


|
||
|
||
MuddyWater has been in the APT business for some time now. And this time, it set its sights on organizations and individuals primarily across the MENA region, leveraging ongoing geopolitical tensions. Dubbed “Operation Olalampo,” the threat actors deployed new malware variants and used Telegram bots for C&C.
Group-IB published their analysis of the threat, including seven network IoCs comprising four domains and three IP addresses, which we further dove into. Note that we checked if any of the domains were owned by legitimate entities aided by the WhoisXML API MCP Server. None of them were so we did not exclude any of them in our investigation.
Our DNS exploration into the IoCs led to these findings:
A sample of the additional artifacts obtained from our analysis is available for download from our website.
We began our investigation by looking more closely at the four domains identified as IoCs.
We queried them on WHOIS API and found out that:
DNS Chronicle API queries for the domains revealed that three recorded 27 historical domain-to-IP resolutions over time, consistent with their ages. Take a look at more information below.
| DOMAIN IoC | NUMBER OF DOMAIN-TO-IP RESOLUTIONS | DATES SEEN |
|---|---|---|
| jerusalemsolutions[.]com | 16 | 10/29/25—02/23/26 |
| miniquest[.]org | 9 | 01/29/26—02/11/26 |
| codefusiontech[.]org | 2 | 02/03/26—02/07/26 |
We then sought for more information about the three IP addresses identified as IoCs.
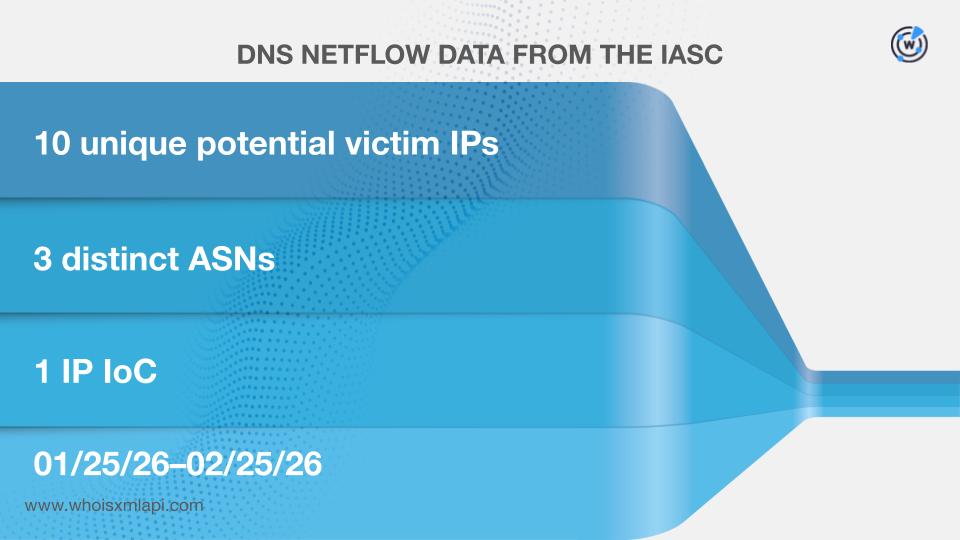
First, sample network data from the IASC showed that 10 unique IP addresses possibly owned by victims under three distinct ASNs communicated with one of the IP addresses tagged as IoCs between 25 January and 25 February 2026
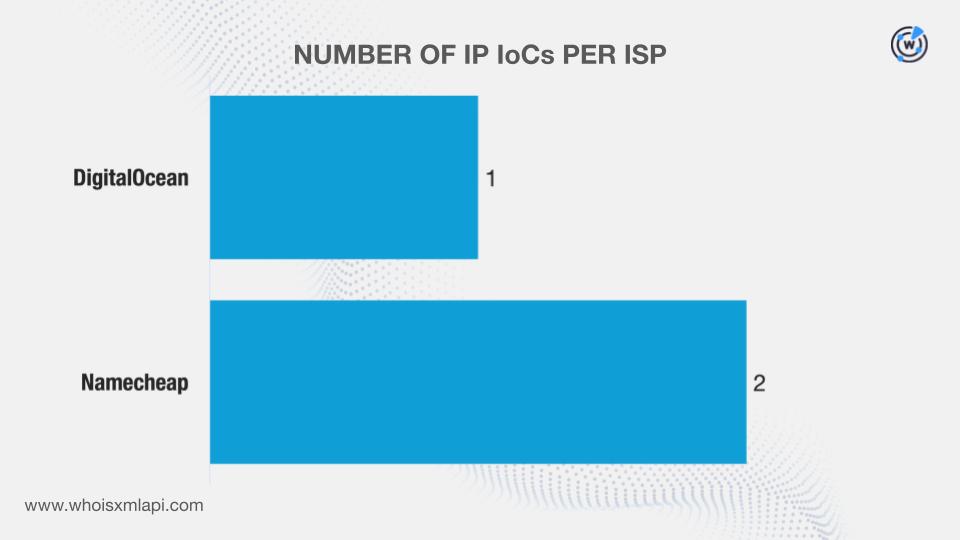
We queried them on Bulk IP Geolocation Lookup and discovered that:
DNS Chronicle API queries for the IP addresses revealed that two recorded 1,017 historical IP-to-domain resolutions over time. Here are more details.
| IP IoC | NUMBER OF IP-TO-DOMAIN RESOLUTIONS | DATES SEEN |
|---|---|---|
| 162[.]0[.]230[.]185 | 1,000 | 09/05/20–07/24/21 |
| 209[.]74[.]87[.]100 | 17 | 03/10/25–05/10/25 |
We then used a variety of solutions to gather as many new potentially connected artifacts as possible.
First, we queried the four domains identified as IoCs on WHOIS History API. We found out that all of them had seven unique email addresses in their historical WHOIS records. Further scrutiny revealed that one was a public email address.
A Reverse WHOIS API query for the sole public email address allowed us to collate 2,530 unique email-connected domains after those already tagged as IoCs were filtered out.
Next, we queried the domains named as IoCs on DNS Lookup API and discovered that three resolved to six unique additional IP addresses (i.e., not on the IoC list).
Threat Intelligence API queries for the additional IP addresses showed that all of them have already been weaponized for various attacks.
This post only contains a snapshot of the full research. Download the complete findings and a sample of the additional artifacts on our website or contact us to discuss your intelligence needs for threat detection and response or other cybersecurity use cases.
Disclaimer: We take a cautionary stance toward threat detection and aim to provide relevant information to help protect against potential dangers. Consequently, it is possible that some entities identified as “threats” or “malicious” may eventually be deemed harmless upon further investigation or changes in context. We strongly recommend conducting supplementary investigations to corroborate the information provided herein.
Sponsored byWhoisXML API

Sponsored byDNIB.com

Sponsored byRadix

Sponsored byIPv4.Global

Sponsored byVerisign

Sponsored byVerisign

Sponsored byCSC
