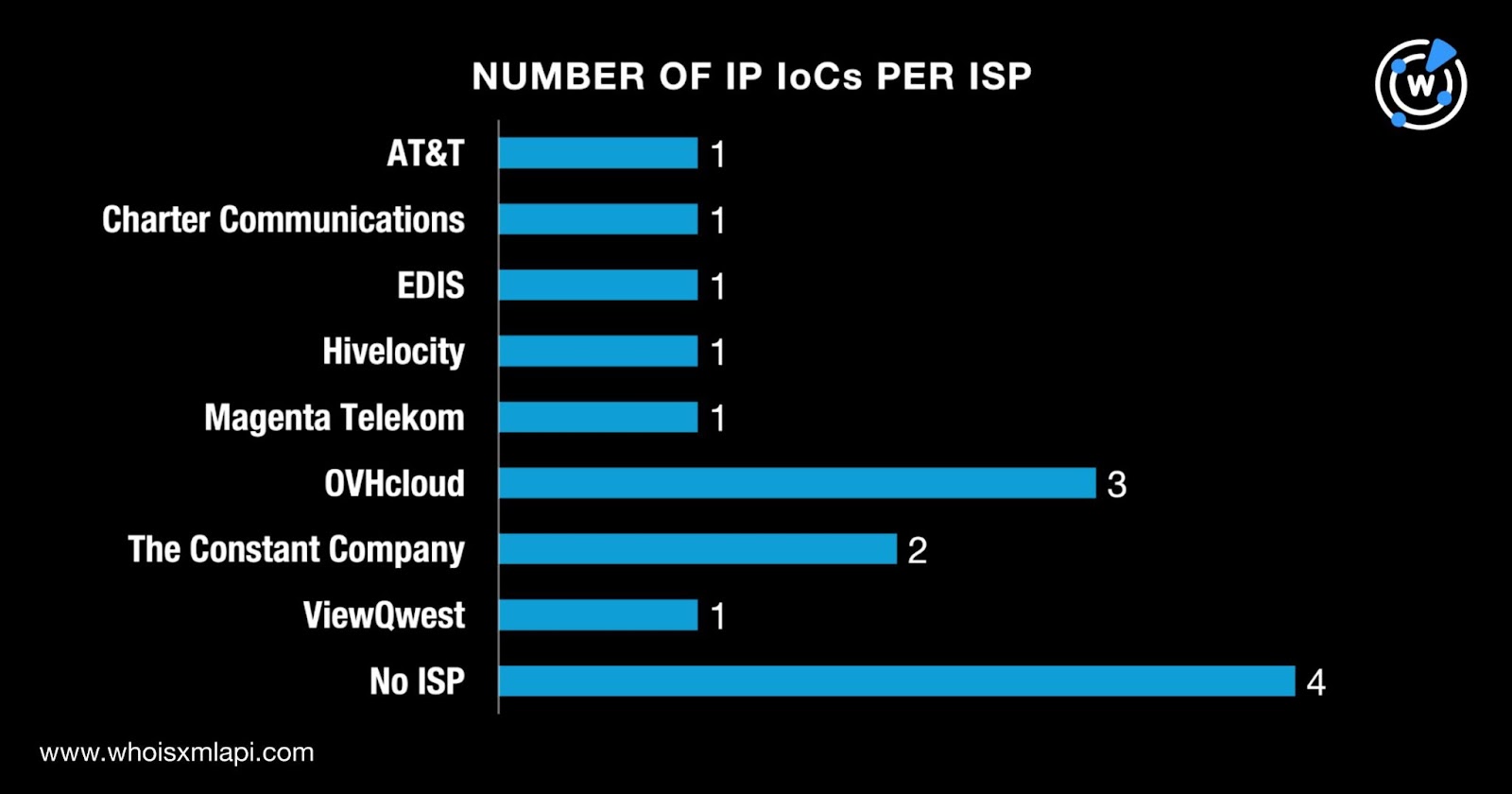
And while four of them did not have ISPs on record, the remaining 11 were administered by eight different ISPs.
Next, we queried the 15 IP addresses identified as IoCs on DNS Chronicle API and found out that 14 of them recorded 3,722 IP-to-domain resolutions over time.
| IP IoC | NUMBER OF RESOLUTIONS | FIRST RESOLUTION DATE | LAST RESOLUTION DATE |
|---|---|---|---|
| 104[.]187[.]107[.]81 | 258 | 02/04/17 | 01/17/26 |
| 213[.]47[.]213[.]243 | 1,000 | 02/05/17 | 12/13/19 |
| 92[.]97[.]159[.]185 | 341 | 02/05/17 | 07/21/25 |
| 76[.]80[.]4[.]222 | 333 | 02/06/17 | 10/07/25 |
| 91[.]204[.]248[.]6 | 213 | 03/15/19 | 01/20/26 |
While the IP address 104[.]187[.]107[.]81 posted the oldest first resolution on 4 February 2017, the IP address 213[.]47[.]213[.]243 recorded the highest number of resolutions at 1,000. It is also interesting to note that four of the IP addresses identified as IoCs first resolved domains within days of each other.
To uncover new artifacts, we first queried the three domains tagged as IoCs on WHOIS History API and learned that together, they had 63 unique email addresses in their historical WHOIS records. Careful scrutiny, however, revealed that only two were public email addresses.
Reverse WHOIS API queries for the two email addresses showed that both appeared in the historical WHOIS records of various domains. This step led to the discovery of 7,560 unique email-connected domains after those already identified as IoCs were filtered out.
The results of our Threat Intelligence API queries for the email-connected domains revealed that 482 have already been weaponized for various attacks.
| MALICIOUS EMAIL-CONNECTED DOMAIN | ASSOCIATED THREAT | DATES SEEN |
|---|---|---|
| bevgfijycd[.]net | Malware distributionC&C | 03/09/23–01/25/2603/09/23–01/25/26 |
| bndduftnfteu[.]com | Malware distributionC&C | 03/09/23–01/25/2603/09/23–01/25/26 |
| btpnxlsfdqbhzazyx[.]net | Malware distributionC&C | 03/09/23–01/25/2603/09/23–01/24/26 |
| bwoslmylnsrr[.]biz | Malware distributionC&C | 03/09/23–01/25/2603/09/23–01/24/26 |
| cgbbwfffnvgh[.]com | Malware distributionC&C | 03/09/23–01/25/2603/09/23–01/24/26 |
It is worth noting that several of the malicious email-connected domains not only resembled one another in terms of makeup (likely created using a DGA) but were also detected as malicious on the same date—9 March 2023.
We then queried the three domains identified as IoCs on DNS Lookup API and found out that they resolved to two unique IP addresses that were not part of the IoC list.
This post only contains a snapshot of the full research. Download the complete findings and a sample of the additional artifacts on our website or contact us to discuss your intelligence needs for threat detection and response or other cybersecurity use cases.
Disclaimer: We take a cautionary stance toward threat detection and aim to provide relevant information to help protect against potential dangers. Consequently, it is possible that some entities identified as “threats” or “malicious” may eventually be deemed harmless upon further investigation or changes in context. We strongly recommend conducting supplementary investigations to corroborate the information provided herein.
Sponsored byRadix

Sponsored byWhoisXML API

Sponsored byCSC

Sponsored byVerisign

Sponsored byVerisign

Sponsored byDNIB.com

Sponsored byIPv4.Global
