


|
||
|
||
Back in March 2025, we investigated the DNS footprint of what were dubbed 2025’s up and coming ransomware families—RansomHub, LockBit 3.0, Play, Akira, Hunters, Medusa, BlackBasta, Qilin, BianLian, and INC Ransom (aka Lynx). We now looked back at last year’s actual threat landscape and discovered that six of them actually made Picus Security’s top 10 ransomware list—Qilin, Akira, Play, INC Ransom, Lynx, and RansomHub.
Take a look at brief descriptions of the 10 ransomware featured in this report below, along with the links to the reports we obtained lists of network IoCs from below.
| RANK | RANSOMWARE | DESCRIPTION | IoC SOURCE | DATE PUBLISHED |
|---|---|---|---|---|
| 1 | Qilin | Also known as “Agenda” and uses advanced techniques, cross-platform variants, and alliances with other major threat groups | https://www.trendmicro.com/vinfo… | 12/31/25 |
| 2 | Akira | RaaS that emerged in March 2023 that targeted 250+ organizations worldwide | https://thedfirreport.com/2025/... | 08/07/25 |
| 3 | Cl0p | Often targets the critical infrastructure, financial, and government sectors using encryptionless tactics to steal data and demand ransoms without encrypting files | https://theravenfile.com/2025… | 11/04/25 |
| 4 | Play | Known for infiltrating companies via exposed RDP servers and exploiting vulnerabilities | https://unit42.paloaltonetworks… | 05/18/25 |
| 5 | INC Ransom | Known for highly aggressive, rapid, and targeted attacks against enterprises in the healthcare, manufacturing, education, and government sectors primarily in North America and Europe | https://www.trendmicro.com/vinfo… | 01/15/26 |
| 6 | SafePay | Operates with a centralized non-RaaS model and frequently executes attacks within a 24-hour window using double-extortion tactics | https://www.acronis.com/en/tru… | 07/08/25 |
| 7 | Lynx | Widely considered a rebranded and more advanced variant of INC Ransom that focuses on double extortion tactics targeting SMBs and large organizations across sectors primarily in the U.S. and the U.K. | https://thedfirreport.com/2025/... | 11/19/25 |
| 8 | RansomHub | Known for operating as a cartel, it lets affiliates keep up to 90% of the ransom payment, attracting experienced threat actors | https://thedfirreport.com/2025/... | 07/01/25 |
| 9 | DragonForce | Operates by leasing to affiliates who conduct attacks through double-extortion tactics | https://www.acronis.com/en/tru… | 11/05/25 |
| 10 | Babuk2 | Suspected to be led by the actor known as “Bjorka,” it uses the notorious Babuk brand to perpetrate extortion through recycled data | https://www.rapid7.com/blog/post… | 04/02/25 |
With the aid of the WhoisXML API MCP Server, we extracted domains from the subdomains identified as IoCs and weeded out those that belonged to legitimate entities, did not leave DNS traces behind, and were only accessible via the Dark Web. After that, we were left with 267 network IoCs comprising 28 domains, 236 IP addresses, and three email addresses for our analysis, which led to these discoveries:
A sample of the additional artifacts obtained from our analysis is available for download from our website.
Note that while we collated 29 domains identified as IoCs for analysis for six of the top 10 ransomware, one domain was tagged as an IoC for two ransomware variants.
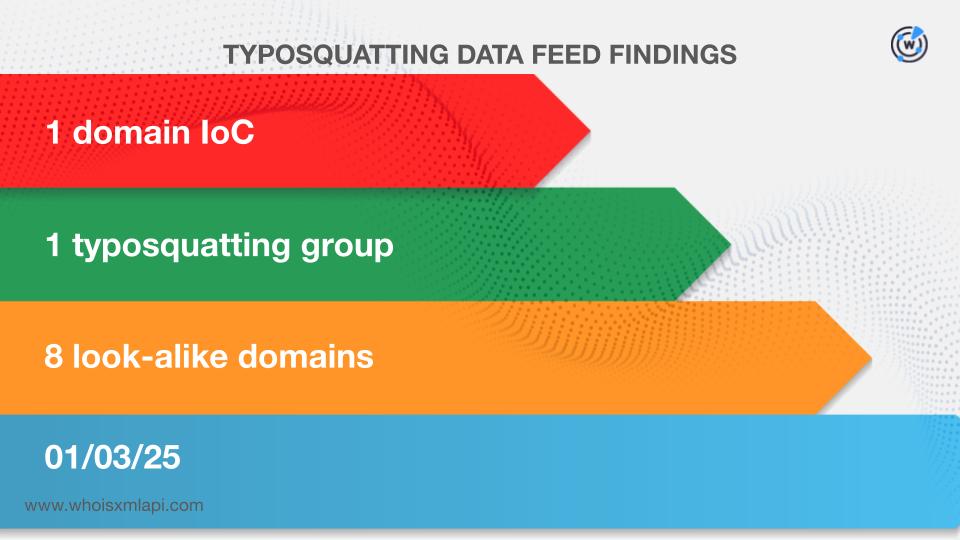
We began our investigation by scouring the Typosquatting Data Feed for signs of the 28 domains. We discovered that the domain simplerwebs[.]world connected to INC Ransom was bulk-registered with eight look-alikes on 3 January 2025.
Next, we sought to find out if any of the 28 domains were likely registered with malicious intent from the get-go. We discovered that three domains related to Akira were tagged as malicious 15—37 days before they were reported as such on 7 August 2025. Here are more details about them.
| DOMAIN IoC | FIRST WATCH DATE | NUMBER OF DAYS BEFORE THE REPORT DATE |
|---|---|---|
| 2rxyt9urhq0bgj[.]org | 07/01/25 | 37 |
| ev2sirbd269o5j[.]org | 07/09/25 | 29 |
| ijt0l3i8brit6q[.]org | 07/23/25 | 15 |
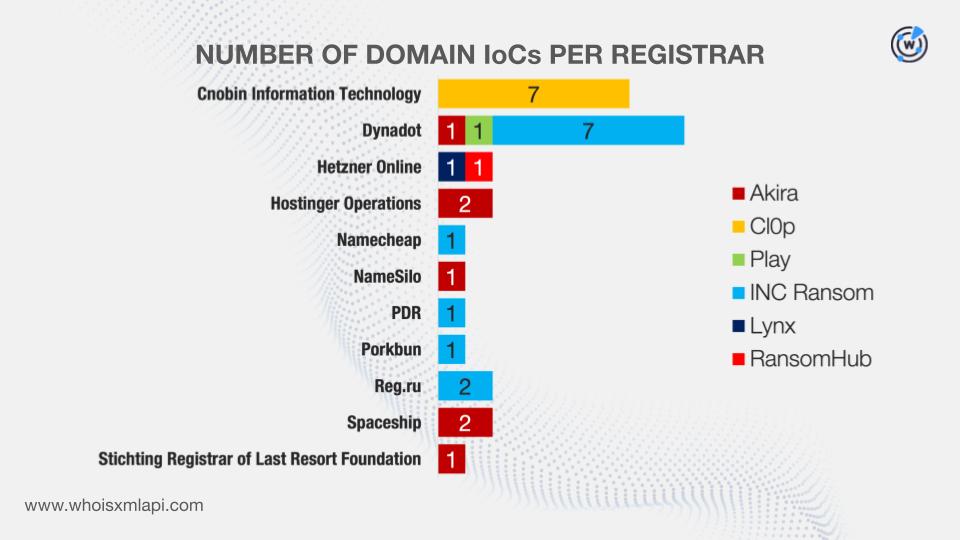
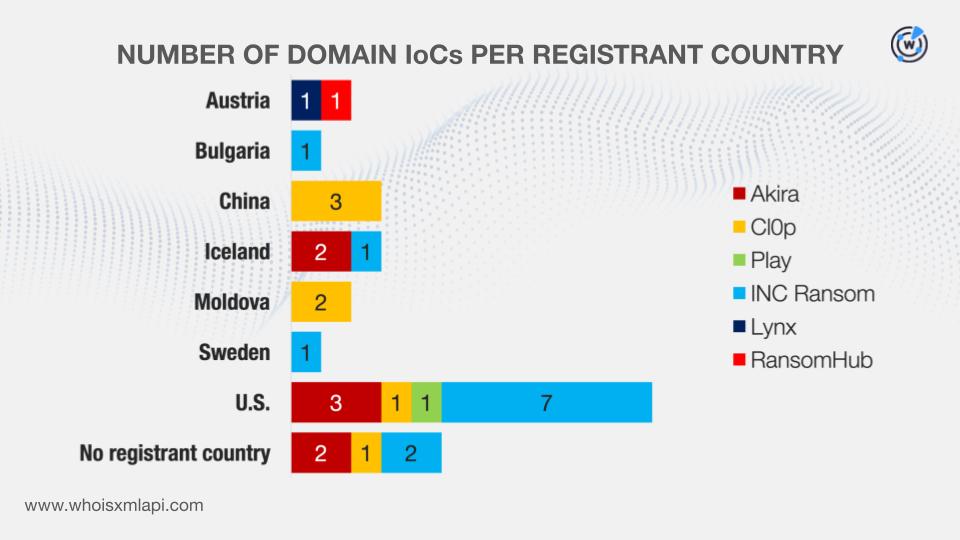
We then queried the 29 domains on WHOIS API and learned that:
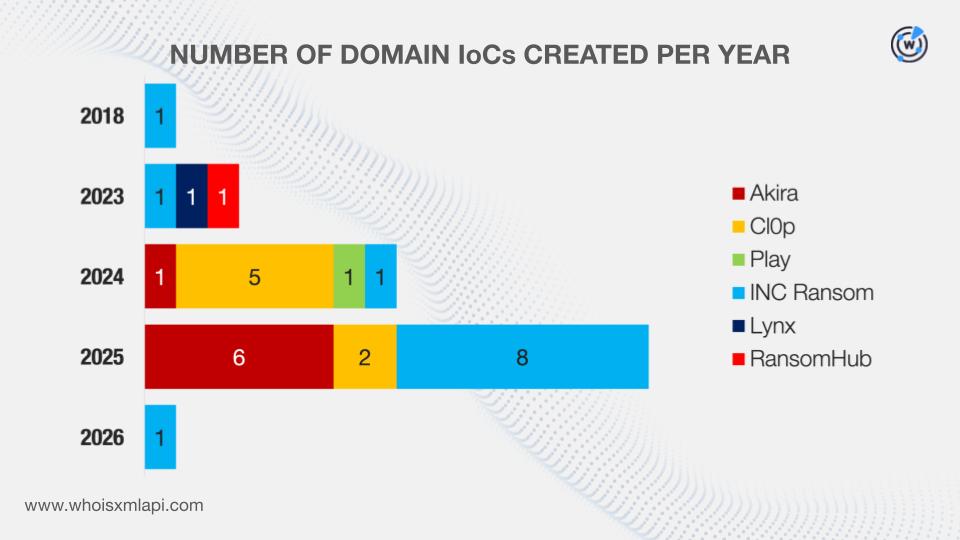
They were administered by 11 registrars.
While six domains did not have registrant countries on record, the remaining 23 were registered in seven countries.
DNS Chronicle API queries for the 28 domains revealed that they recorded 2,728 historical domain-to-IP resolutions over time. Take a look at more information on five domains with the oldest resolution dates below.
| RANSOMWARE | DOMAIN IoC | NUMBER OF DOMAIN-TO-IP RESOLUTIONS | DATES SEEN |
|---|---|---|---|
| Cl0p | in2pay[.]com | 229 | 02/06/17—03/12/26 |
| Cl0p | pubstorm[.]com | 116 | 02/06/17—01/25/26 |
| Akira | angryipscanner[.]org | 114 | 06/02/17—06/04/25 |
| Cl0p | he1p-center[.]com | 61 | 11/04/17—05/06/25 |
| Akira | opmanager[.]pro | 59 | 08/24/18—06/16/25 |
It is interesting to note that the five domains with the oldest resolution dates above were also affiliated with two of the oldest ransomware variants that made the top 10. Cl0p has been around since 2019 while Akira has been active since 2023.
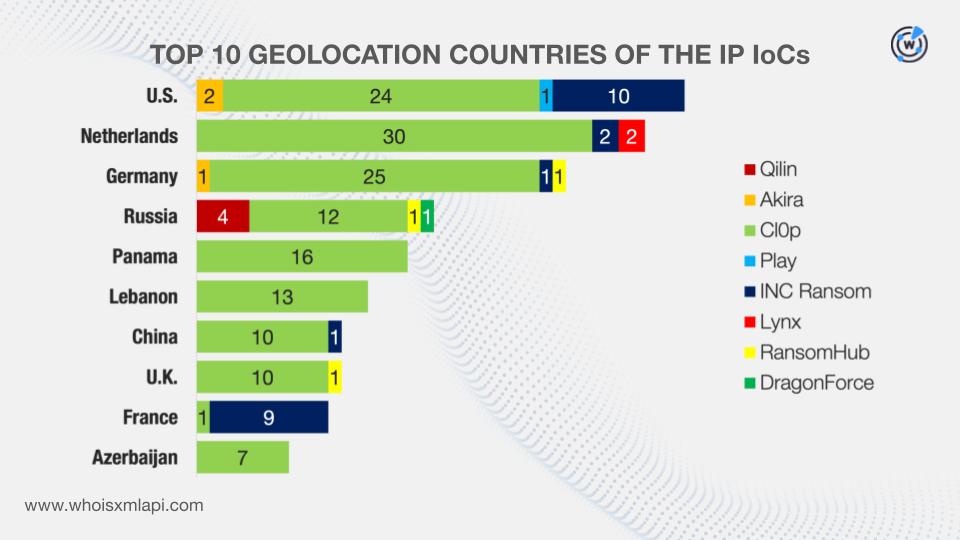
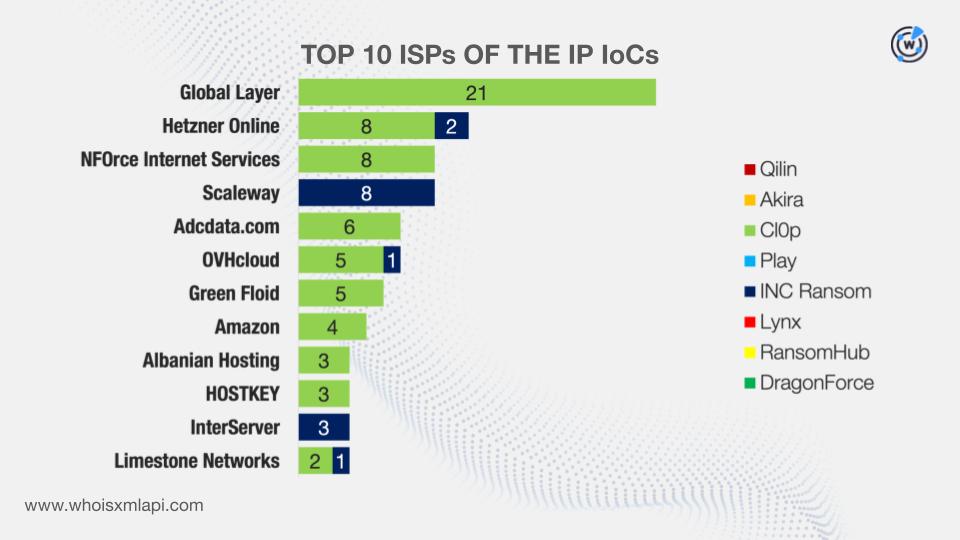
The reports connected to eight of the top 10 ransomware also identified 236 IP addresses as IoCs.
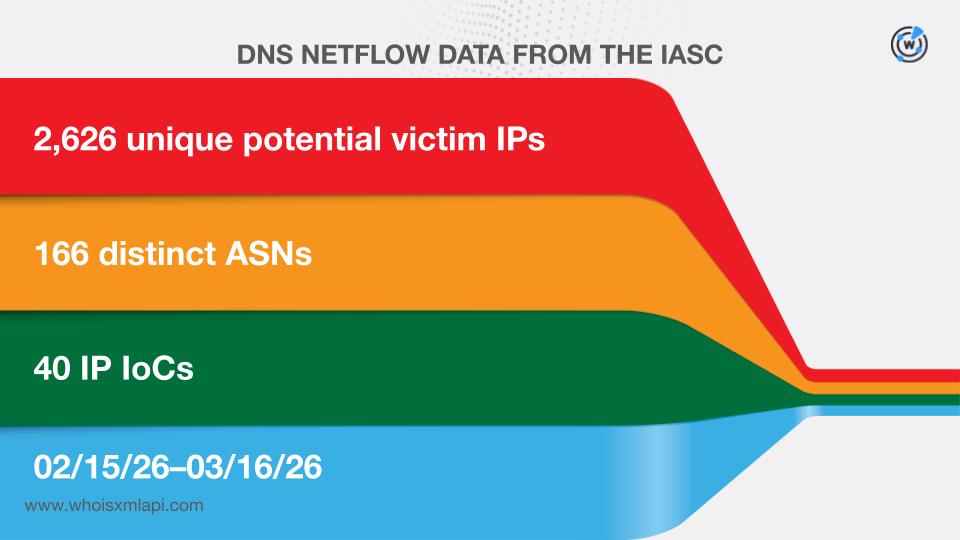
Sample network traffic data from the IASC revealed that 2,626 unique potential victim IP addresses under 166 distinct ASNs communicated with 40 of the IP IoCs between 15 February and 16 March 2026
We then queried the IP addresses on Bulk IP Geolocation Lookup and found out that:
While 122 IP addresses did not have ISPs on record, the remaining 114 were administered by 39 ISPs.
DNS Chronicle API queries for the IP addresses showed that 160 recorded 25,643 IP-to-domain resolutions over time. Here are more details for five examples.
| RANSOMWARE | IP IoC | NUMBER OF IP-TO-DOMAIN RESOLUTIONS | DATES SEEN |
|---|---|---|---|
| Cl0p | 46[.]161[.]27[.]113 | 27 | 02/05/17—10/29/22 |
| INC Ransom | 212[.]83[.]137[.]94 | 650 | 02/05/17—10/21/25 |
| RansomHub | 164[.]138[.]90[.]2 | 258 | 02/05/17—08/25/24 |
| Qilin | 176[.]113[.]115[.]209 | 223 | 11/01/20—01/17/26 |
| Akira | 109[.]205[.]195[.]21 | 172 | 07/02/25—08/04/25 |
Interestingly, all of the IP addresses with the oldest resolution dates were connected to the oldest ransomware in the top 10 list—Cl0p.
We also collated three email addresses affiliated with three ransomware for this study.
Our checks via the WhoisXML API MCP Server revealed that two were worth avoiding all forms of communication with specifically because they contained the names of two notorious ransomware—Qilin and Babuk. They also showed that none of them were used to register any domain, hence they will no longer appear in the next steps of our analysis.
According to our prompt results, for instance, while the email address named as an IoC qilin@exxxxxx[.]im was correctly formatted and not a catch-all, disposable, or free email address, the SMTP check showed it could not currently receive mail, meaning the mailbox may not be active or blocks SMTP verification. Also, while it was not necessarily tagged as malicious, users should note that Qilin is a well-known RaaS group. As such, the username “qilin’ could indicate it belongs to an actor operating in cybercriminal circles likely on or affiliated with the group.
For this step, we only focused on the 28 domains and 236 IP addresses identified as IoCs.
First, we queried the domains on WHOIS History API and discovered that 16 had 49 email addresses in their historical WHOIS records. Further scrutiny showed that 12 were public email addresses.
Our Reverse WHOIS API queries for the public email addresses led to the discovery of 8,491 unique email-connected domains after those already tagged as IoCs were filtered out.
This post only contains a snapshot of the full research. Download the complete findings and a sample of the additional artifacts on our website or contact us to discuss your intelligence needs for threat detection and response or other cybersecurity use cases.
Disclaimer: We take a cautionary stance toward threat detection and aim to provide relevant information to help protect against potential dangers. Consequently, it is possible that some entities identified as “threats” or “malicious” may eventually be deemed harmless upon further investigation or changes in context. We strongly recommend conducting supplementary investigations to corroborate the information provided herein.
Sponsored byIPv4.Global

Sponsored byVerisign

Sponsored byVerisign

Sponsored byRadix

Sponsored byWhoisXML API

Sponsored byDNIB.com

Sponsored byCSC
