


|
||
|
||
WhoisXML API expands Cisco Talos’s findings on the new UAT-8099 campaign that has been active since late 2025 to date, identifying additional associated artifacts.
UAT-8099 is a threat actor that has reportedly targeted vulnerable IIS servers across Asia specifically focusing on Thailand and Vietnam. They used web shells and PowerShell to execute scripts and deploy the GotoHTTP tool, granting them remote access to vulnerable IIS servers. They also utilized new BadIIS variants that came hardcoded with their target region, along with customized features for each variant.
Cisco Talos originally identified 17 network IoCs. Upon further scrutiny (i.e., apex domain extraction from subdomains and exclusion of legitimate domains) aided by the WhoisXML API MCP Server, we ended up with and analyzed 27 IoCs comprising 10 domains and 17 subdomains. Our in-depth investigation led to these discoveries:
A sample of the additional artifacts obtained from our analysis is available for download from our website.
We began our analysis by querying the 17 subdomains identified as IoCs using the WhoisXML API MCP Server.
We discovered that 13 of them fell under recently registered domains, and several consisted of random characters, which is unusual for legitimate websites. Only one, however, merited complete avoidance since it seemed to be mimicking Google, typical of sites designed for phishing campaigns.
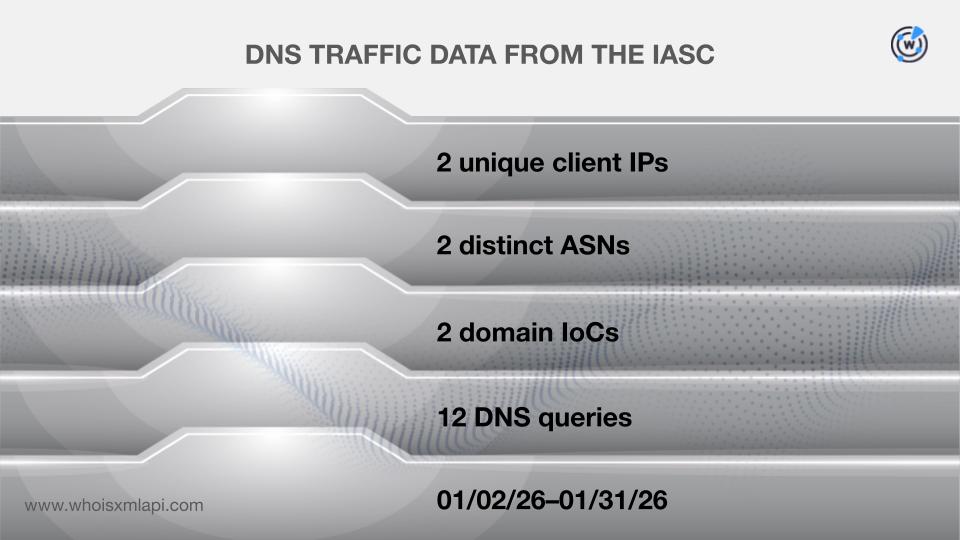
Sample network traffic data from the IASC showed that two unique client IP addresses under two distinct ASNs communicated with two domains identified as IoCs via 12 DNS queries between 2 and 31 January 2026.
The First Watch Malicious Domains Data Feed revealed that three of the domains tagged as IoCs were deemed likely to turn malicious 545—569 days before they were dubbed as such. An example is the domain gtwql[.]com, which was likely registered with malicious intent 569 days before it was named as an IoC on 29 January 2026.
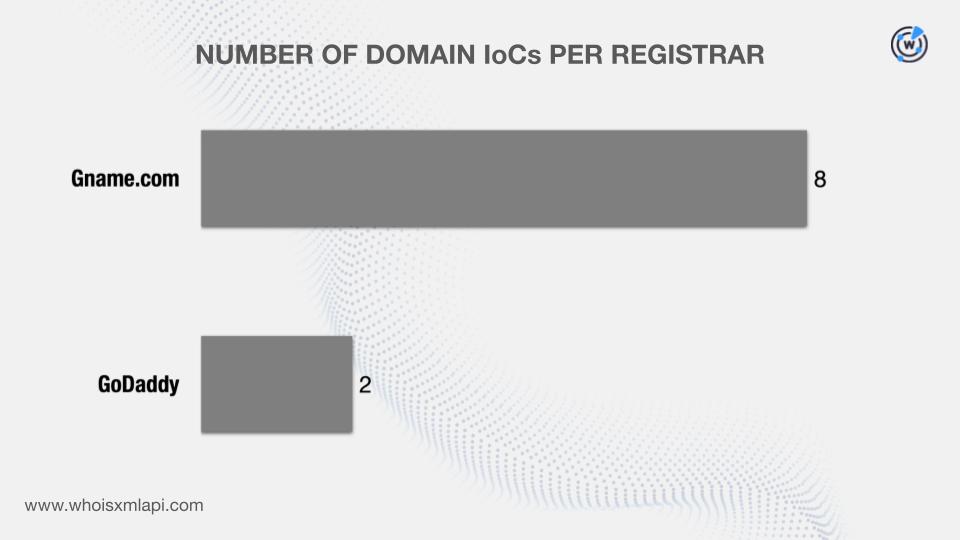
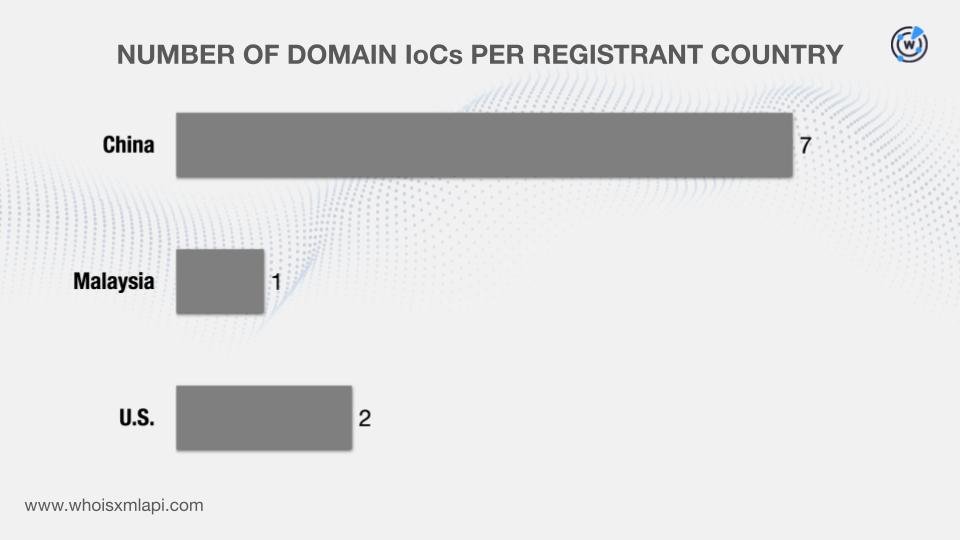
Next, we queried the 10 domains classified as IoCs on WHOIS API and discovered that:
They were administered by two registrars.
They were registered in three different countries.
DNS Chronicle API queries for the 10 domains categorized as IoCs revealed that seven recorded 566 domain-to-IP resolutions over time. Take a look at more details for three examples below.
| DOMAIN IoC | NUMBER OF RESOLUTIONS | FIRST RESOLUTION DATE | LAST RESOLUTION DATE |
|---|---|---|---|
| ceye[.]io | 354 | 02/26/17 | 01/30/26 |
| jmfwy[.]com | 58 | 04/29/17 | 01/27/26 |
| hunanduodao[.]com | 36 | 06/13/22 | 01/08/26 |
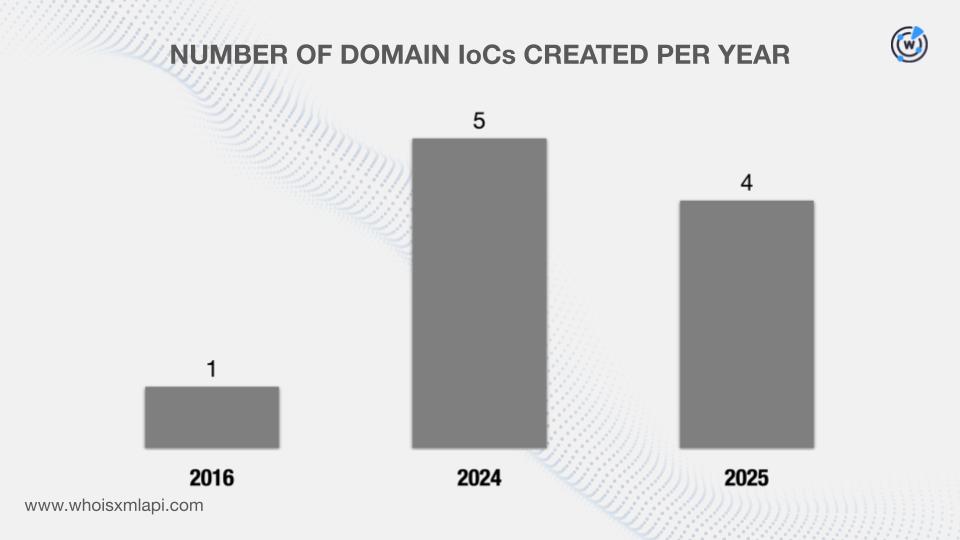
A closer look at the historical resolutions of the seven domains revealed as IoCs showed that two first posted resolutions in 2017, one in 2022, and four in 2025.
To unearth new artifacts connected to this UAT-8099 campaign, we queried the 10 domains identified as IoCs on WHOIS History API. We found out that three of them had eight unique email addresses in their historical WHOIS records. Upon further scrutiny, seven were public email addresses.
The results of our Reverse WHOIS API queries for the public email addresses revealed that two could belong to domainers. The remaining five public email addresses, meanwhile, led to the discovery of 12,787 unique email-connected domains after those already named as IoCs were filtered out.
Threat Intelligence API queries for the email-connected domains showed that four have already been weaponized for various attacks. An example is dmnsg[.]com, which has already been associated with malware distribution between 9 March 2023 and 30 January 2026.
Next, we queried the 10 domains named as IoCs on DNS Lookup API and discovered that seven resolved to 13 unique IP addresses.
The results of our Threat Intelligence API queries for the IP addresses revealed that 12 have already figured in various malicious campaigns.
This post only contains a snapshot of the full research. Download the complete findings and a sample of the additional artifacts on our website or contact us to discuss your intelligence needs for threat detection and response or other cybersecurity use cases.
Disclaimer: We take a cautionary stance toward threat detection and aim to provide relevant information to help protect against potential dangers. Consequently, it is possible that some entities identified as “threats” or “malicious” may eventually be deemed harmless upon further investigation or changes in context. We strongly recommend conducting supplementary investigations to corroborate the information provided herein.
Sponsored byVerisign

Sponsored byWhoisXML API

Sponsored byCSC

Sponsored byVerisign

Sponsored byDNIB.com

Sponsored byIPv4.Global

Sponsored byRadix
