


|
||
|
||
Picus Security, in Red Report 2026, identified the top 10 MITRE ATT&CK techniques in 2025 and named some of the groups that employed them. We zoomed in on 11 attacks featured in their report for six of the 10 ATT&CK techniques with their corresponding subtechniques where applicable in hopes of gathering more insights and collating additional artifacts.
| MITRE ATT&CK TECHNIQUE/SUBTECHNIQUE ABUSED | THREAT/ACTOR | THREAT/GROUP |
|---|---|---|
| T1036 Masquerading T1036.008 Masquerade File Type | UNC6384 abused file typemasquerading to deliver STATICPLUGIN to diplomatic targets’ systems | STATICPLUGIN |
| T1055 Process Injection T1055.004 Asynchronous Procedure Call | SadBridge Loader used APC injection as a key technique to execute malicious code within a legitimate process | SadBridge Loader |
| T1055 Process Injection T1055.004 Asynchronous Procedure Call | XLoader 6 and 7 used APC injection to execute their payloads within legitimate processes | XLoader 6 and 7 |
| T1055 Process Injection T1055.003 Thread Execution Hijacking | NoisyBear used execution hijacking in Operation BarrelFire to run its payload under trusted processes | Operation BarrelFire |
| T1055 Process Injection T1055.002 Portable Executable Injection | ClickFix used PE injection to execute its finalpayload entirely in memory | ClickFix |
| T1059 Command and Scripting Interpreter T1059.006 Python | APT36 or Transparent Tribe demonstrated a significant evolution in their capabilities with the Python-based ELF malware | APT36 Python-Based ELF Malware |
| T1059 Command and Scripting Interpreter T1059.001 PowerShell | Chihuahua Stealer launched a compact PowerShell command that decoded a Base64 payload, executing it in memory | Chihuahua Stealer |
| T1555 Credentials from Password Stores T1555.004 Windows Credential Manager | Earth Ammit enumerated credentials saved on compromised systems | Earth Ammit |
| T1562 Impair Defenses T1562.004 Disable or Modify System Firewall | Cryptojacking campaign leveraged Docker Swarm and Kubernetes for attack | Docker Swarm and Kubernetes Attack |
| T1562 Impair Defenses T1562.004 Disable or Modify System Firewall | PlushDaemon used the Ruler system to dynamically modify iptables firewall rules to intercept and manipulate networktraffic on compromised systems | PlushDaemon |
| T1486 Data Encrypted for Impact | Earth Alux queried the MachineGUID value from the Windows Registry to serve as a persistent, unique identifier for each target host | Earth Alux |
We obtained a total of 147 network IoCs from the abovementioned 11 analyses referenced in the report.
| THREAT/GROUP | IoCs ANALYZED |
|---|---|
| STATICPLUGIN | Domain: 1 IPs: 2 |
| SadBridge Loader | Subdomains: 5 Domains: 5 |
| XLoader 6 and 7 | Domains: 67 |
| Operation BarrelFire | Domain: 1 IPs: 2 |
| ClickFix | Subdomains: 7 Domains: 16 IPs: 3 |
| APT36 Python-Based ELF Malware | Domain: 1 IP: 1 |
| Chihuahua Stealer | Subdomains: 2 Domains: 2 |
| Earth Ammit | Subdomains: 7 Domains: 7 IPs: 3 |
| Docker Swarm and Kubernetes Attack | Subdomain: 1 Domain: 1 IPs: 3 |
| PlushDaemon | Subdomains: 2 Domain: 1 IPs: 2 |
| Earth Alux | Subdomains: 2 Domains: 2 IP: 1 |
We analyzed the IoCs further, which led to these discoveries:
A sample of the additional artifacts obtained from our analysis is available for download from our website.
We began our analysis by looking for more information about the 26 subdomains identified as IoCs for seven of the 11 attacks via the WhoisXML API MCP Server.
We determined that while many of them were considered either benign or inactive, five have been confirmed as malicious—four related to Earth Ammit and one to Earth Alux.
As our next step, we sought out more details about the 104 domains identified as IoCs for the 11 threats.
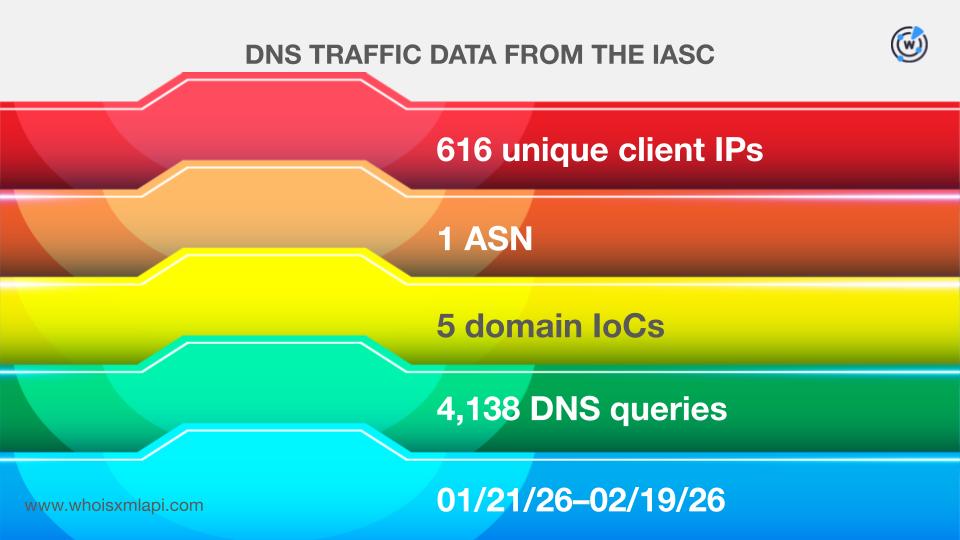
Sample network traffic data from the IASC, for one, revealed that 616 unique client IP addresses under a single ASN communicated with five of the domains tagged as IoCs via a total of 4,138 DNS queries made between 21 January and 19 February 2026.
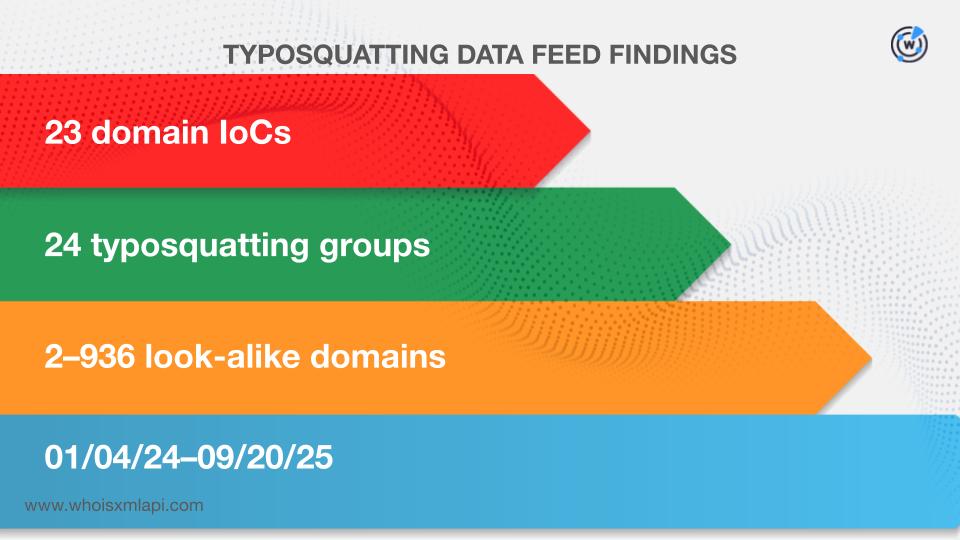
We sought to find out if any of the 104 domains named as IoCs appeared in the Typosquatting Data Feed and discovered that 23 were part of 24 typosquatting domain groups. Each was bulk-registered with 2—936 look-alikes between 4 January 2024 and 20 September 2025.
The results of our First Watch Malicious Domains Data Feed searches, meanwhile, showed that 28 of the domains categorized as IoCs for five threats could have been registered with malicious intent from the get-go. In fact, they were deemed likely to turn malicious 46—516 days before they were reported as IoCs. Take a look at more details for a domain related to each threat below.
| THREAT | DOMAIN IoC | FIRST WATCH INCLUSION DATE | NUMBER OF DAYS BEFORE REPORTING |
|---|---|---|---|
| STATICPLUGIN | mediareleaseupdates[.]com | 07/20/24 | 402 |
| XLoader 6 and 7 | carpmaxxbait[.]online | 11/24/23 | 430 |
| ClickFix | groupewadesecurity[.]com | 12/09/24 | 350 |
| Chihuahua Stealer | cat-watches-site[.]xyz | 01/25/25 | 164 |
| Earth Ammit | symantecsecuritycloud[.]com | 12/14/23 | 516 |
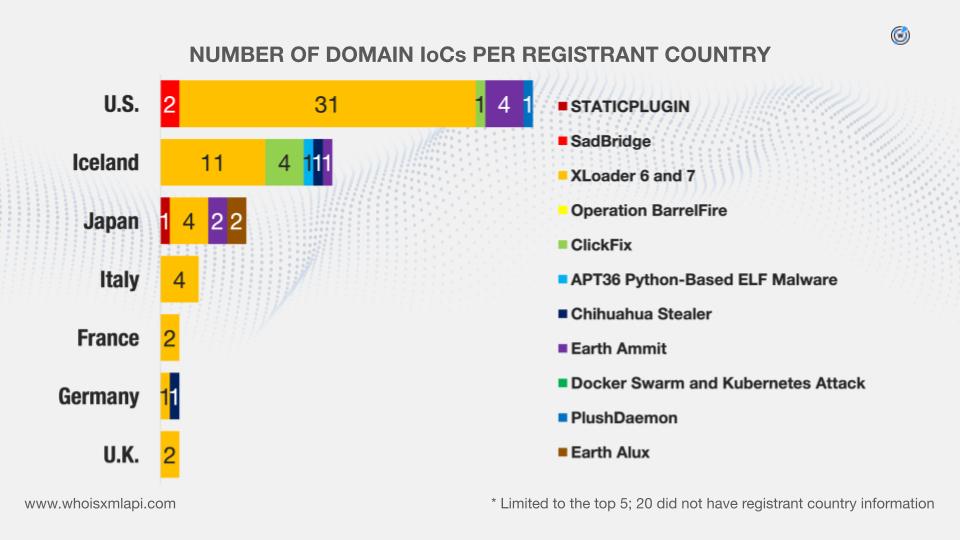
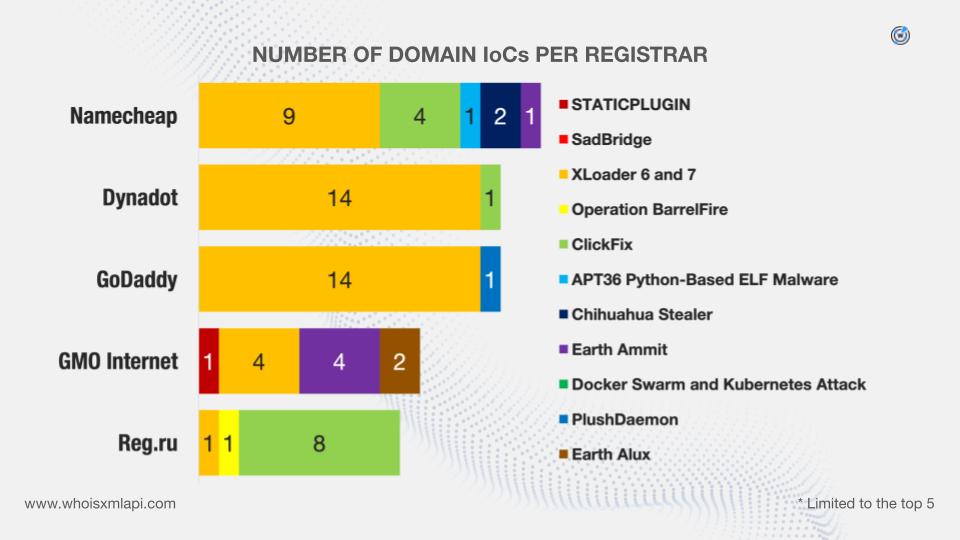
We then queried the 104 domains classified as IoCs on WHOIS API and discovered that:
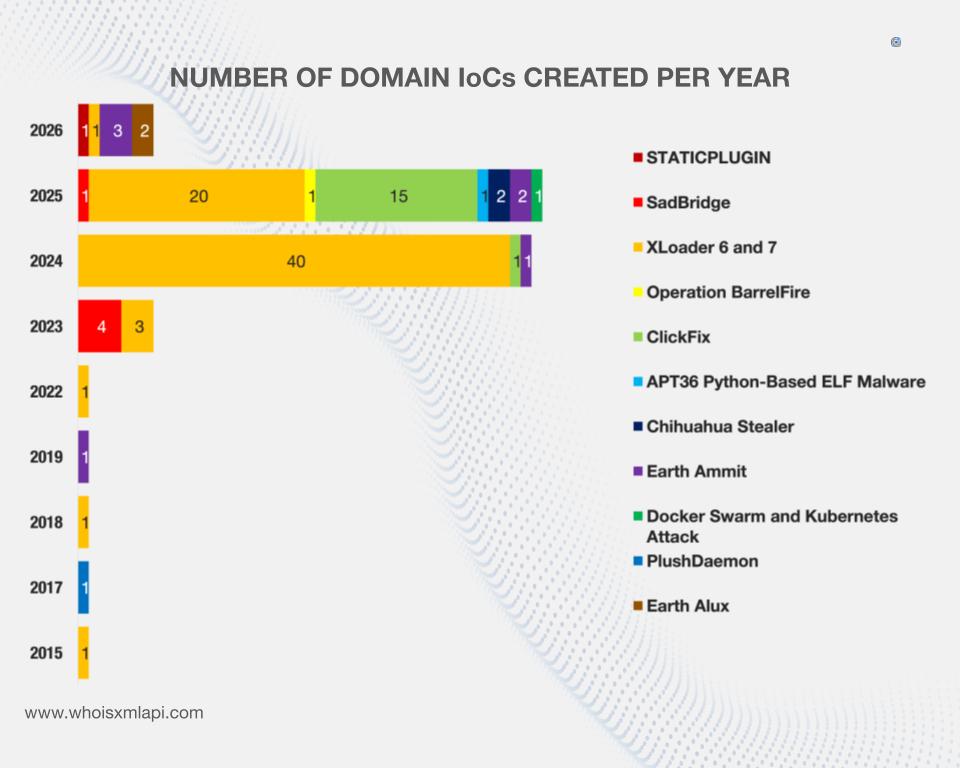
They were administered by 29 different registrars.

While 20 did not have registrant countries on record, the remaining 84 domains were registered in 15 different countries.
We also queried the 104 domains dubbed as IoCs on DNS Chronicle API and found out that 101 related to 10 threats have recorded 5,823 domain-to-IP resolutions over time. Here are details on a domain related to each threat.
| THREAT | DOMAIN IoC | NUMBER OF RESOLUTIONS | TIME PERIOD |
|---|---|---|---|
| STATICPLUGIN | mediareleaseupdates[.]com | 20 | 07/21/24—02/19/26 |
| SadBridge | secssl[.]com | 3 | 06/27/22—12/14/24 |
| XLoader 6 and 7 | alace5[.]com | 519 | 02/05/17—02/06/26 |
| Operation BarrelFire | wellfitplan[.]ru | 8 | 04/14/25—02/09/26 |
| ClickFix | galaxyswapper[.]pro | 61 | 08/08/22—02/14/26 |
| APT36 Python-Based ELF Malware | lionsdenim[.]xyz | 3 | 11/03/25—11/30/25 |
| Chihuahua Stealer | cat-watches-site[.]xyz | 24 | 01/28/25—04/28/25 |
| Earth Ammit | *uckeveryday[.]life | 37 | 07/29/23—01/06/26 |
| Docker Swarm and Kubernetes Attack | solscan[.]live | 70 | 06/15/22—01/17/26 |
| Earth Alux | upload-microsoft[.]com | 6 | 11/20/23—02/19/26 |
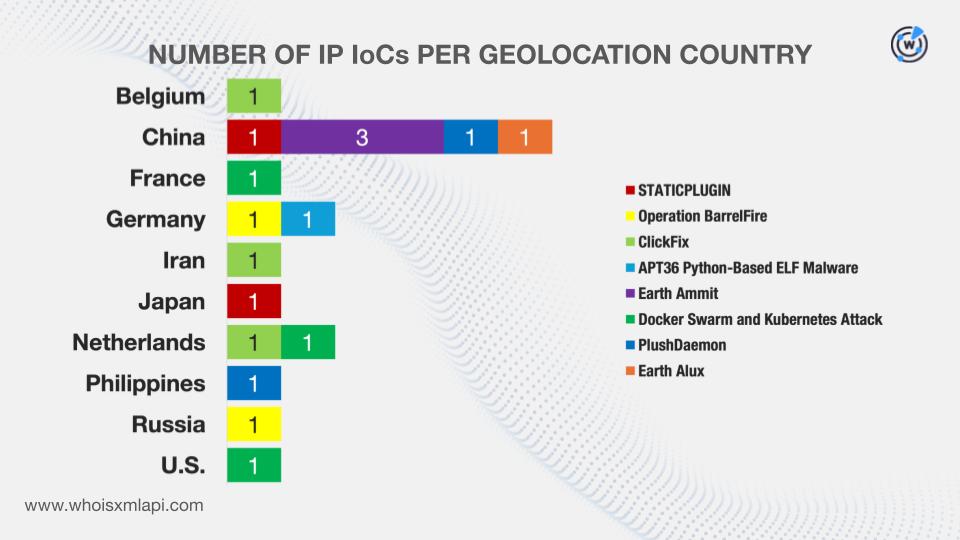
Next, we scoured the DNS for more information about the 17 IP addresses identified as IoCs for eight threats.
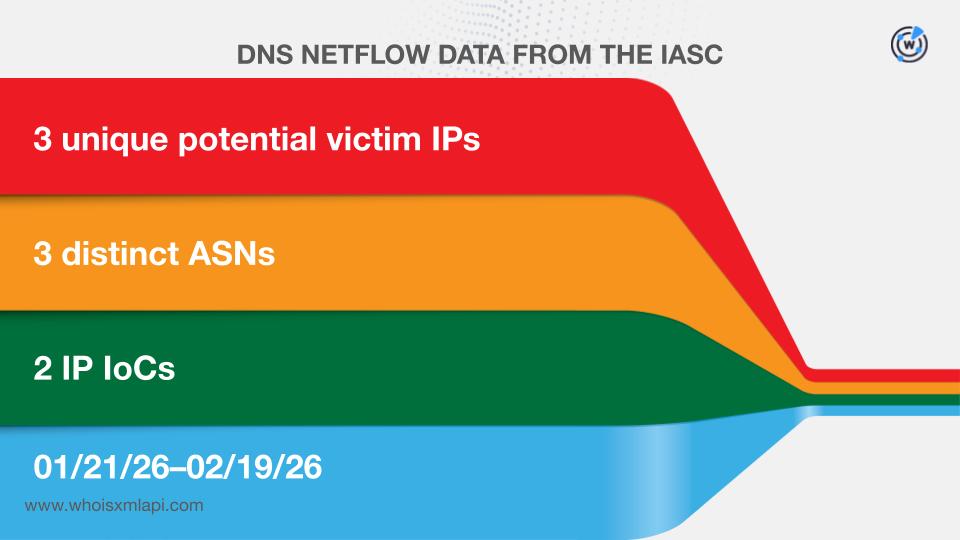
Sample network data from the IASC, for instance, revealed that three unique potential victim IP addresses under three distinct ASNs communicated with two IP addresses tagged as IoCs between 21 January and 19 February 2026.
We then queried them on Bulk IP Geolocation Lookup and discovered that:
While one did not have an ISP on record, the remaining 16 were administered by 12 ISPs.
DNS Chronicle API queries for the 17 IP addresses named as IoCs showed that 16 IPs related to eight threats recorded 1,842 IP-to-domain resolutions over time. Take a look at more information on an IP address related to each threat below.
| THREAT | IP IoC | NUMBER OF RESOLUTIONS | TIME PERIOD |
|---|---|---|---|
| STATICPLUGIN | 166[.]88[.]2[.]90 | 88 | 07/09/18—02/11/26 |
| Operation BarrelFire | 178[.]159[.]94[.]8 | 18 | 12/10/17—03/04/18 |
| ClickFix | 141[.]98[.]80[.]175 | 12 | 10/03/25—02/19/26 |
| APT36 Python-Based ELF Malware | 185[.]235[.]137[.]90 | 33 | 09/01/24—04/09/25 |
| Earth Ammit | 45[.]121[.]50[.]30 | 19 | 03/14/20—01/31/26 |
| Docker Swarm and Kubernetes Attack | 192[.]155[.]94[.]199 | 763 | 02/06/17—01/21/26 |
| PlushDaemon | 47[.]242[.]198[.]250 | 6 | 07/31/24—08/24/24 |
| Earth Alux | 8[.]218[.]222[.]216 | 2 | 01/23/26—02/15/26 |
After gathering more details about the IoCs, we then scoured the DNS for additional connected artifacts.
First, we queried the 104 domains identified as IoCs on WHOIS History API and found out that 58 had 125 unique email addresses in their historical WHOIS records. Careful scrutiny allowed us to discern that 28 were public email addresses.
Reverse WHOIS API queries for the 28 public email addresses revealed that four could belong to domainers. This step also led to the discovery of 7,770 unique email-connected domains after those already listed as IoCs were filtered out.
According to Threat Intelligence API, 25 email-connected domains have already been weaponized for various threats.
This post only contains a snapshot of the full research. Download the complete findings and a sample of the additional artifacts on our website or contact us to discuss your intelligence needs for threat detection and response or other cybersecurity use cases.
Disclaimer: We take a cautionary stance toward threat detection and aim to provide relevant information to help protect against potential dangers. Consequently, it is possible that some entities identified as “threats” or “malicious” may eventually be deemed harmless upon further investigation or changes in context. We strongly recommend conducting supplementary investigations to corroborate the information provided herein.
Sponsored byIPv4.Global

Sponsored byDNIB.com

Sponsored byVerisign

Sponsored byCSC

Sponsored byVerisign

Sponsored byWhoisXML API

Sponsored byRadix
