


|
||
|
||
Securelist recently uncovered a new HoneyMyte (also known as “Mustang Panda” or “Bronze President”) campaign leveraging an updated version of CoolClient. The group has been known to use various sophisticated tools like ToneShell, PlugX, Qreverse, CoolClient, Tonedisk, and SnakeDisk, among others.
In 2025, HoneyMyte updated the CoolClient backdoor, adding new features like deploying several browser login data stealers and using multiple data theft and reconnaissance scripts.
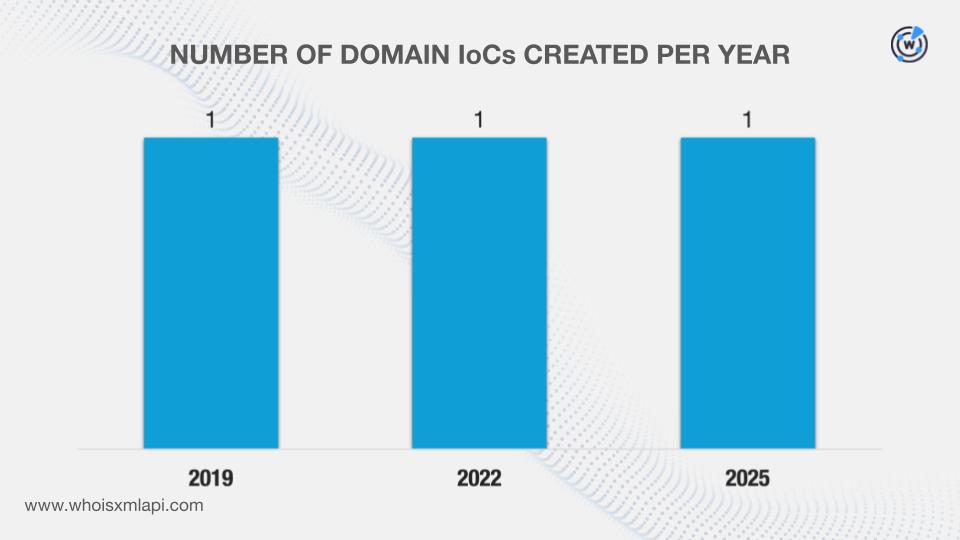
The researchers originally identified four CoolClient network IoCs. After more careful scrutiny (extracting domains from the subdomains and weeding out legitimate ones), we ended up with six IoCs in all comprising three domains, two subdomains, and one IP address. We then verified the legitimacy of the three domains tagged as IoCs aided by the WhoisXML API MCP Server and discovered that none of them were owned by legitimate entities.
Our in-depth investigation of the CoolClient IoCs led to these findings:
A sample of the additional artifacts obtained from our analysis is available for download from our website.
We began our investigation by analyzing the two subdomains identified as IoCs through our MCP server. We discovered that while there was not much to tell about one of them, we learned that the subdomain japan[.]lenovoappstore[.]com may be worth avoiding due to its use of a major brand name despite its illegitimacy (it does not belong to Lenovo) and lack of a live website that could suggest its ties to phishing or other malicious activities.
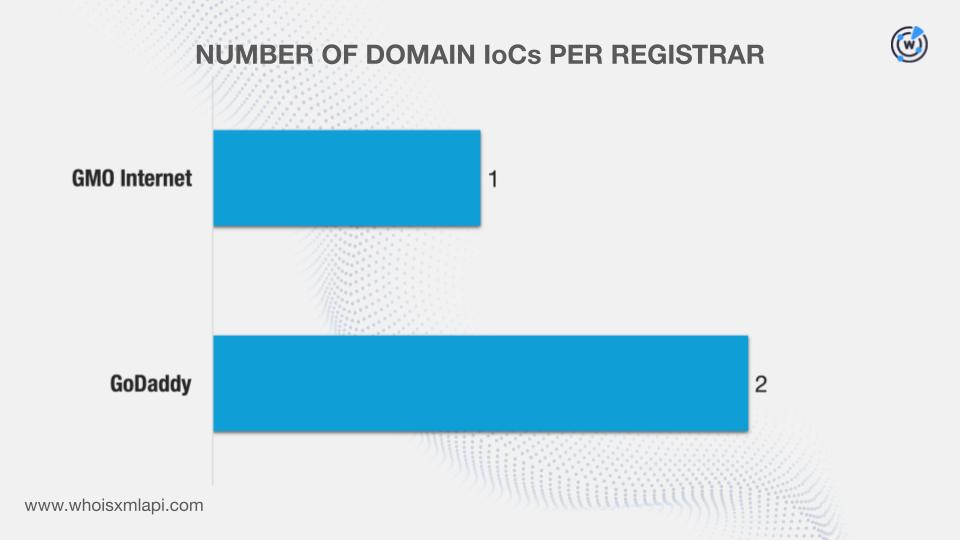
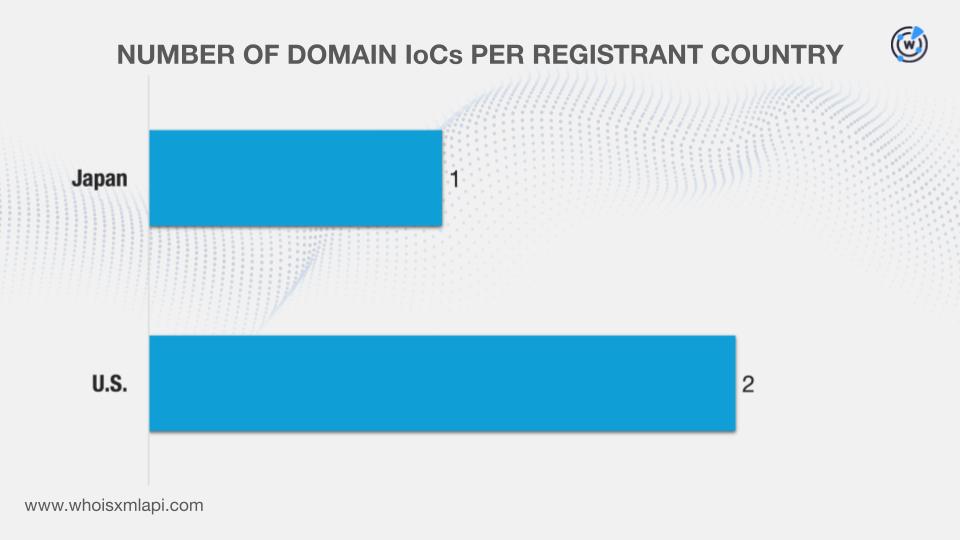
We queried the three domains identified as IoCs on WHOIS API and discovered that:
They were administered by two registrars.
They were registered in two countries.
DNS Chronicle API queries for the three domains tagged as IoCs showed that they recorded 213 historical domain-to-IP resolutions over time. The domain lenovoappstore[.]com, for instance, posted 131 resolutions from 30 April 2020 to 6 September 2025.
We queried the sole IP address identified as an IoC on IP Geolocation API and discovered that it was geolocated in Malaysia under the purview of ISP Extreme Broadband.
A DNS Chronicle API query for the IP address, meanwhile, revealed that it has recorded 146 IP-to-domain resolutions between 5 February 2017 and 14 May 2021.
To uncover new potentially connected artifacts, we queried the three domains identified as IoCs on WHOIS History API. We found out that two of them had two unique email addresses in their historical WHOIS records. Further scrutiny showed that one of them was a public email address.
A Reverse WHOIS API query for the public email address led to the discovery of 57 unique email-connected domains after those already tagged as IoCs were filtered out.
Next, we queried the three domains named as IoCs on DNS Lookup API and discovered that one of them resolved to an IP address that differed from the one already classified as an IoC.
A Threat Intelligence API query for the additional IP address revealed that it has been associated with malware distribution from 14—15 February 2026 that, interestingly, coincides with much-celebrated Valentine’s Day.
An IP Geolocation API query, meanwhile, for the additional IP address revealed that it was geolocated in Japan under the administration of NTT Communications Corporation (OCN).
After that last step, we now had two IP addresses for further investigation. Reverse IP API queries for them showed that one could be a dedicated host. We collated five unique IP-connected domains after those already classified as IoCs and the email-connected domains were filtered out.
This post only contains a snapshot of the full research. Download the complete findings and a sample of the additional artifacts on our website or contact us to discuss your intelligence needs for threat detection and response or other cybersecurity use cases.
Disclaimer: We take a cautionary stance toward threat detection and aim to provide relevant information to help protect against potential dangers. Consequently, it is possible that some entities identified as “threats” or “malicious” may eventually be deemed harmless upon further investigation or changes in context. We strongly recommend conducting supplementary investigations to corroborate the information provided herein.
Sponsored byRadix

Sponsored byVerisign

Sponsored byVerisign

Sponsored byCSC

Sponsored byIPv4.Global

Sponsored byDNIB.com

Sponsored byWhoisXML API
