


|
||
|
||
Amid the ongoing conflict involving Iran, we could not help but wonder if the tension has extended online. That said, we sought to trace the DNS footprint of eight of the 10 known Iran-affiliated APT groups listed in S2W’s recently published “Iran APT Landscape Report: State-Sponsored Cyber Threats in an Era of Active Conflict.”
| APT GROUP | DESCRIPTION | IoC SOURCE | DATE PUBLISHED |
|---|---|---|---|
| APT42 | Also known as “UNC788,” “Charming Kitten,” or “TA453” and active since at least 2015, it has targeted the Middle East but also various industries in other regions | https://research.checkpoint.com/2025/iranian-educated-manticore-targets-leading-tech-academics/ | 06/25/25 |
| APT34 | Also known as “Helix Kitten” or “OilRig” and active since at least 2014, it has targeted Middle Eastern and international victims, specifically from the financial, government, energy, chemical, and telecommunications sectors | https://research.checkpoint.com/2024/iranian-malware-attacks-iraqi-government/ | 09/11/24 |
| MuddyWater | Also known as “Seedworm,” “MERCURY,” “Static Kitten,” “TEMP.Zagros,” “TA450,” or “Mango Sandstorm” and active since at least 2017, it has targeted government and private organizations in the telecommunications, local government, defense, and oil and natural gas sectors in the Middle East, Asia, Africa, Europe, and North America | https://www.huntress.com/blog/muddywater-attack-chain | 03/06/26 |
| CyberAv3ngers | Also known as “Soldiers of Solomon” and active since at least 2020, it has made disputed and false claims of critical infrastructure compromises in Israel | https://www.ic3.gov/CSA/2026/260407.pdf | 04/07/26 |
| BladedFeline | Known to be a subgroup of APT34 and active since at least 2017, it has targeted Iraqi and Kurdish government officials | https://www.welivesecurity.com/en/eset-research/bladedfeline-whispering-dark/ | 06/05/25 |
| Peach Sandstorm | Also known as “APT33,” “HOLMIUM,” or “Elfin” and active since at least 2013, it has targeted organizations in the aviation and energy sectors in the U.S., Saudi Arabia, and South Korea | https://blog.checkpoint.com/research/iran-nexus-password-spray-campaign-targeting-cloud-environments-with-a-focus-on-the-middle-east/ | 03/31/26 |
| Void Manticore | Also known as “Storm-842,” it has become notorious for conducting destructive wiping attacks and influence operations | https://research.checkpoint.com/2026/handala-hack-unveiling-groups-modus-operandi/ | 03/12/26 |
| Pioneer Kitten | Also known as “Fox Kitten,” “Yellow Dev 15,” “COBALT FOXGLOVE,” “Lemon Sandstorm,” “PARISITE,” or “UNC757” and active since at least 2017, it reportedly focuses on gaining and maintaining access to entities possessing sensitive information of likely intelligence interest to the Iranian government | https://www.cisa.gov/news-events/cybersecurity-advisories/aa24-241a | 08/08/24 |
While we were able to collate 190 network IoCs originally from the eight reports cited above, after processing (i.e., domain extraction from subdomains, legitimate domain filtering, and weeding out of inactive domains) aided by the WhoisXML API MCP Server we ended up with 191 unique IoCs comprising four subdomains, 136 domains, and 51 IP addresses for our analysis.
Utilizing our extensive WHOIS, DNS, and threat intelligence sources, our investigation led to these discoveries:
A sample of the additional artifacts obtained from our analysis is available for download from our website.
Before we proceed, note that only one of the APT groups—Pioneer Kitten—had subdomain IoCs, four in total.
The results of our WhoisXML API MCP Server queries for the four subdomain IoCs revealed that all were confirmed active malware distributors that shared identical infrastructure fingerprints and threat timelines. They seemed to be part of a coordinated campaign impersonating major cybersecurity and technology vendors to blend into enterprise network traffic.
Take a look at more information for two examples below.
| SUBDOMAIN IoC | WXA MCP SERVER FINDING |
|---|---|
| cloud[.]sophos[.]one | Likely chosen to blend in as a legitimate cloud/API service from trusted brand Sophos; consistent with the C&C infrastructure for a persistent malware campaign |
| fortigate[.]forticloud[.]online | Shares the infrastructure of cloud[.]sophos[.]one; part of a coordinated, multibrand impersonation campaign targeting Sophos and Fortinet, among others |
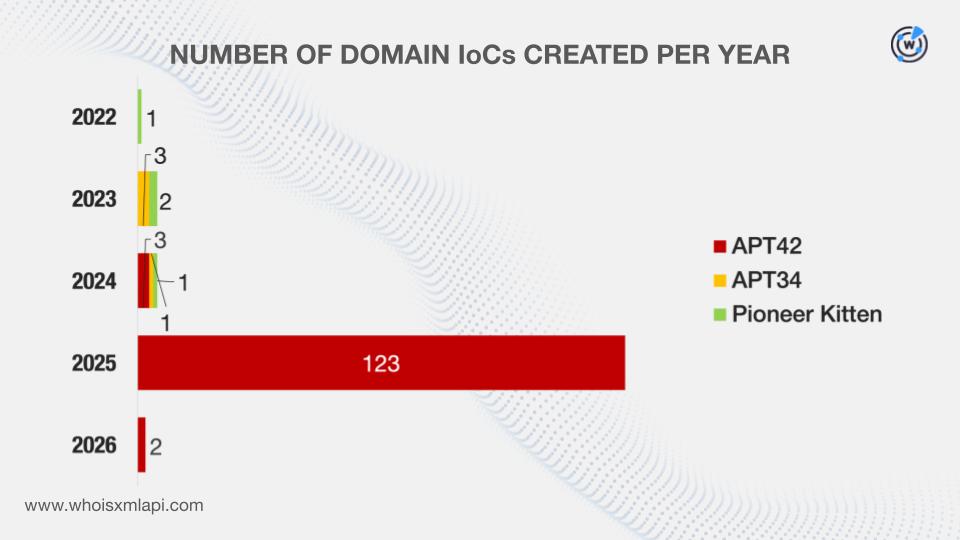
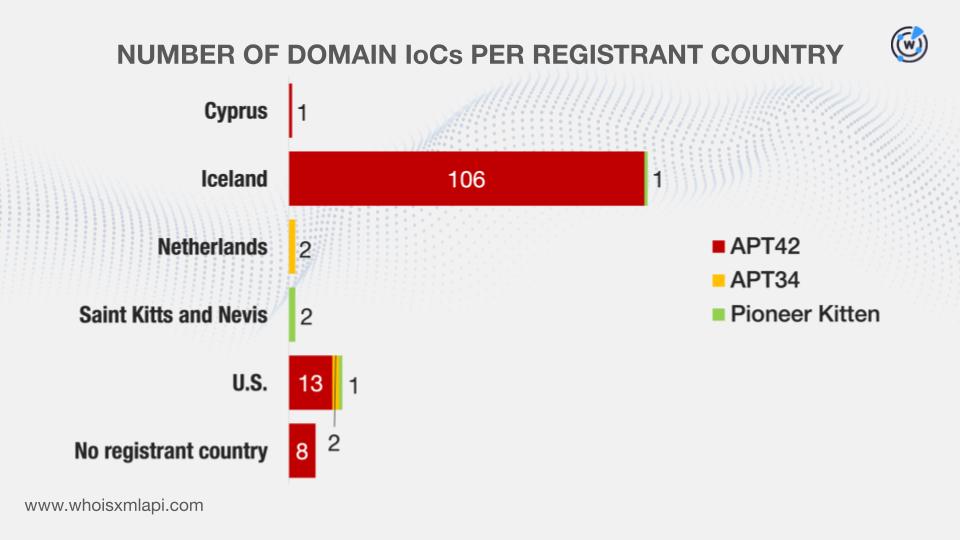
Note that only three of the APT groups—APT42, APT34, and Pioneer Kitten—had domain IoCs, 136 in all.
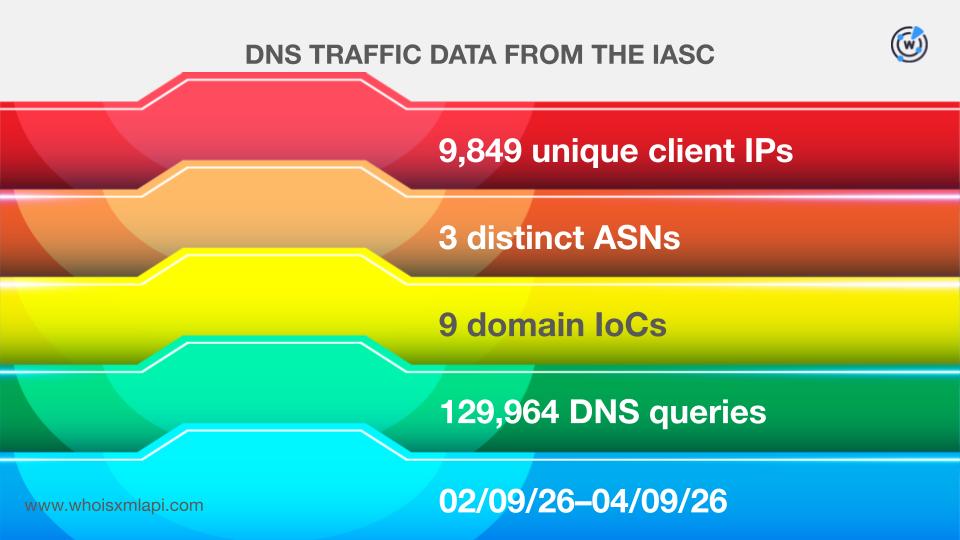
Sample network traffic data from the IASC revealed that 9,849 unique client IP addresses under three distinct ASNs communicated with nine domain IoCs all tied to APT42 between 9 February and 9 April 2026 via 129,964 DNS queries.
Our Typosquatting API searches, meanwhile, showed that one domain IoC connected to APT42 was bulk-registered with two look-alikes on 14 April 2025.
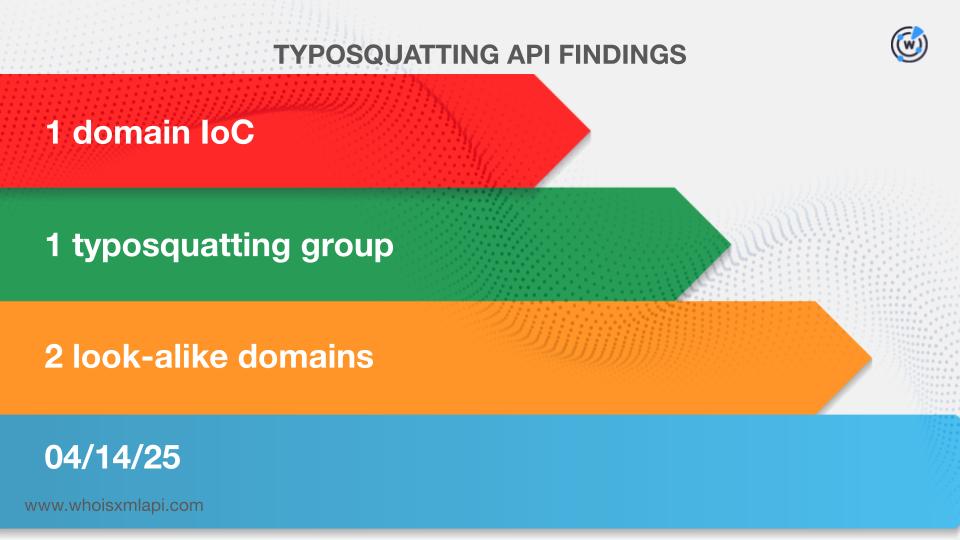
Specifically, the domain IoC work-meeting[.]info was bulk-registered with its look-alikes workmeeting[.]info and workmeeting[.]online. In addition, while the domain IoC was administered by Namecheap, the look-alikes were registered with One.com.
Next up, we scoured the First Watch Malicious Domains Data Feed and discovered that 73 domain IoCs for two of the three APT groups—APT42 and APT34—were deemed likely to have been registered with malicious intent.
Here are more details for five examples.
| GROUP | DOMAIN IoC | FIRST WATCH DATE | NUMBER OF DAYS BEFORE THE REPORT DATE |
|---|---|---|---|
| APT42 | world-shop[.]online | 03/28/24 | 454 |
| APT42 | live-meet[.]cloud | 09/30/24 | 268 |
| APT42 | top-game[.]online | 10/19/24 | 249 |
| APT42 | live-meet[.]info | 01/18/25 | 158 |
| APT34 | iqwebservice[.]com | 10/31/23 | 316 |
After that, we queried the domain IoCs on WHOIS API and filled in gaps using details from Domain Info API. We found out that:
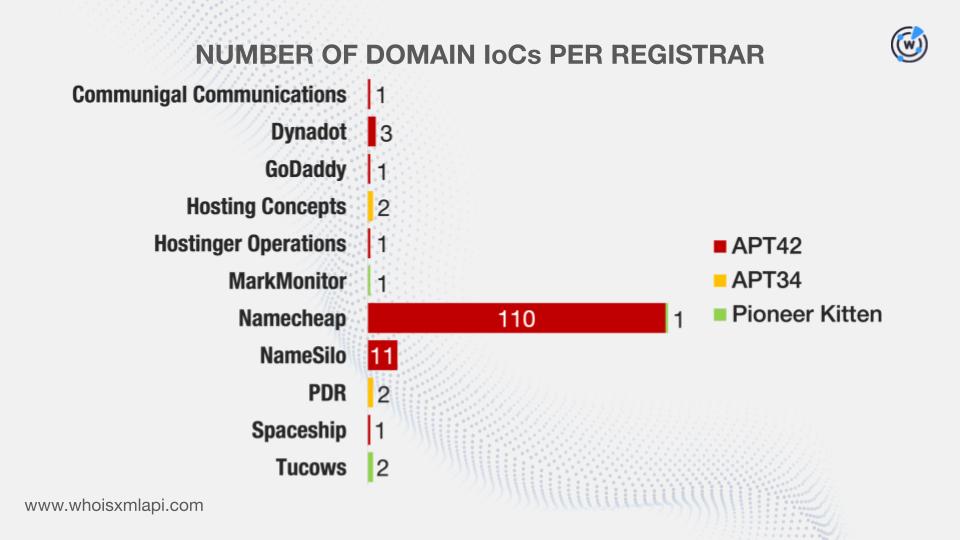
The APT42, APT34, and Pioneer Kitten domains were administered by seven, two, and three registrars, respectively.
While eight APT42 domains did not have registrant countries on record, the remaining APT42, APT34, and Pioneer Kitten domains were registered in three, two, and three countries, respectively.
Finally, we queried the domain IoCs on DNS Chronicle API and learned that:
All in all, 130 of the domain IoCs chalked up 5,455 historical domain-to-IP resolutions as of this writing.
Take a look at more information for five examples below.
| GROUP | DOMAIN IoC | NUMBER OF DOMAIN-TO-IP RESOLUTIONS | DATES SEEN |
|---|---|---|---|
| APT42 | backback[.]info | 362 | 02/23/25–03/07/26 |
| APT42 | rap-art[.]info | 361 | 02/23/25–03/10/26 |
| APT42 | arrow-click[.]info | 360 | 03/01/25–03/04/26 |
| APT34 | asiacall[.]net | 14 | 02/05/17–08/02/24 |
| Pioneer Kitten | sophos[.]one | 140 | 06/02/20–04/03/26 |
It is worth noting that 50 APT42 and three Pioneer Kitten domains continued to resolve to IP addresses in 2026.
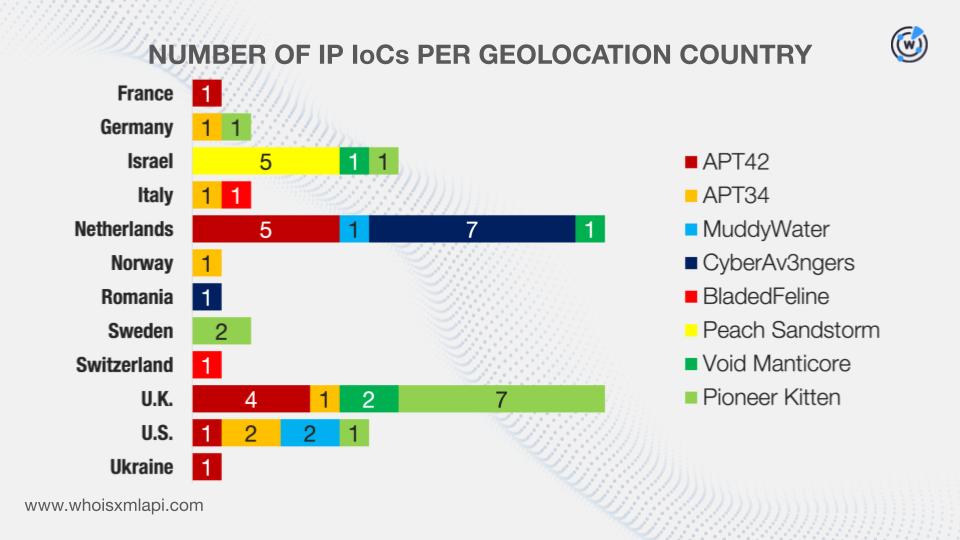
Next, we analyzed 51 IP IoCs for all of the eight APT groups. Note, however, that one IP address was used by two groups so this section will feature 52 IP addresses in all.
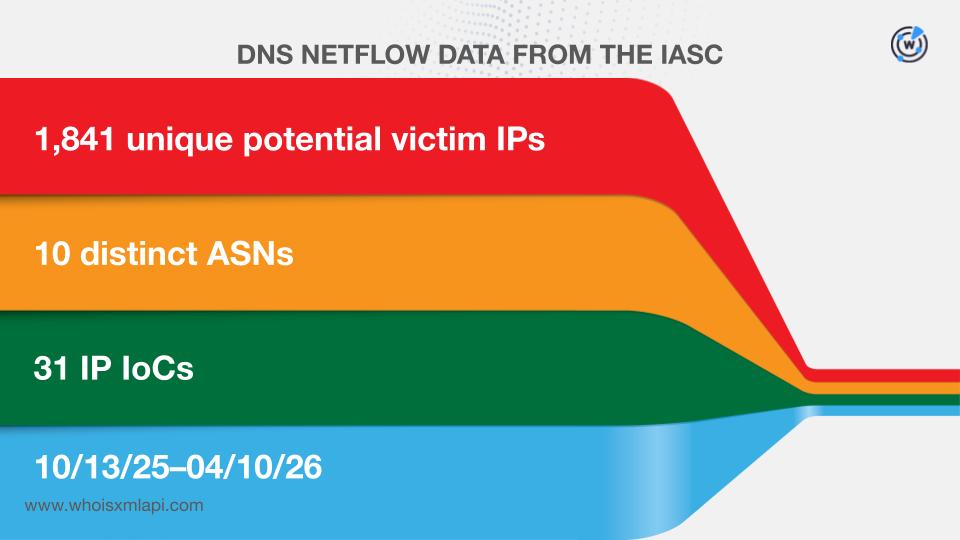
First, sample network traffic data from the IASC revealed that 1,841 IP addresses that could belong to victims under 10 distinct ASNs communicated with 31 of the IP IoCs between 13 October 2025 and 10 April 2026.
A Bulk IP Geolocation Lookup for the IP addresses, meanwhile, showed that:
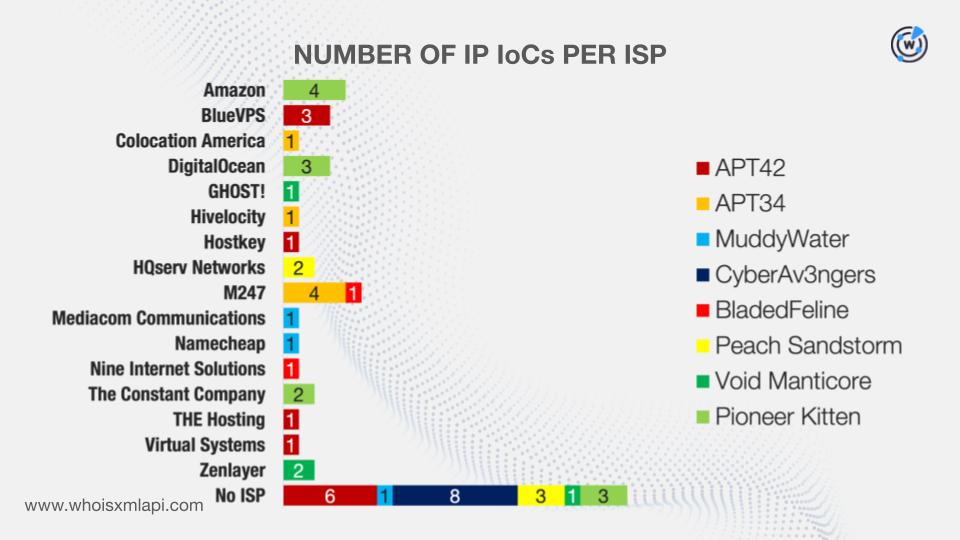
While 22 IP addresses did not have ISPs on record, the remaining 30 were administered by 16 ISPs split into the following per group:
Finally, from the results of our DNS Chronicle API queries, we learned that:
Here are more details for eight examples.
| GROUP | IP IoC | NUMBER OF IP-TO-DOMAIN RESOLUTIONS | DATES SEEN |
|---|---|---|---|
| APT42 | 146[.]19[.]254[.]238 | 1,000 | 04/06/25–06/10/25 |
| APT34 | 91[.]132[.]95[.]117 | 78 | 09/23/19–08/02/24 |
| MuddyWater | 162[.]0[.]230[.]185 | 1,000 | 09/05/20–07/24/21 |
| CyberAv3ngers | 185[.]82[.]73[.]162 | 12 | 05/18/19–03/21/21 |
| BladedFeline | 178[.]209[.]51[.]61 | 267 | 02/07/17–08/30/24 |
| Peach Sandstorm | 185[.]191[.]204[.]203 | 38 | 12/31/17–02/27/26 |
| Void Manticore | 82[.]25[.]35[.]25 | 515 | 02/05/17–04/05/26 |
| Pioneer Kitten | 193[.]149[.]187[.]41 | 1,000 | 12/29/22–07/21/25 |
It is also interesting to note that five APT42, two Peach Sandstorm, three Void Manticore, and two Pioneer Kitten IP addresses continued to resolve domains in 2026.
After obtaining more insights into the IoCs related to the eight APT groups, we then sought to uncover additional artifacts.
First off, we queried the 136 domain IoCs on WHOIS History API and discovered that 121 had 148 unique email addresses in their historical WHOIS records. Of these, 15 turned out to be public email addresses.
This post only contains a snapshot of the full research. Download the complete findings and a sample of the additional artifacts on our website or contact us to discuss your intelligence needs for threat detection and response or other cybersecurity use cases.
Disclaimer: We take a cautionary stance toward threat detection and aim to provide relevant information to help protect against potential dangers. Consequently, it is possible that some entities identified as “threats” or “malicious” may eventually be deemed harmless upon further investigation or changes in context. We strongly recommend conducting supplementary investigations to corroborate the information provided herein.
Sponsored byIPv4.Global

Sponsored byVerisign

Sponsored byVerisign

Sponsored byRadix

Sponsored byWhoisXML API

Sponsored byCSC

Sponsored byDNIB.com
