


|
||
|
||
SOCRadar named the top 10 ransomware attacks of 2025, and guess which led the pack? The Salesforce SaaS supply chain attack that affected the company’s customers in the technology, aviation, and luxury sectors. Reports revealed that the Scattered Lapsus$ Hunters, a combination of Scattered Spider and ShinyHunters, were behind the campaign that transpired in mid to late 2025.
The attack exposed tens of millions of customer records and caused multisectoral operational disruption. And the threat actors got hold of OAuth tokens, CRM data, customer records, and support and travel data.
Jumping off two lists of IoCs published by LevelBlue and Seqrite, we compiled five domains, 33 IP addresses, and three email addresses. We excluded two domains, however, since they belonged to legitimate entities. That said, we analyzed 39 IoCs in the end, which led to these findings:
A sample of the additional artifacts obtained from our analysis is available for download from our website.
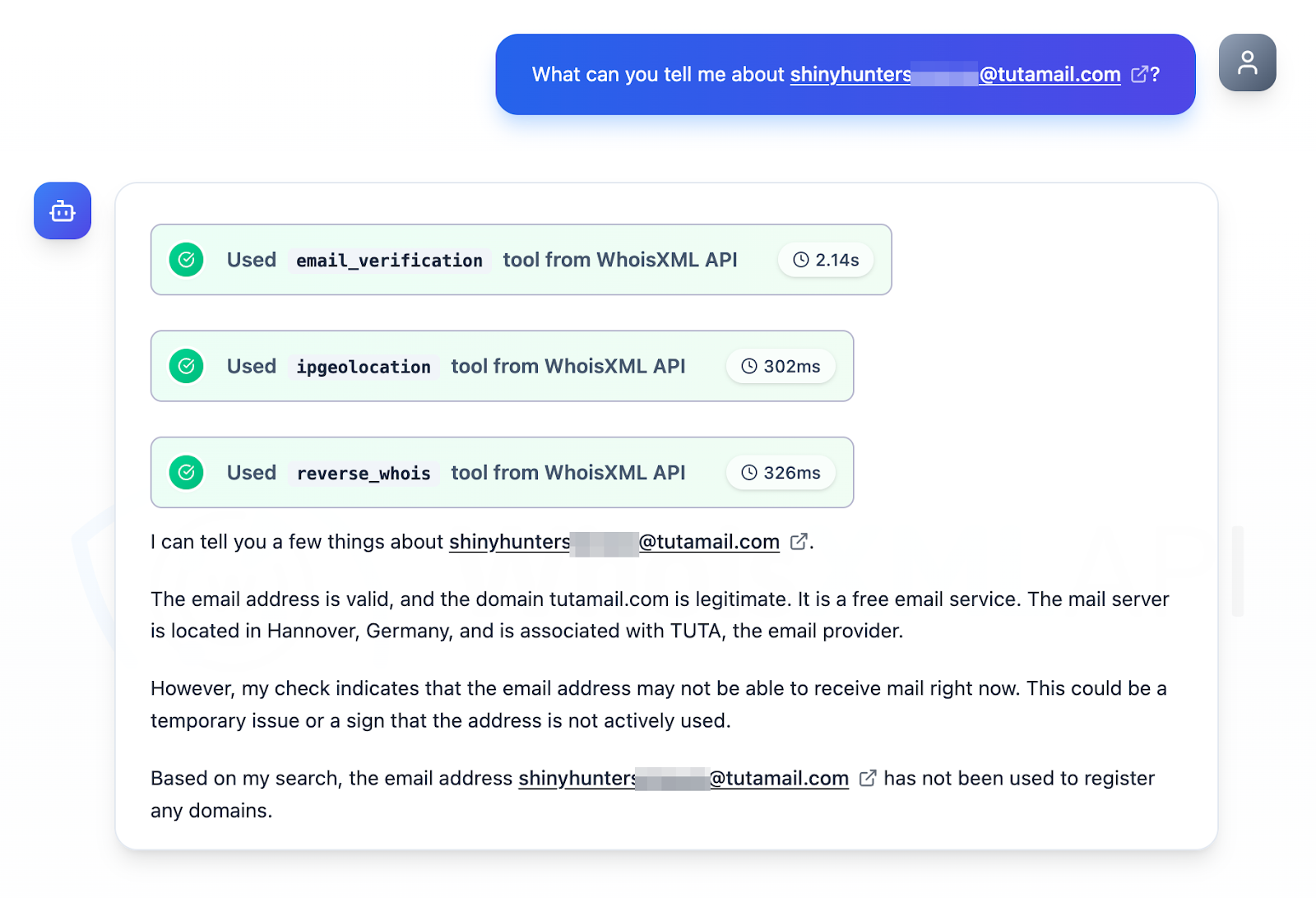
We examined the three email addresses identified as IoCs by querying them on Jake AI. The tool revealed that while they were all valid email addresses, they could not receive messages at present. None of them have also been used to register any domain, excluding them from our hunt for new artifacts.
Our First Watch Malicious Domains Data Feed findings revealed that one domain identified as an IoC—ticket-audemarspiguet[.]com—was registered with malicious intent on 20 June 2025, 76 days before the Seqrite report was published on 4 September 2025.
Next, we queried the three domains tagged as IoCs on WHOIS API and found out that they were created at around the same time, between 20 and 29 September 2025, with GMO Internet in Seychelles.
The results of our DNS Chronicle API queries for the three domains identified as IoCs supported our WHOIS findings above. Together, they posted 28 domain-to-IP resolutions over time. The domain ticket-audemarspiguet[.]com recorded the earliest resolution on 20 June 2025. The domain ticket-nike[.]com, meanwhile, posted the highest number of resolutions totaling 20 so far. Finally, the domain ticket-dior[.]com recorded the latest resolution on 29 June 2025. All these dates coincided with the three domains’ creation dates, too.
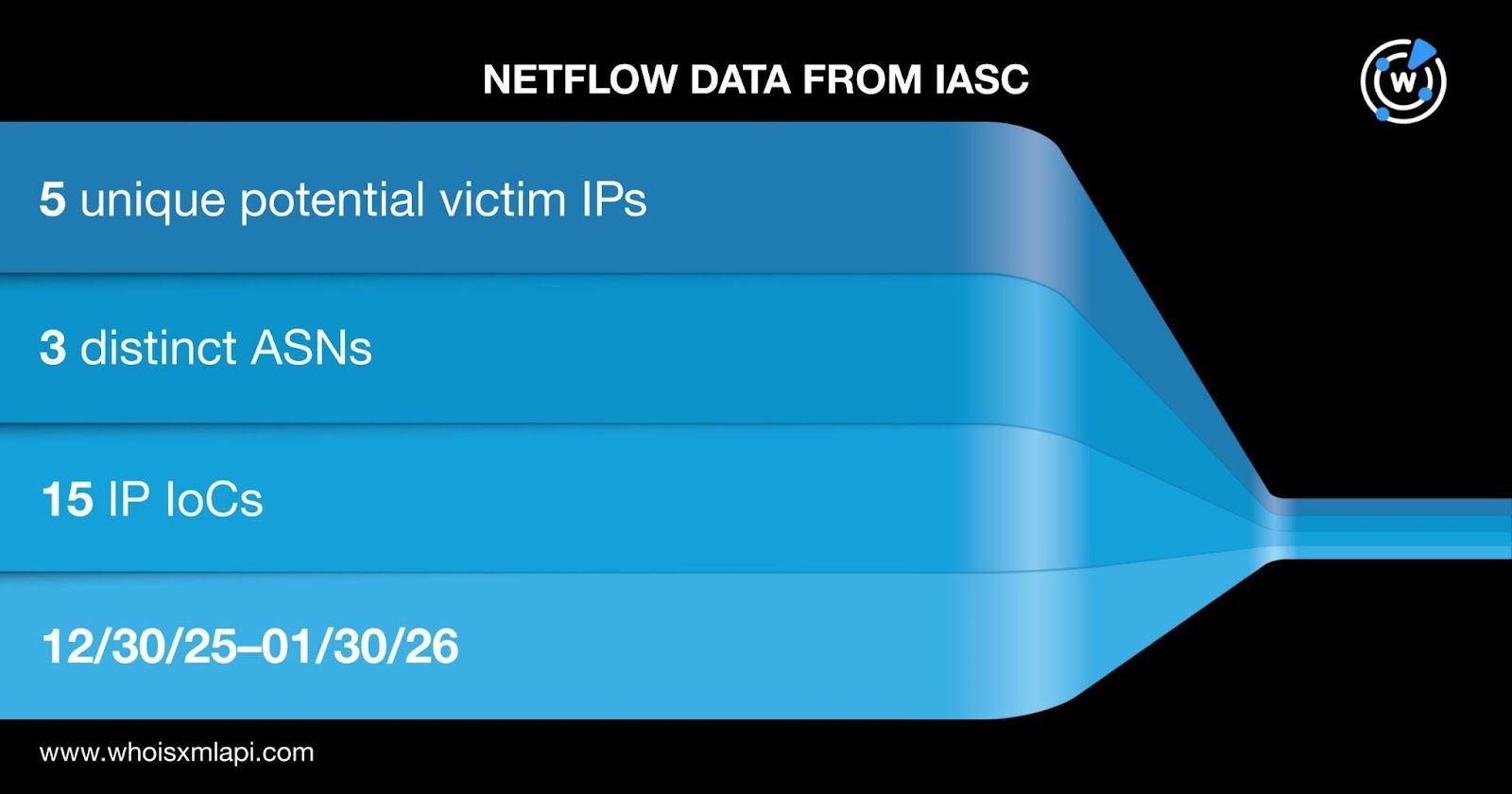
Sample network traffic data from the IASC showed that 1,722 unique potential victim IP addresses under 152 distinct ASNs communicated with 24 IP addresses tagged as IoCs between 30 December 2025 and 30 January 2026.
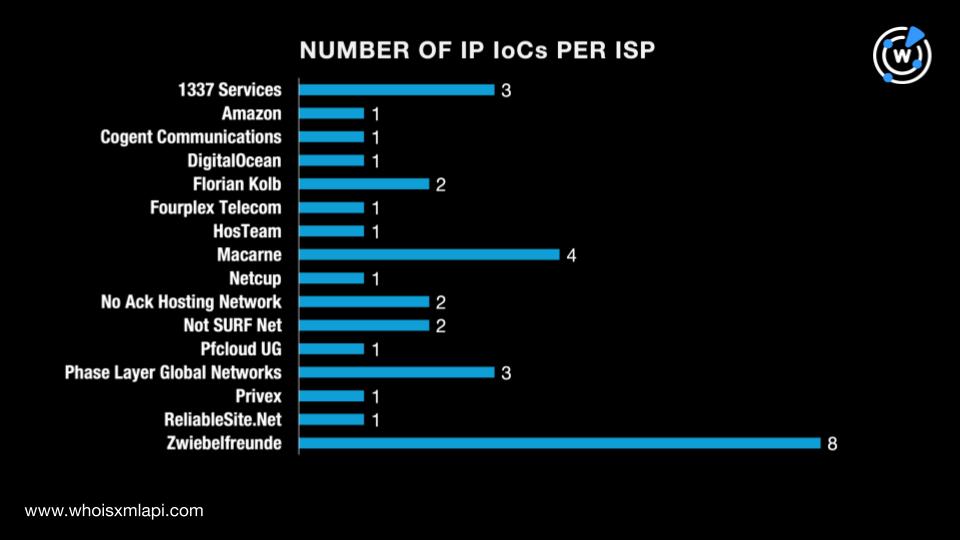
We then queried the 33 IP addresses identified as IoCs on Bulk IP Geolocation Lookup and discovered that:
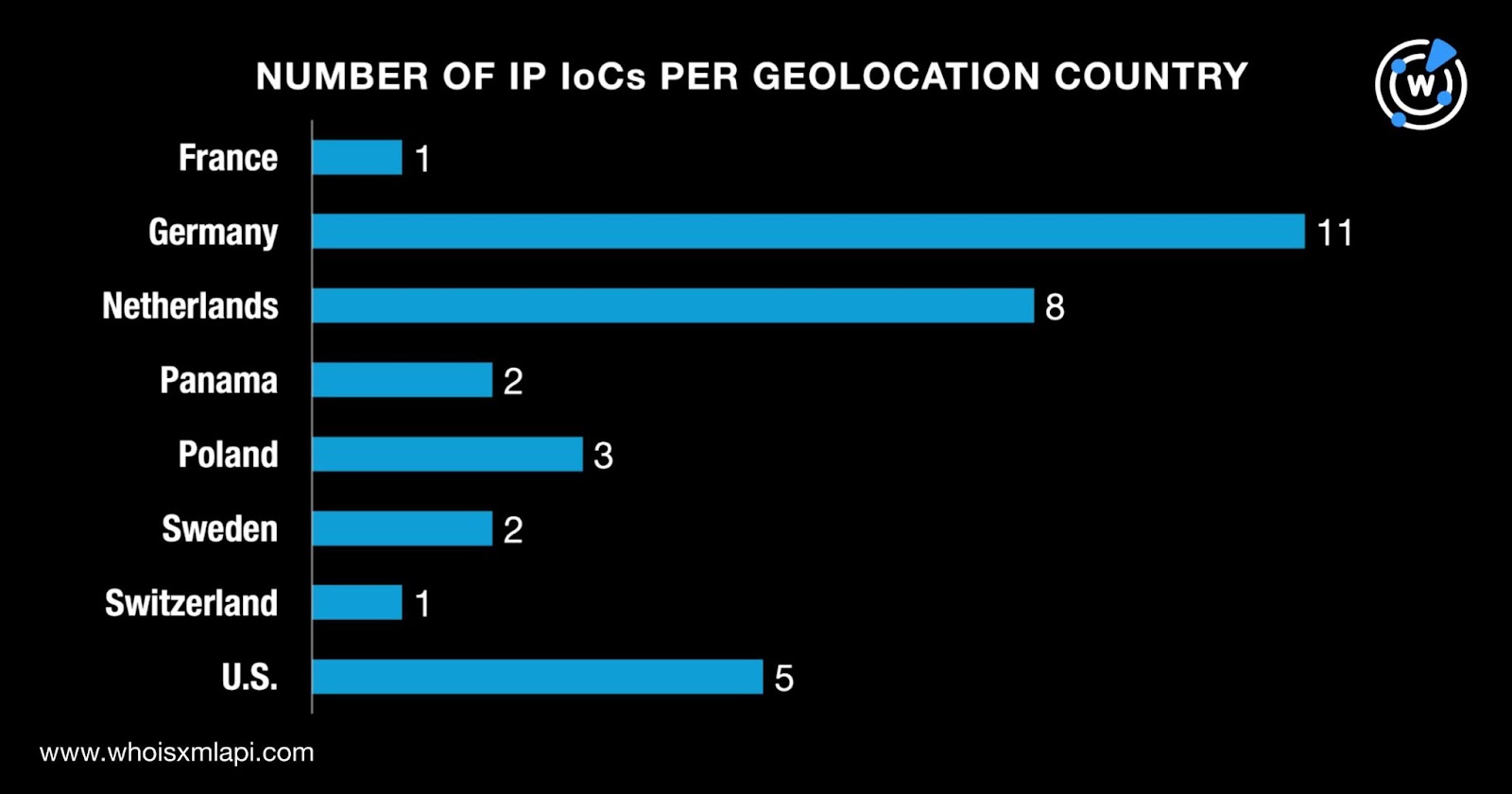
They were administered by 16 different ISPs with the majority (eight in all) managed by Zwiebelfreunde.
Next, we queried the 33 IP addresses tagged as IoCs on DNS Chronicle API and found out that only 25 had historical IP-to-domain resolutions over time. Together, they recorded 3,370 in all. The IP address 208[.]68[.]36[.]90 posted the earliest resolution as far back as 7 February 2017. Here are a few examples.
| IP IoC | NUMBER OF RESOLUTIONS | FIRST RESOLUTION DATE | LAST RESOLUTION DATE |
|---|---|---|---|
| 208[.]68[.]36[.]90 | 383 | 02/07/17 | 10/12/25 |
| 185[.]207[.]107[.]130 | 382 | 02/25/18 | 12/24/25 |
| 192[.]42[.]116[.]20 | 374 | 06/11/18 | 09/21/25 |
| 81[.]17[.]28[.]95 | 185 | 10/12/18 | 02/09/24 |
| 31[.]133[.]0[.]210 | 9 | 11/09/18 | 06/26/22 |
Our hunt for new connected artifacts started with WHOIS History API queries for the three domains identified as IoCs. We discovered that they had two unique email addresses in their historical WHOIS records. Both were public email addresses.
The results of our historical Reverse WHOIS API queries for the two public email addresses led to the discovery of 405 unique email-connected domains after those already tagged as IoCs were filtered out.
Threat Intelligence API queries for the email-connected domains showed that four have already been weaponized for attacks. The domain join-meets[.]com, for instance, has been associated with malware distribution from 28 July 2025 to 24 January 2026.
After that, we queried the 33 domains tagged as IoCs on DNS Lookup API and uncovered two unique IP addresses not on the list of IP IoCs.
According to Threat Intelligence API, both additional IP addresses have already figured in various attacks. The IP address 104[.]21[.]78[.]124, for example, was associated with malware distribution (29 October 2024—24 January 2026) and phishing (28 March 2023—29 November 2025).
Given the 33 IP addresses identified as IoCs and the two additional ones found above, we now had 35 for further analysis. Our Reverse IP API queries showed that 10 could be dedicated hosts. Together, they hosted 11 unique IP-connected domains after those already tagged as IoCs and the email-connected domains were filtered out.
Next, we looked more closely at the three domains identified as IoCs and deemed that they all started with the text string ticket-. Our Domains & Subdomains Discovery searches for the string led to the discovery of 7,900 unique string-connected domains after those already tagged as IoCs and the email- and IP-connected domains were filtered out. Here are a few examples.
| MALICIOUS STRING-CONNECTED DOMAIN | ASSOCIATED THREAT | DATE FIRST SEEN | DATE LAST SEEN |
|---|---|---|---|
| ticket-aviata[.]info | Malware distribution | 03/09/23 | 01/24/26 |
| ticket-escrow[.]com | Phishing | 01/10/26 | 01/11/26 |
| ticket-frankfurt[.]de | Phishing | 10/03/25 | 12/04/25 |
Our search for traces that the Salesforce supply chain attack of 2025 left behind in the DNS uncovered 8,318 new artifacts comprising 405 email-connected domains, two additional IP addresses, 11 IP-connected domains, and 7,900 string-connected domains.
We also discovered that one domain tagged as an IoC was deemed likely to turn malicious 76 days before being dubbed as such. Finally, 1,722 potential victim IP addresses communicated with 24 IP addresses identified as IoCs.
This post only contains a snapshot of the full research. Download the complete findings and a sample of the additional artifacts on our website or contact us to discuss your intelligence needs for threat detection and response or other cybersecurity use cases.
Disclaimer: We take a cautionary stance toward threat detection and aim to provide relevant information to help protect against potential dangers. Consequently, it is possible that some entities identified as “threats” or “malicious” may eventually be deemed harmless upon further investigation or changes in context. We strongly recommend conducting supplementary investigations to corroborate the information provided herein.
Sponsored byDNIB.com

Sponsored byWhoisXML API

Sponsored byVerisign

Sponsored byRadix

Sponsored byCSC

Sponsored byIPv4.Global

Sponsored byVerisign
