


|
||
|
||
LummaStealer reportedly got a second lease on life after years of being considered the world’s most prolific information stealer. Even after a significant law-enforcement disruption in 2025, LummaStealer operations continued, demonstrating the malware’s resilience aided by rapidly migrating to new hosting providers and adapting alternative loaders and delivery techniques like ClickFix.
Bitdefender uncovered a new LummaStealer campaign that used CastleLoader as its central delivery mechanism. This combination allowed the infostealer to use in-memory execution, heavy obfuscation, and flexible payload deployment to evade detection and enable massive distribution.
The researchers identified several network IoCs in their report. After extracting domains from the subdomains tagged as IoCs and excluding those that belonged to legitimate organizations, we collated 211 IoCs comprising two subdomains, 180 domains, and 29 IP addresses for further analysis, which led to these discoveries:
A sample of the additional artifacts obtained from our analysis is available for download from our website.
We began our investigation by looking for more information on the two subdomains tagged as IoCs via the WhoisXML API MCP Server. And we discovered that:
We then shifted our focus on the 180 domains identified as IoCs.
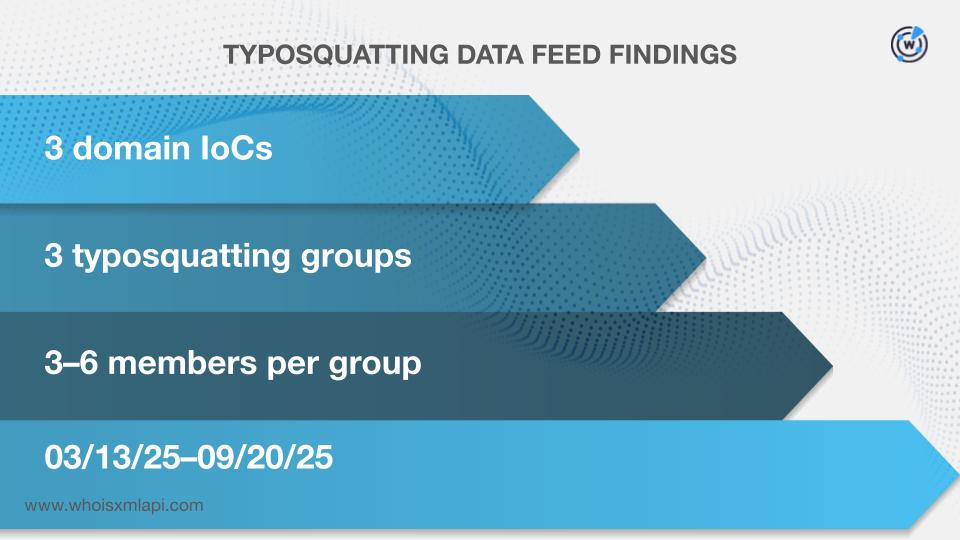
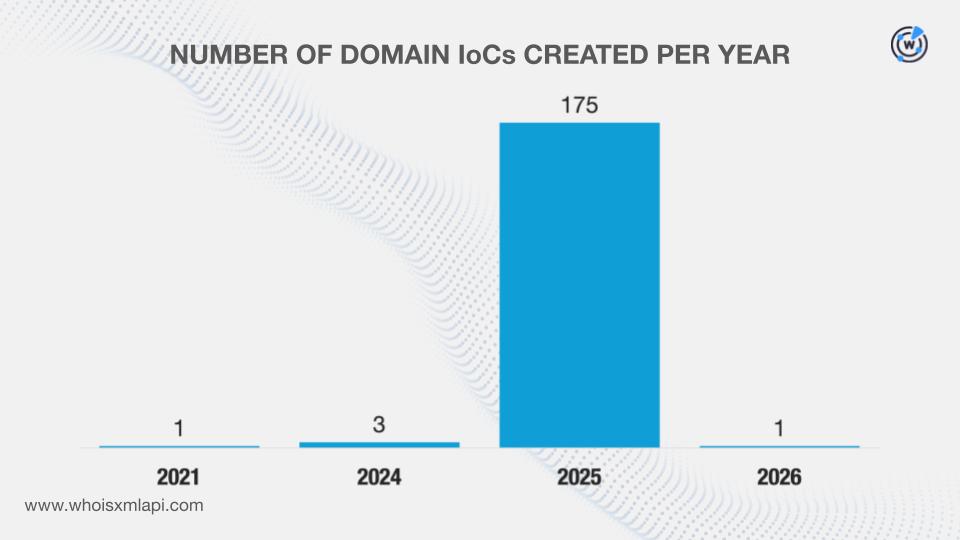
Our searches on the Typosquatting Data Feed revealed that three of the domains classified as IoCs appeared in three typosquatting groups with 3—6 members each (i.e., one IoC and 2—5 look-alikes). They were registered between 13 March and 20 September 2025.
Our First Watch Malicious Domains Data Feed search results showed that 49 of the domains named as IoCs could have been registered with malicious intent. They were deemed likely to turn malicious 43—432 days before being dubbed as IoCs on 11 February 2026. Take a look at five examples below.
| DOMAIN IoC | FIRST WATCH DATE | NUMBER OF DAYS BEFORE THE REPORT DATE |
|---|---|---|
| diffuculttan[.]xyz | 12/06/24 | 432 |
| effecterectz[.]xyz | 12/06/24 | 432 |
| mannelaeksug[.]top | 01/17/25 | 390 |
| sterilizeflow[.]top | 01/17/25 | 390 |
| weighcobbweo[.]top | 01/17/25 | 390 |
Next, we queried the domains on WHOIS API. We found out that one did not have current WHOIS registration data but we did obtain historical information from Domain Info API. Our searches led to these findings:
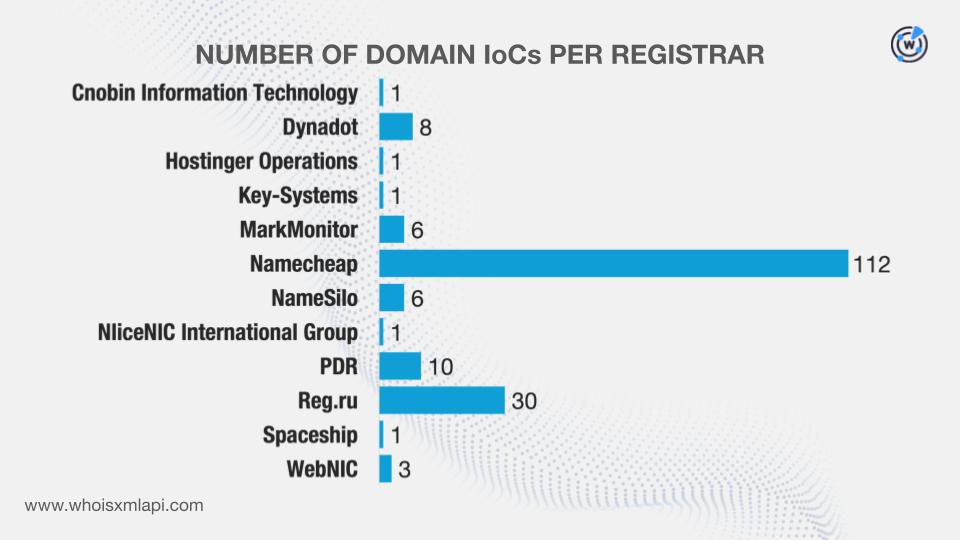
They were administered by 12 different registrars.
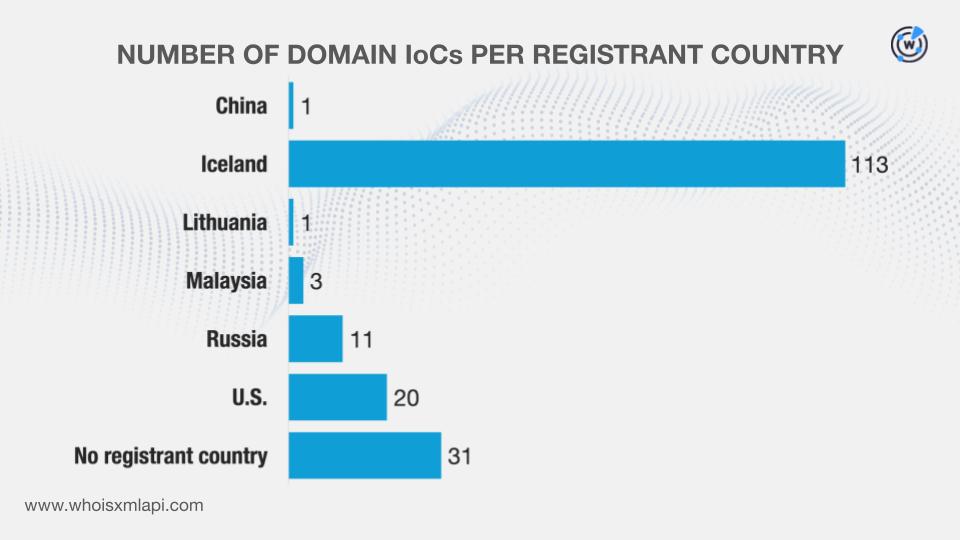
And while 31 of them did not have registrant countries on record, the remaining 149 were registered in six different countries.
Last but not least, we queried the domains on DNS Chronicle API and found out that 161 had 2,944 historical domain-to-IP resolutions over time. Here are more details on five of them.
| DOMAIN IoC | NUMBER OF DOMAIN-TO-IP RESOLUTIONS | DATES SEEN |
|---|---|---|
| whitepepper[.]su | 477 | 07/01/17–02/08/26 |
| rifledog[.]xyz | 11 | 01/08/18–01/20/26 |
| sealake[.]info | 227 | 04/16/18–02/16/26 |
| tailcoat[.]xyz | 81 | 04/19/19–02/07/26 |
| hatwomen[.]info | 69 | 12/08/19–02/16/26 |
A closer look at the historical domain-to-IP resolutions also showed that a majority of the domains categorized as IoCs, 148 to be exact, first recorded resolutions in 2025.
After that, we zoomed in on the 29 IP addresses identified as IoCs.
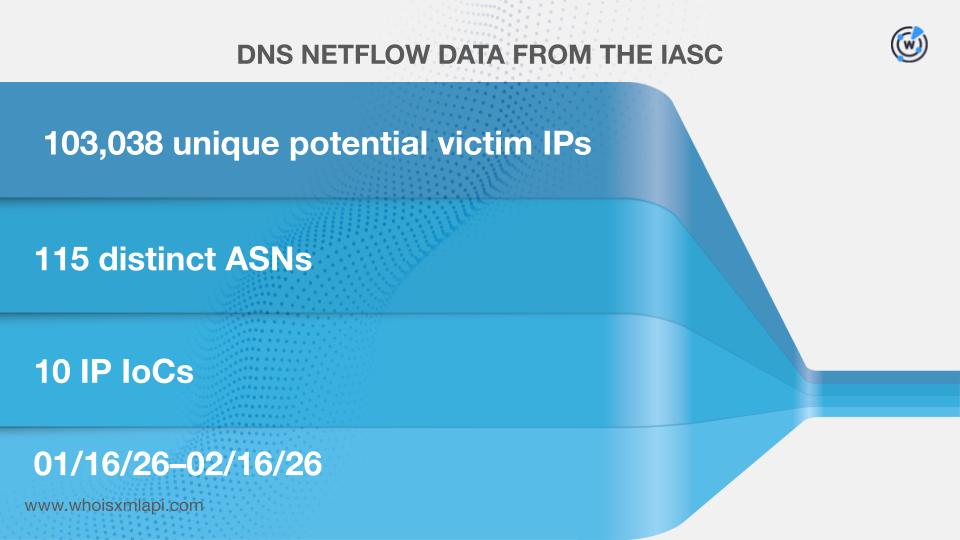
Sample network traffic data from the IASC revealed that 103,038 unique potential victim IP addresses under 115 distinct ASNs communicated with 10 of the IP addresses tagged as IoCs between 16 January and 16 February 2026.
Next, we queried them on Bulk IP Geolocation Lookup and discovered that:
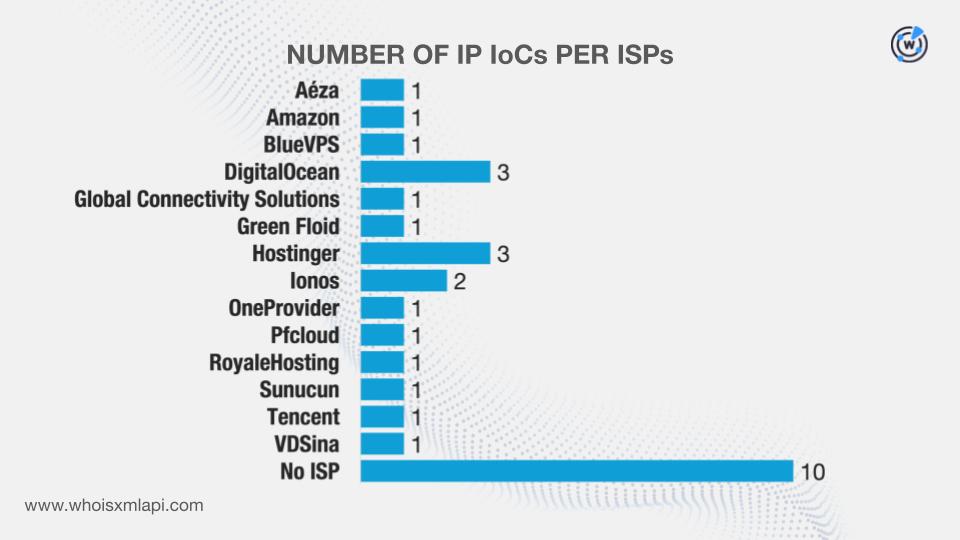
While 10 did not have ISPs on record, the remaining 19 were administered by 14 different ISPs.
Our DNS Chronicle API queries for the IP addresses, meanwhile, revealed that 24 had 2,869 historical IP-to-domain resolutions over time. Take a look at more information for five examples below.
| IP IoC | NUMBER OF IP-TO-DOMAIN RESOLUTIONS | DATES SEEN |
|---|---|---|
| 85[.]90[.]196[.]155 | 266 | 02/04/17–01/12/26 |
| 185[.]121[.]233[.]78 | 217 | 02/06/17–02/04/22 |
| 31[.]220[.]109[.]219 | 46 | 09/23/17–12/12/25 |
| 144[.]172[.]115[.]212 | 214 | 07/23/18–12/08/25 |
| 206[.]189[.]97[.]184 | 308 | 08/17/18–02/12/26 |
In comparison to the domains categorized as IoCs, eight of the IP addresses dubbed as IoCs recorded their first resolutions in 2025.
Our hunt for other LummaStealer-connected artifacts started with WHOIS History API queries for the 180 domains identified as IoCs. We discovered that 165 of them had 159 unique email addresses in their historical WHOIS records. Further scrutiny showed that 15 were public email addresses.
The results of our Reverse WHOIS API queries for the 15 public email addresses revealed that one could belong to a domainer, excluding it from further analysis. This step led to the discovery of 129 unique email-connected domains after those already tagged as IoCs were filtered out.
Threat Intelligence API queries for the email-connected domains showed that 26 have already been confirmed as malicious. Here are more details for five examples.
| MALICIOUS EMAIL-CONNECTED DOMAIN | ASSOCIATED THREAT | DATES SEEN |
|---|---|---|
| advennture[.]top | Malware distribution | 03/23/25–02/16/26 |
| boustrn[.]su | Malware distribution | 09/26/25–02/16/26 |
| consnbx[.]su | Malware distribution | 09/09/25–02/16/26 |
| cornerdurv[.]top | Malware distribution | 05/20/25–02/16/26 |
| coverxyzer[.]su | Malware distribution | 01/07/26–02/16/26 |
Next, we queried the domains dubbed as IoCs on DNS Lookup API and found out that 125 actively resolved to 200 unique additional IP addresses.
Threat Intelligence API queries for the additional IP addresses showed that 196 have already figured in several malicious campaigns.
This post only contains a snapshot of the full research. Download the complete findings and a sample of the additional artifacts on our website or contact us to discuss your intelligence needs for threat detection and response or other cybersecurity use cases.
Disclaimer: We take a cautionary stance toward threat detection and aim to provide relevant information to help protect against potential dangers. Consequently, it is possible that some entities identified as “threats” or “malicious” may eventually be deemed harmless upon further investigation or changes in context. We strongly recommend conducting supplementary investigations to corroborate the information provided herein.
Sponsored byDNIB.com

Sponsored byWhoisXML API

Sponsored byCSC

Sponsored byVerisign

Sponsored byVerisign

Sponsored byIPv4.Global

Sponsored byRadix
