


|
||
|
||
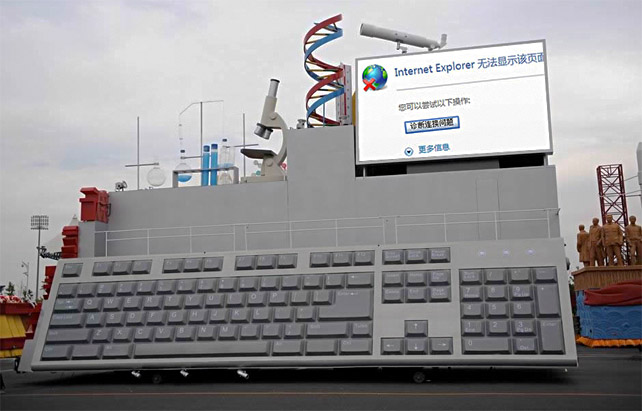
Last week the China Digital Times reported that the photo below has been making the rounds in Chinese blogs and chatrooms. It is an image of a “computer science float” for Thursday’s National Day parade, onto which somebody has photoshopped a screenshot of the Internet Explorer error message familiar to anybody who has ever tried to access a blocked website in China: “This page cannot be displayed.”
As the 60th birthday of the People’s Republic of China approaches, Internet users in China are complaining that the Internet has become even more difficult to use than ever before. Not only has the number of blocked websites increased, but the most popular censorship circumvention techniques and technologies have come under attack. A sampling:
VPN‘s (Virtual Private Networks): The most popular VPN’s among people I know in China are Witopia and Hotspot Shield. Witopia users in Beijing report that even with the VPN on, they have to manually set the DNS (via these instructions, see Q6) in order to access certain super-blocked sites like Facebook and Twitter. Others, in Shanghai and elsewhere, report that Witopia isn’t even working when they set the DNS, or it works only intermittently for all sites. People all over China are telling me that Hotspot Shield no longer works for them at all.
Tor (onion routing): Since September 25th, according to the Tor development team, 80% of Tor’s public relays are “blocked by IP address and TCP port combination.” However you can still access Tor via bridges, updated regularly in various places. See some Chinese instructions here.
Freegate: (Note their website is down as of 1am Monday EDT) This tool developed by FLG-followers has reportedly been under attack since around September 1st. They have issued an update but according to various people around China who I’ve queried, including those using the latest version, it’s still intermittent and difficult to use.
SSH tunnel: Dave Lyons, who has set up a tunnel to his own server outside China, reports that he also has to use Foxyproxy. UPDATE: Jon Phillips aka “Rejon” has detailed instructions for SSH tunneling here.
Proxy servers: Until this summer, probably the most common (if insecure and unreliable) way to access blocked websites was through proxies. It has been the case for years that users of public proxies had to switch frequently as they got blocked. However in the past few months Internet users in China have been reporting that the blocking of public proxies has become much more thorough.
Psiphon: I’ve sent out queries to see if anybody out there in my Twitter network is using Psiphon and whether it’s working. However as of this writing I’ve gotten no responses. [UPDATE 30 minutes later: one person reports it’s working]
If anybody reading this post has anything to add about any of the above, please share it in the comments section of this post.
Meanwhile, Global Voices Advocacy, Reporters Without Borders, The Register, and PCWorld all report that at least some ISP’s in some parts of China have been ordered to install new censorship and surveillance software, “Lan Dun,” which has variously been translated as “Bluedon,” “Blue Shield” or “Blue Dam.” According to PCWorld:
At least one Chinese city has adopted a further measure to monitor Internet traffic. The southern city of Guangzhou this month ordered Internet service providers to install “security monitoring” software on all servers and threatened punishment for failure to do so, according to government notices posted on the blog of one data center management company. Two such software programs, called Blue Shield and Huadun, were recommended in one of the government notices. Huadun’s Web site says the program helps server owners remove illegal and pornographic content from their systems.
The software is meant to “create a favorable online environment” for China’s National Day celebration next week, the government orders said. A representative of the data center company reached by phone said it put the orders on the blog for reference by clients and that the order applied only to Guangzhou.
Both Global Voices and Reporters Without Borders cite this Chinese-language Apple Daily (Taiwan) article which says that all ISP’s were required to install the software by September 13th. According to the product description, it not only blocks websites but also logs individual users’ web browsing histories and monitors instant messaging conversations.
In other developments, AFP quotes Chinese state media reports of new laws in Northwest China (namely Xinjiang) “making it a criminal offence for people to discuss separatism on the Internet.” AFP continues:
The Bill passed by authorities in the Xinjiang region bans locals from using the internet in any way that undermines national unity.
It also bans them from inciting ethnic separatism or harming social stability, the China News Service reported.The Bill requires internet service providers and network operators to set up monitoring systems—or strengthen existing ones—and report anyone who breaks the law, the report said.
The Bill did not specify what punishment offenders would face, but its apparent aim is to allow authorities to arrest individuals behind emails and web posts within the region that they deem to be a threat.“The introduction of the ‘Information Promotion Bill’ is timely and necessary,” the report quoted the Bill as saying.
“It ensures internet criminals can be quickly and effectively controlled in the future.”
The Internet was shut off in Xinjiang in early July and has not been turned back on. Blogger-journalist Michael Anti posted a report on Twitter that Internet connectivity will finally be restored in Xinjiang in mid-October.
Global Voices Advocacy also recently reported that Chinese Internet users are also becoming more acutely aware of the reality that domestic companies like Tencent log users’ conversations and share them with the police as requested.
Sponsored byVerisign

Sponsored byCSC

Sponsored byRadix

Sponsored byWhoisXML API

Sponsored byDNIB.com

Sponsored byIPv4.Global

Sponsored byVerisign
