


|
||
|
||
StepSecurity recently uncovered and is continuously tracking the ForceMemo campaign targeting developers’ GitHub accounts. The attackers reportedly injected the same malware into hundreds of Python repositories starting 8 March 2026.
The researchers identified several network IoCs related to the threat. We extracted domains from the subdomains tagged as IoCs and weeded out those that belonged to legitimate entities aided by the WhoisXML API MCP Server. In the end, we analyzed 20 IoCs comprising nine subdomains, five domains, and six IP addresses.
Our in-depth investigation of the IoCs led to these discoveries:
A sample of the additional artifacts obtained from our analysis is available for download from our website.
We kicked off our analysis by looking for more information about the nine subdomains dubbed as IoCs via the WhoisXML API MCP Server.
We discovered that they all belonged to code repositories, mostly open-source or free services. While none of the domains they fell under have been categorized as malicious, some of the code stored in them could have been injected with the malware as part of the ForceMemo campaign.
Take a look at specific findings for three examples below.
| SUBDOMAIN IoC | WXA MCP SERVER FINDING |
|---|---|
| api[.]blockeden[.]xyz | Based on data up to August 2025, BlockEden[.]xyz is a blockchain infrastructure and API platform, primarily targeting Web3 developers. It provides RPC/API endpoints for multiple blockchains (Aptos, Sui, Ethereum, Solana, etc.), staking services, and analytics tools for on-chain data. This subdomain is their main developer API gateway. |
| api[.]mainnet-beta[.]solana[.]com | This is the official public RPC endpoint for the Solana Mainnet Beta network operated by the Solana Foundation. Developers use it to interact with the Solana blockchain (submitting transactions, querying accounts, etc.). It is a heavily used but rate-limited endpoint. Production apps are generally encouraged to use dedicated RPC providers instead. |
| go[.]getblock[.]us | GetBlock (getblock[.]io) is a well-known blockchain node-as-a-service/RPC provider supporting 50+ blockchains including Solana, Ethereum, BNB Chain, Bitcoin, and many others. This subdomain appears to be their U.S.-facing API gateway with the dual-IP, ultra-low TTL setup designed to maximize availability and minimize latency for North American users. |
We then went on to gather DNS data on the five domains categorized as IoCs.
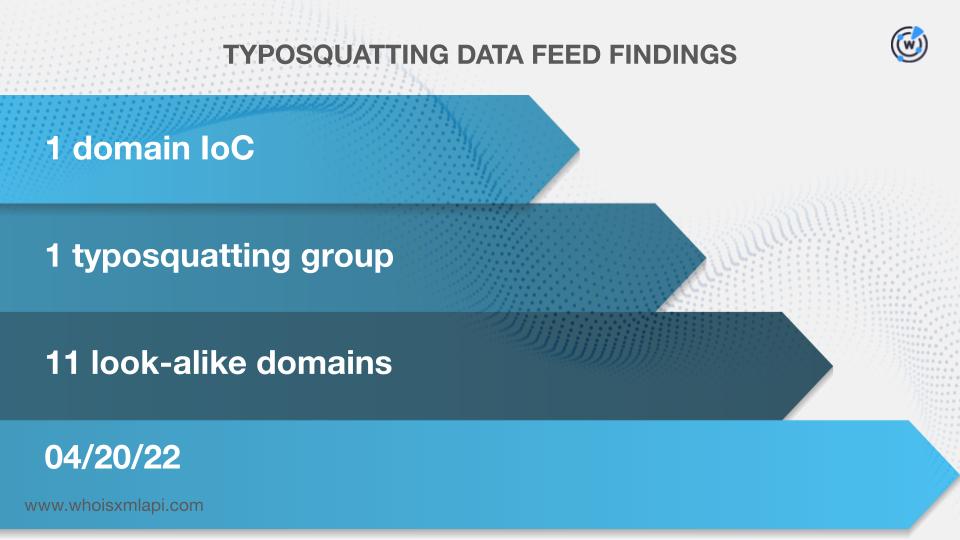
We scoured the Typosquatting Data Feed and found out that the domain pocket[.]network was bulk-registered with 11 look-alike domains on 20 April 2022.
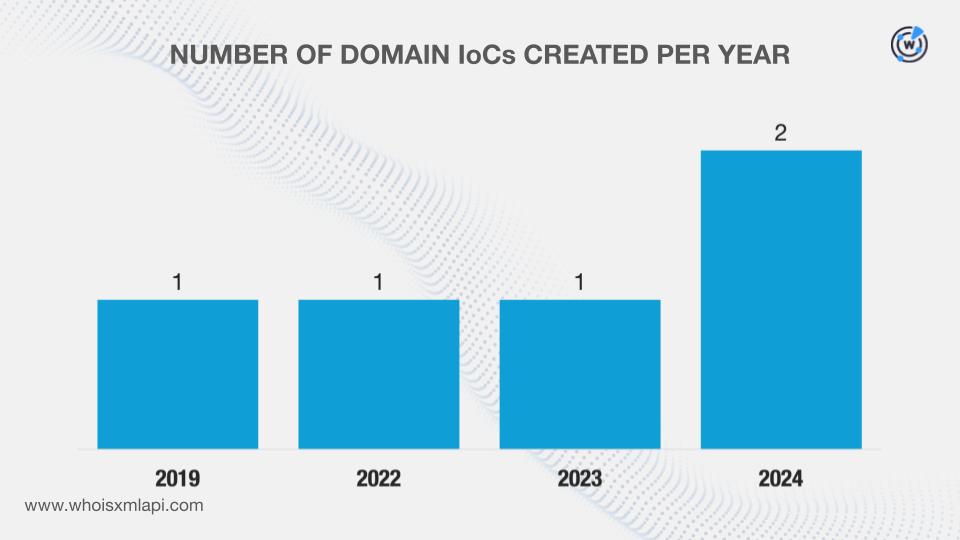
Our searches on the First Watch Malicious Domains Data Feed, meanwhile, revealed that the same domain—pocket[.]network—was deemed to have been registered with malicious intent on 23 February 2024, 750 days before being dubbed as an IoC on 14 March 2026.
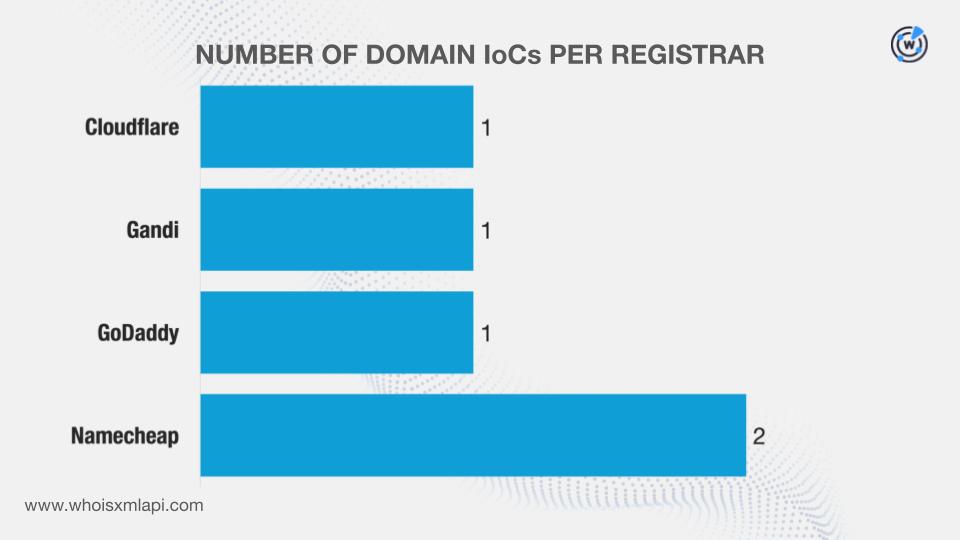
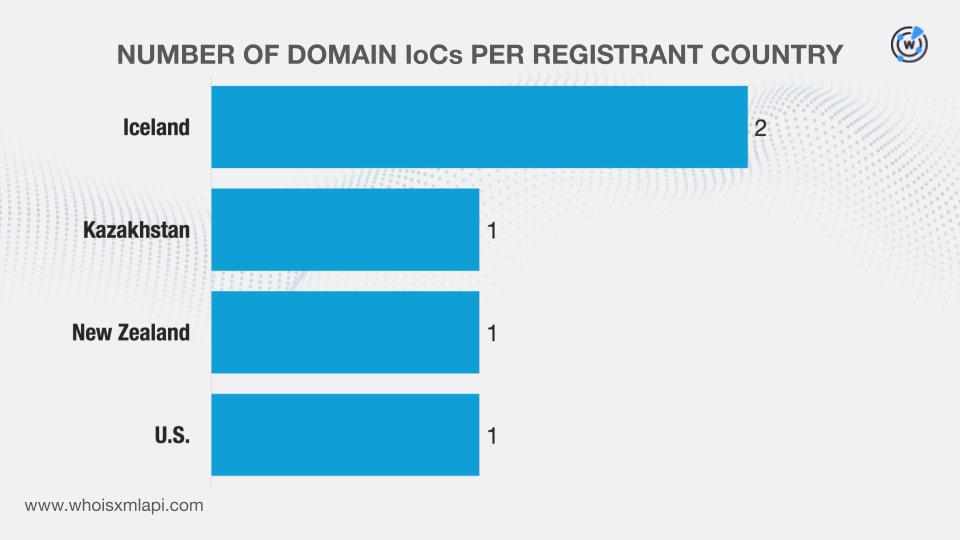
We then queried the domains on WHOIS API and filled in gaps (i.e., missing details) specifically for blockeden[.]xyz using Domain Info API, which gave us the latest available information from its historical records. We discovered that:
They were administered by four registrars.
They were registered in four countries.
DNS Chronicle API queries for the domains showed that four recorded 1,368 historical domain-to-IP resolutions over time. Take a look at more information for two examples below.
| DOMAIN IoC | NUMBER OF DOMAIN-TO-IP RESOLUTIONS | DATES SEEN |
|---|---|---|
| pocket[.]network | 102 | 12/04/17–02/28/26 |
| onfinality[.]io | 1,000 | 04/24/20–02/17/26 |
Given the dates when the sample domains above last resolved to IP addresses, we can infer that they continue to be actively used for the campaign.
Next, we gathered more information on the six IP addresses identified as IoCs.
A Bulk IP Geolocation Lookup for the IP addresses revealed that:
Our DNS Chronicle API queries for the IP addresses showed that five recorded 251 historical IP-to-domain resolutions over time. Below are more details for two examples.
| IP IoC | NUMBER OF IP-TO-DOMAIN RESOLUTIONS | DATES SEEN |
|---|---|---|
| 45[.]32[.]151[.]157 | 58 | 02/11/17–06/07/21 |
| 217[.]69[.]11[.]57 | 61 | 04/18/20–05/04/25 |
Since the dates when the sample IP addresses above last resolved to domains do not extend to 2026, we can infer that the attackers may have opted to use new IPs for the campaign.
As the final step in our investigation, we sought to uncover artifacts that could be connected to the threat.
We began by querying the five domains tagged as IoCs on WHOIS History API. We found out that all of them had seven unique email addresses in their historical records. Further scrutiny revealed that three were public email addresses.
Reverse WHOIS API queries for the public email addresses led to the discovery of 86 unique email-connected domains after those already named as IoCs were filtered out.
We then queried the domains on DNS Lookup API and learned that four actively resolved to nine unique IP addresses that were not in the list of IoCs.
Threat Intelligence API queries for the additional IP addresses revealed that four have already been weaponized for various attacks.
This post only contains a snapshot of the full research. Download the complete findings and a sample of the additional artifacts on our website or contact us to discuss your intelligence needs for threat detection and response or other cybersecurity use cases.
Disclaimer: We take a cautionary stance toward threat detection and aim to provide relevant information to help protect against potential dangers. Consequently, it is possible that some entities identified as “threats” or “malicious” may eventually be deemed harmless upon further investigation or changes in context. We strongly recommend conducting supplementary investigations to corroborate the information provided herein.
Sponsored byVerisign

Sponsored byWhoisXML API

Sponsored byCSC

Sponsored byIPv4.Global

Sponsored byRadix

Sponsored byVerisign

Sponsored byDNIB.com
