

ICANN has submitted the first report of what will be a series of annual reports summarizing its "expierince" with the Whois Data problems and inaccuracies. While emphasizing that "ICANN-accredited registrars are obligated by the terms of their accreditation agreements to investigate and correct any reported inaccuracies," the report provides the following conclusions: more
We, as the Internet engineering community, have made a great mistake. Actually, it wasn't even one large mistake, but a series of small ones. Engineers are busy people, and most of us work under the constraints of the organizational entities we serve (be it ISPs, non-internet corporates, or even non-profits). Few of us have time for politics; even fewer have the desire and motivation for politics, and those of us who do try usually end up facing a brick wall of stubbornness, lack of understanding of the underlying technical issues, or just a deaf ear. more
 To paraphrase an old Klingon proverb, there can be no spam solution, so long as e-mail is free. Yahoo has unveiled plans to launch its Domain Keys software as an open-source toolkit in 2004. The intent is to allow developers of major e-mail systems to integrate Yahoo's public/private key authentication system into their own software and thus create momentum for a standard whose raison d'etre is identify verification. This is a commendable effort, but a closer look reveals that it will not only not stop the spam problem, it may have almost no effect at all. more
To paraphrase an old Klingon proverb, there can be no spam solution, so long as e-mail is free. Yahoo has unveiled plans to launch its Domain Keys software as an open-source toolkit in 2004. The intent is to allow developers of major e-mail systems to integrate Yahoo's public/private key authentication system into their own software and thus create momentum for a standard whose raison d'etre is identify verification. This is a commendable effort, but a closer look reveals that it will not only not stop the spam problem, it may have almost no effect at all. more
 Stratton Sclavos of VeriSign distills the essence of the SiteFinder controversy in his CNet interview...There is a subtle but essential misunderstanding here. Innovation can and should happen in Internet infrastructure, but there are a handful of core elements that must remain open and radically simple if the Internet is to remain, well, the Internet. These include TCP/IP, SMTP, HTTP, BIND, BGP, and the DNS (especially the .com registry). Any change in these protocols should be very carefully vetted through a consensus-based process. more
Stratton Sclavos of VeriSign distills the essence of the SiteFinder controversy in his CNet interview...There is a subtle but essential misunderstanding here. Innovation can and should happen in Internet infrastructure, but there are a handful of core elements that must remain open and radically simple if the Internet is to remain, well, the Internet. These include TCP/IP, SMTP, HTTP, BIND, BGP, and the DNS (especially the .com registry). Any change in these protocols should be very carefully vetted through a consensus-based process. more
Yet another DNS blacklist has been taken down out of fear of the DDoS attacks that took down Osirusoft, Monkeys.com, and the OpenRBL. Blackholes.compu.net suffered a Joe-Job (A Joe-Job is essentially spam designed to look like it's coming from someone else.) earlier this week. Apparently the Joe-Jobing was enough to convince some extremely ignorant mail administrators that Compu.net is spamming and blocked mail from compu.net. Compu.net has also seen the effects of DDoS attacks on other DNS blacklist maintainers. They've decided that the risk to their actual business is too great and they are pulling the plug on their DNS blacklist before they come under the gun by spammers. more
Register.com has not taken a position for or against WLS. If and when the registry launches this service, Register.com will consider whether to offer it based on the price and conditions attached to the service. We are committed to delivering to our customers the best in class services available. Therefore, the registry's price will be an important factor. Moreover, we are concerned about some of the conditions currently being considered by ICANN - primarily, the "black out period." This is a period of time prior to the final deletion of a name, during which a registrar would be prohibited from selling a WLS subscription on a domain name that it sponsors. We consider this a condition that could confuse consumers and dampen domain name competition. more
 Some individual appears to have hijacked more than a 1,000 home computers starting in late June or early July and has been installing a new Trojan Horse program on them. The Trojan allows this person to run a number of small websites on the hijacked home computers. These websites consists of only a few web pages and apparently produce income by directing sign-ups to for-pay porn websites through affiliate programs. Spam emails messages get visitors to come to the small websites.
Some individual appears to have hijacked more than a 1,000 home computers starting in late June or early July and has been installing a new Trojan Horse program on them. The Trojan allows this person to run a number of small websites on the hijacked home computers. These websites consists of only a few web pages and apparently produce income by directing sign-ups to for-pay porn websites through affiliate programs. Spam emails messages get visitors to come to the small websites.
To make it more difficult for these websites to be shut down, a single home computer is used for only 10 minutes to host a site. After 10 minutes, the IP address of the website is changed to a different home computer... more
A recent study by researchers at the Cooperative Association for Internet Data Analysis (CAIDA) at the San Diego Super Computer Center (SDSC) revealed that a staggering 98% of the global Internet queries to one of the main root servers, at the heart of the Internet, were unnecessary. This analysis was conducted on data collected October 4, 2002 from the 'F' root server located in Palo Alto, California.
The findings of the study were originally presented to the North American Network Operators' Group (NANOG) on October 2002 and later discussed with Richard A. Clarke, chairman of the President's Critical Infrastructure Protection Board and Special Advisor to the U.S. President for Cyber Space Security. more
 Recently, I entered my domain name in a "WHOIS" database query to test the results of the database by using WHOIS on a number of domain name registrar websites. WHOIS is a database service that allows Internet users to look up a number of matters associated with domain names, including the full name of the owner of a domain name, the name of the domain name hosting service, the Internet Protocol or I.P. number(s) corresponding to the domain name, as well as personally identifying information on those who have registered domain names. I was astonished to find... more
Recently, I entered my domain name in a "WHOIS" database query to test the results of the database by using WHOIS on a number of domain name registrar websites. WHOIS is a database service that allows Internet users to look up a number of matters associated with domain names, including the full name of the owner of a domain name, the name of the domain name hosting service, the Internet Protocol or I.P. number(s) corresponding to the domain name, as well as personally identifying information on those who have registered domain names. I was astonished to find... more
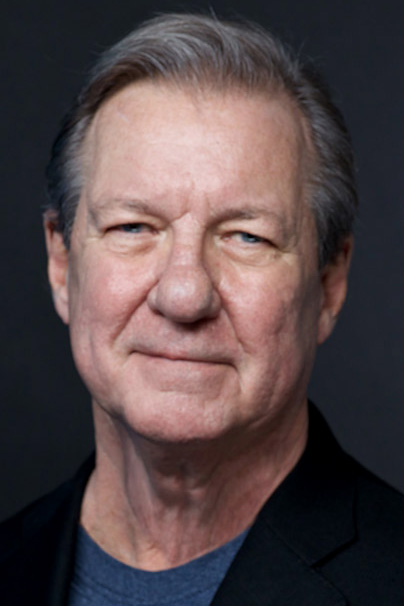
Cybersecurity pioneer Steven Bellovin's new book strips away jargon and outdated online-safety advice, offering ordinary users practical guidance on passwords, phishing, privacy and digital habits in an era of constant cyber threats and increasingly sophisticated scams. more
 CDA Section 230 has been called "The 26 Words that Created the Internet". While it is obvious how Sec 230 protects the World Wide Web, it is equally important for e-mail. A recent Pennsylvania court case emphasizes this point. Dr. Thomas, a professor at the University of Pennsylvania, forwarded an article about another professor Dr. Monge to an online e-mail discussion list. Dr. Monge claimed the article was defamatory and sued Dr. Thomas, the university, and many others. more
CDA Section 230 has been called "The 26 Words that Created the Internet". While it is obvious how Sec 230 protects the World Wide Web, it is equally important for e-mail. A recent Pennsylvania court case emphasizes this point. Dr. Thomas, a professor at the University of Pennsylvania, forwarded an article about another professor Dr. Monge to an online e-mail discussion list. Dr. Monge claimed the article was defamatory and sued Dr. Thomas, the university, and many others. more
 From time to time, a party can get out of control. Raucous celebration can become careless, even destructive. Combine a critical number of young people, a certain amount of beer and lots of music and damage often happens. Partygoers leave a mess behind them. The same thing happens to some IP addresses. Malicious actors use IP addresses properly registered to someone else. more
From time to time, a party can get out of control. Raucous celebration can become careless, even destructive. Combine a critical number of young people, a certain amount of beer and lots of music and damage often happens. Partygoers leave a mess behind them. The same thing happens to some IP addresses. Malicious actors use IP addresses properly registered to someone else. more
 I can still hear it. ‘Hee hee’. That’s good. We all have unique laughs, but few are distinctive. Fewer yet belly the true nature of the human being issuing them. British insult comedian Jimmy Carr has one such laugh, a tri-tone ‘dah dah DUH,’ rising on the third expulsion. It has a bell-like quality, ringing, embodying the deft touch that Don Rickles had of insulting while loving, something Carr has mastered. It lets you know that despite him having just said something shocking and horrid, he is laughing with, never at, reassuring the target, ‘all is well.’ more
I can still hear it. ‘Hee hee’. That’s good. We all have unique laughs, but few are distinctive. Fewer yet belly the true nature of the human being issuing them. British insult comedian Jimmy Carr has one such laugh, a tri-tone ‘dah dah DUH,’ rising on the third expulsion. It has a bell-like quality, ringing, embodying the deft touch that Don Rickles had of insulting while loving, something Carr has mastered. It lets you know that despite him having just said something shocking and horrid, he is laughing with, never at, reassuring the target, ‘all is well.’ more
 Has your organization recently received an email claiming to be from NABP's Internet Drug Outlet Identification Program (IDOI)? If so, it is possible that someone is trying to trick you. The NABP IDOI team's email account has recently been illegally "spoofed" by unaffiliated persons or organizations. Email spoofing involves the forgery of an email header so that the email appears to have originated from someone other than the actual source. more
Has your organization recently received an email claiming to be from NABP's Internet Drug Outlet Identification Program (IDOI)? If so, it is possible that someone is trying to trick you. The NABP IDOI team's email account has recently been illegally "spoofed" by unaffiliated persons or organizations. Email spoofing involves the forgery of an email header so that the email appears to have originated from someone other than the actual source. more
 A recent piece in The Markup called Swinging the Vote? attempts to figure out how Google decides where to deliver political e-mail. They were startled to discover that only a small fraction of it was delivered into the main inbox, and a fair amount was classed as spam. They shouldn't have been. This is an example of the fallacy We're so nice that the rules don't apply to us, which is far too common among non-profit and political mailers. more
A recent piece in The Markup called Swinging the Vote? attempts to figure out how Google decides where to deliver political e-mail. They were startled to discover that only a small fraction of it was delivered into the main inbox, and a fair amount was classed as spam. They shouldn't have been. This is an example of the fallacy We're so nice that the rules don't apply to us, which is far too common among non-profit and political mailers. more