

|
||
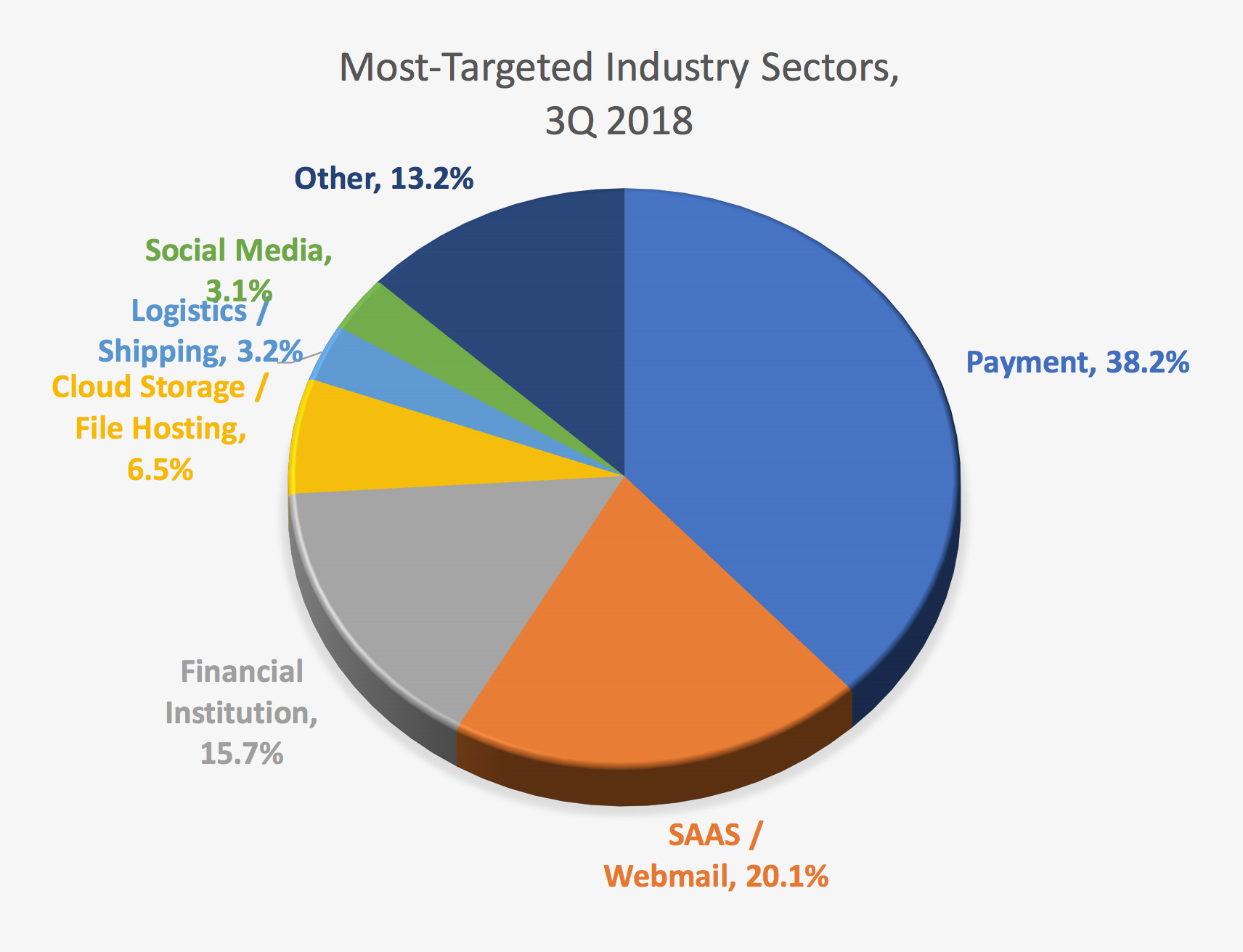 Most-Targeted Industry Sectors, 3Q 2018 from APWG Phishing Activity Trends ReportAccording to the APWG’s new Phishing Activity Trends Report released today, phishers are using new techniques to carry out their attacks and hide their origins in order to make the most of every phishing campaign. From the report: “Phishers are increasingly using web page redirects as a way of hiding their phishing sites from detection. When victims click on links in phishing emails, redirects take the user on an unwitting journey through other sites before arriving at the phishing site itself. And then once the victim submits his or her credentials, still more redirects make take the victim to yet another domain.”
Most-Targeted Industry Sectors, 3Q 2018 from APWG Phishing Activity Trends ReportAccording to the APWG’s new Phishing Activity Trends Report released today, phishers are using new techniques to carry out their attacks and hide their origins in order to make the most of every phishing campaign. From the report: “Phishers are increasingly using web page redirects as a way of hiding their phishing sites from detection. When victims click on links in phishing emails, redirects take the user on an unwitting journey through other sites before arriving at the phishing site itself. And then once the victim submits his or her credentials, still more redirects make take the victim to yet another domain.”
— “The researchers at APWG member PhishLabs have observed that half of all phishing sites now use SSL encryption, which can fool users into thinking that a site is safe to use, for example, by virtue of the green lock symbol that appears in the browser address bar when SSL encryption is enabled. Some of the increase comes from phishers adding HTTP encryption to their phishing sites—a technique that turns a security feature against the victims.”
— “Certain top-level domains have notable amounts of phishing in them, both in absolute and relative terms. Some of this phishing is attributable to phishers who register in top-level domains that offer domain names for free.”
Sponsored byCSC

Sponsored byVerisign

Sponsored byWhoisXML API

Sponsored byDNIB.com

Sponsored byVerisign

Sponsored byRadix

Sponsored byIPv4.Global
