


|
||
|
||
Securonix recently published their analysis of stealthy campaign PHALT#BLYX, which targeted the European hospitality sector. They used click-fix social engineering, fake CAPTCHAs, and fake BSOD pages to trick users into downloading DCRat so the threat actors could take full remote access to infected systems and drop secondary payloads. The researchers cited 11 original IoCs in their report comprising one URL, seven domains, and three IP addresses.
After extracting an additional domain from the URL, we analyzed 12 IoCs in total—one URL, eight domains, and three IP addresses. Our investigation uncovered these findings:
A sample of the additional artifacts obtained from our analysis is available for download from our website.
According to Securonix, the PHALT#BLYX attack started with the threat actors sending phishing emails to mostly European users. The potential victims were tricked into accessing a fake booking[.]com CAPTCHA page. Those who fell for the ruse then saw a fake BSOD page while DCRat was silently dropped onto their systems.
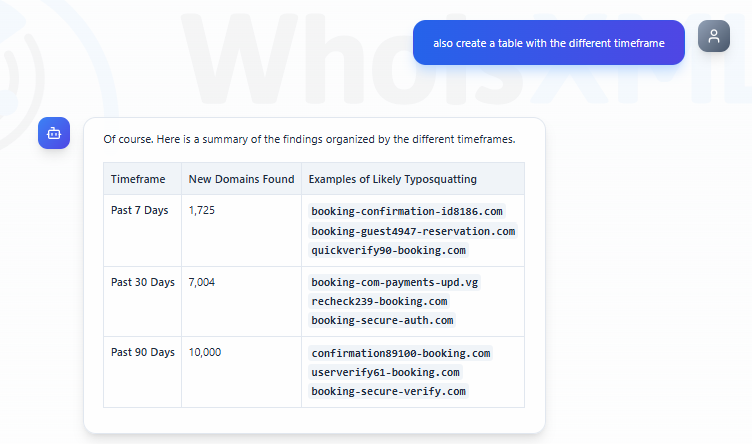
We took a closer look at booking[.]com using Jake AI and discovered that while the domain was legitimate, cyber attackers could be typosquatting on its popularity. In fact, we learned how many of its look-alikes were registered in the past seven, 30, and 90 days, along with some examples.
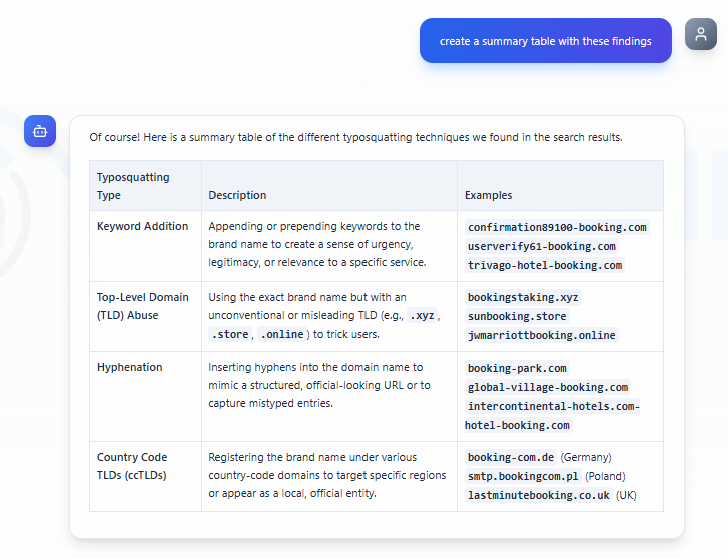
Our AI tool also clued us in to the various typosquatting methods that could have been used to mimic the site with examples as well.
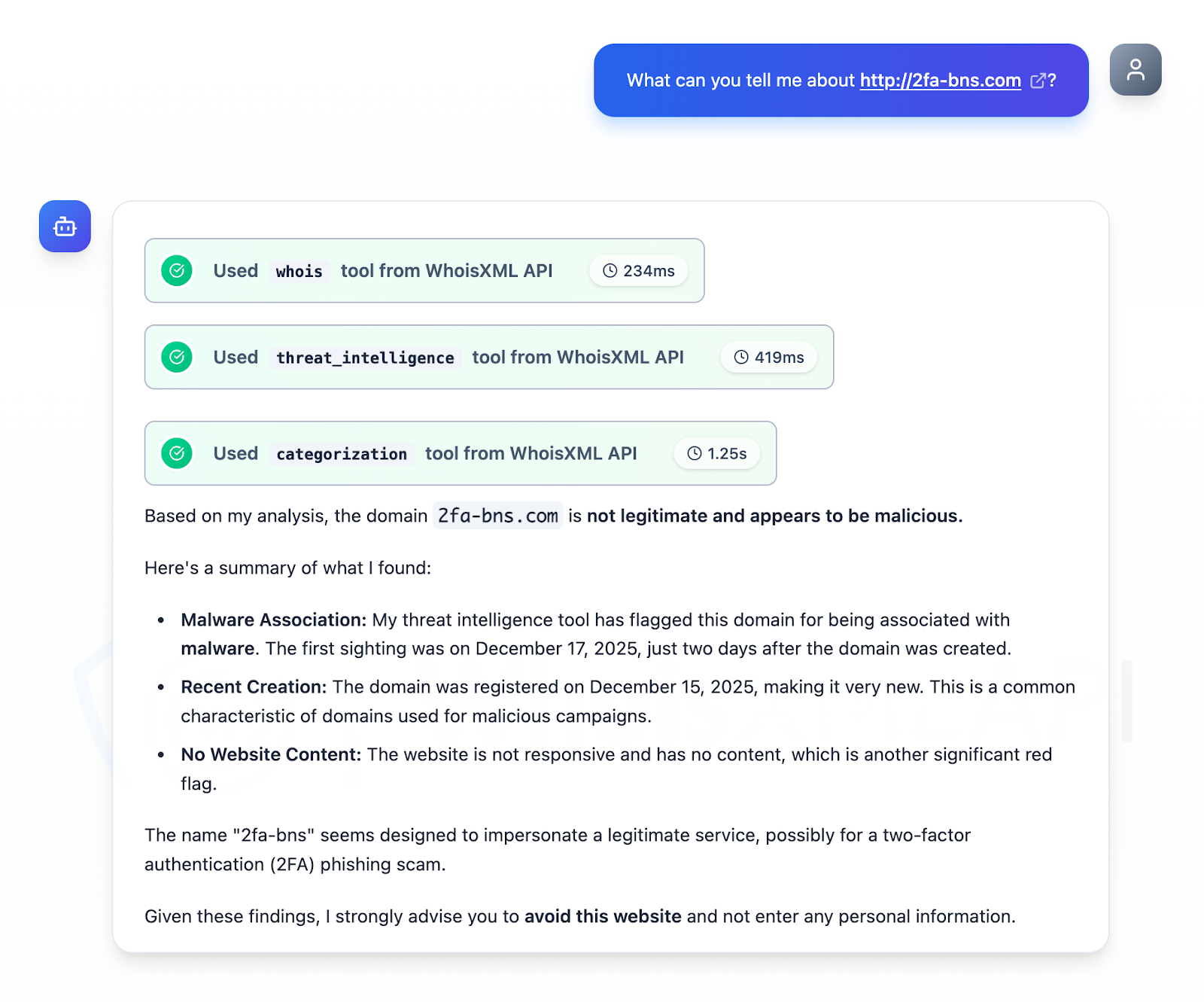
A sole URL was also identified as an IoC and we dug up more information about it via Jake AI, too. We learned that the site has been associated with malware distribution since 17 December 2025, two days after its creation. The site it led to did not have content as well. Interestingly, the site name 2fa-bns could have been designed to impersonate a legitimate service potentially for a 2FA phishing scam.
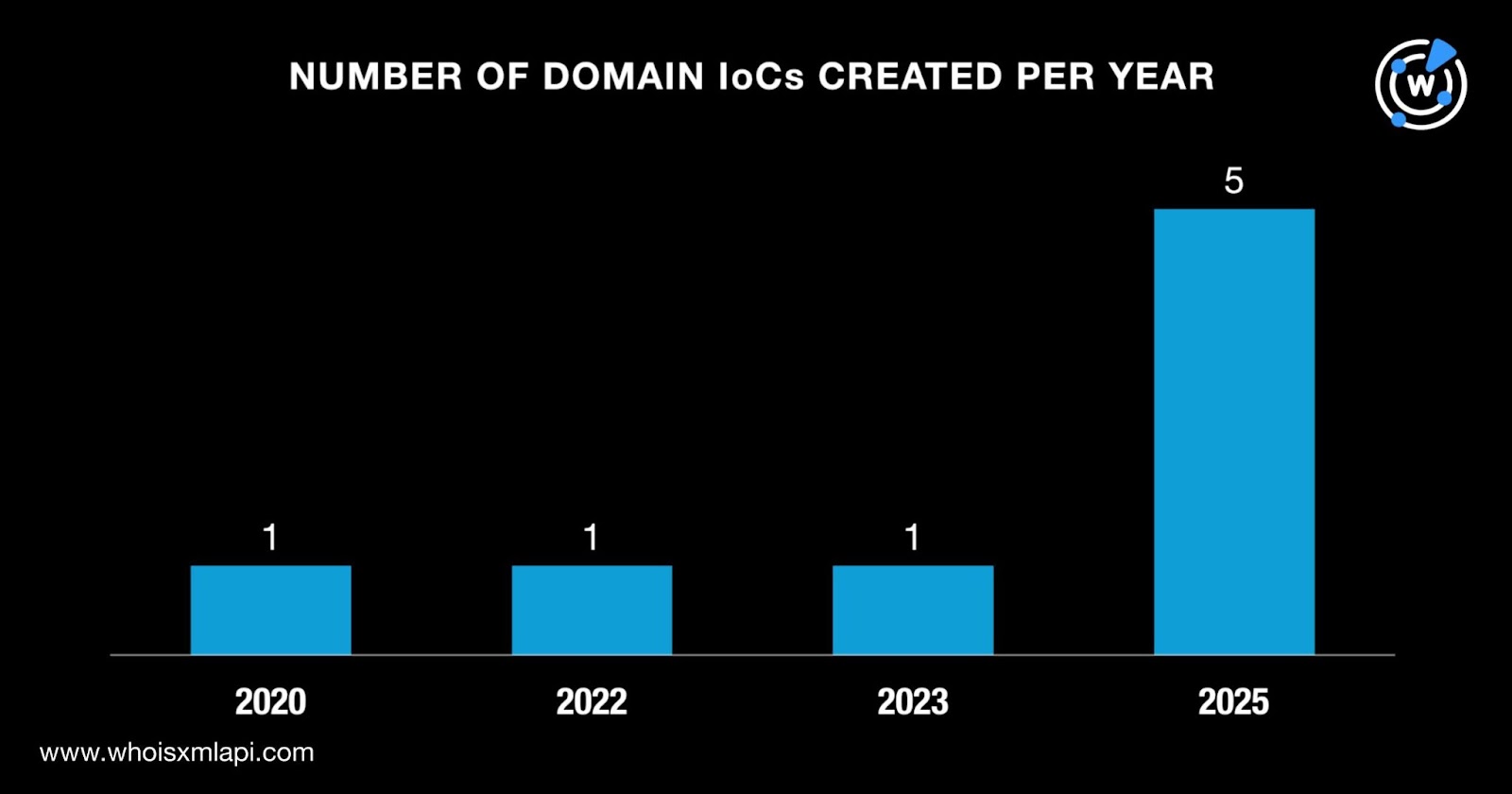
Our First Watch Malicious Domains Data Feed query results revealed that three domains identified as IoCs were registered with malicious intent. They were classified as malicious 28—177 days before the report’s publication on 6 January 2026.
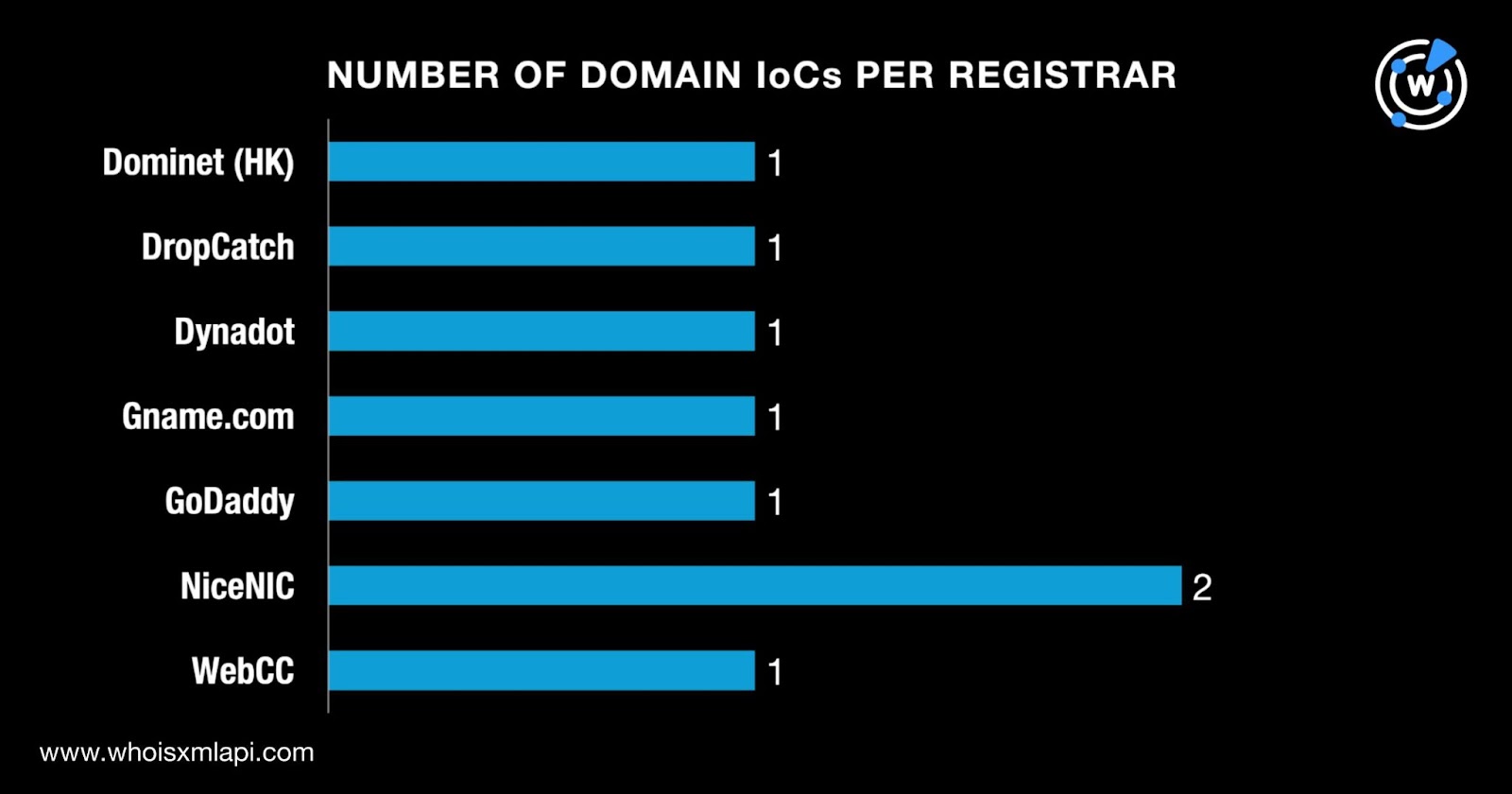
Next, we queried the eight domains identified as IoCs on WHOIS API and discovered that:
They were administered by six different registrars led by NiceNIC.
They were registered in five different countries, with a majority in the U.S.
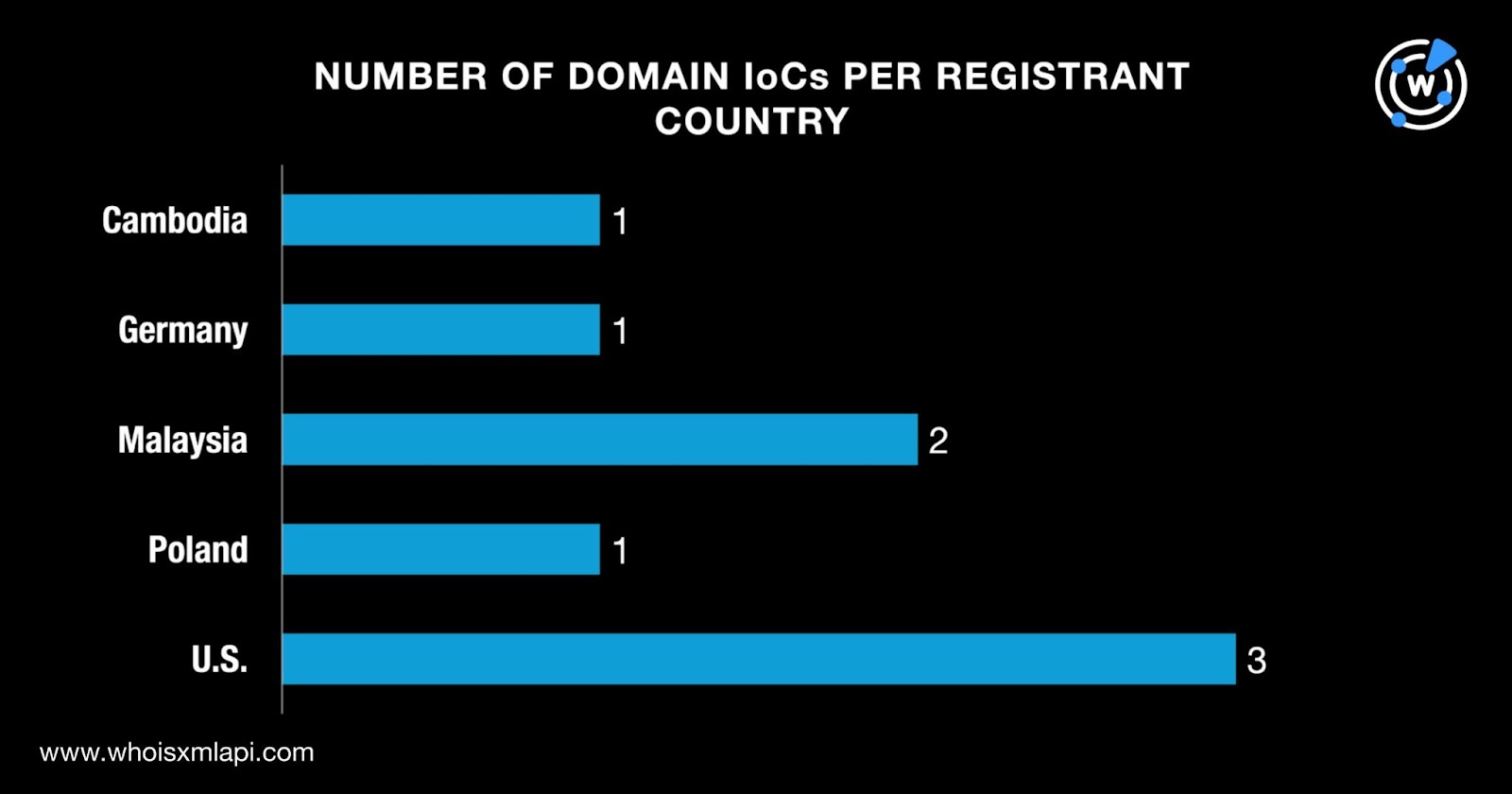
The differences in registrar and registrant country could be a misdirection tactic the threat actors employed to evade the prying eyes of law enforcement agencies as to their actual location, which, according to the researchers, was in Russia (i.e., not even on the list of registrant countries).
Finally, DNS Chronicle API queries for the eight domains identified as IoCs showed that seven recorded 523 historical domain-to-IP resolutions over time. The domain asj88[.]com’s oldest resolution was recorded on 5 February 2017.
| DOMAIN IoC | NUMBER OF RESOLUTIONS | FIRST RESOLUTION DATE | LAST RESOLUTION DATE |
|---|---|---|---|
| asj88[.]com | 186 | 02/05/17 | 01/09/26 |
| wmk77[.]com | 171 | 04/29/17 | 01/07/26 |
| asj99[.]com | 154 | 11/03/17 | 06/13/24 |
Given the discrepancies between the WHOIS creation dates (i.e., 2023, 2025, and 2022) and first domain-to-IP resolution dates (i.e., 2017) for the three domains above, we could infer that they may have been reregistered for the campaign’s use. And while one of them stopped actively resolving to an IP address in 2024, two remain active to date.
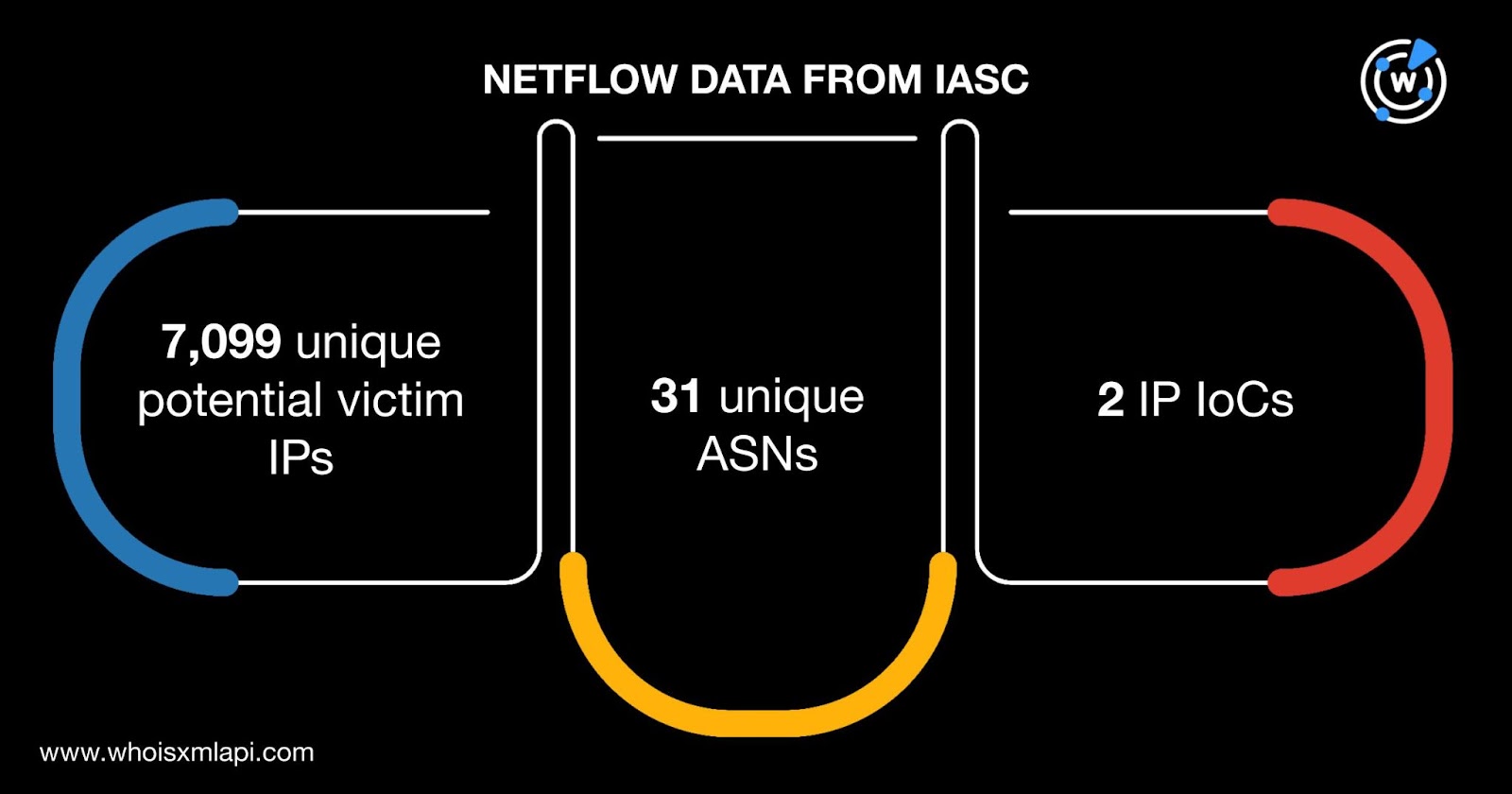
Sample network traffic data from the IASC revealed that 7,099 unique potential victim IP addresses under 31 distinct ASNs communicated with two IP addresses identified as IoCs between 9 September 2025 and 16 January 2026.
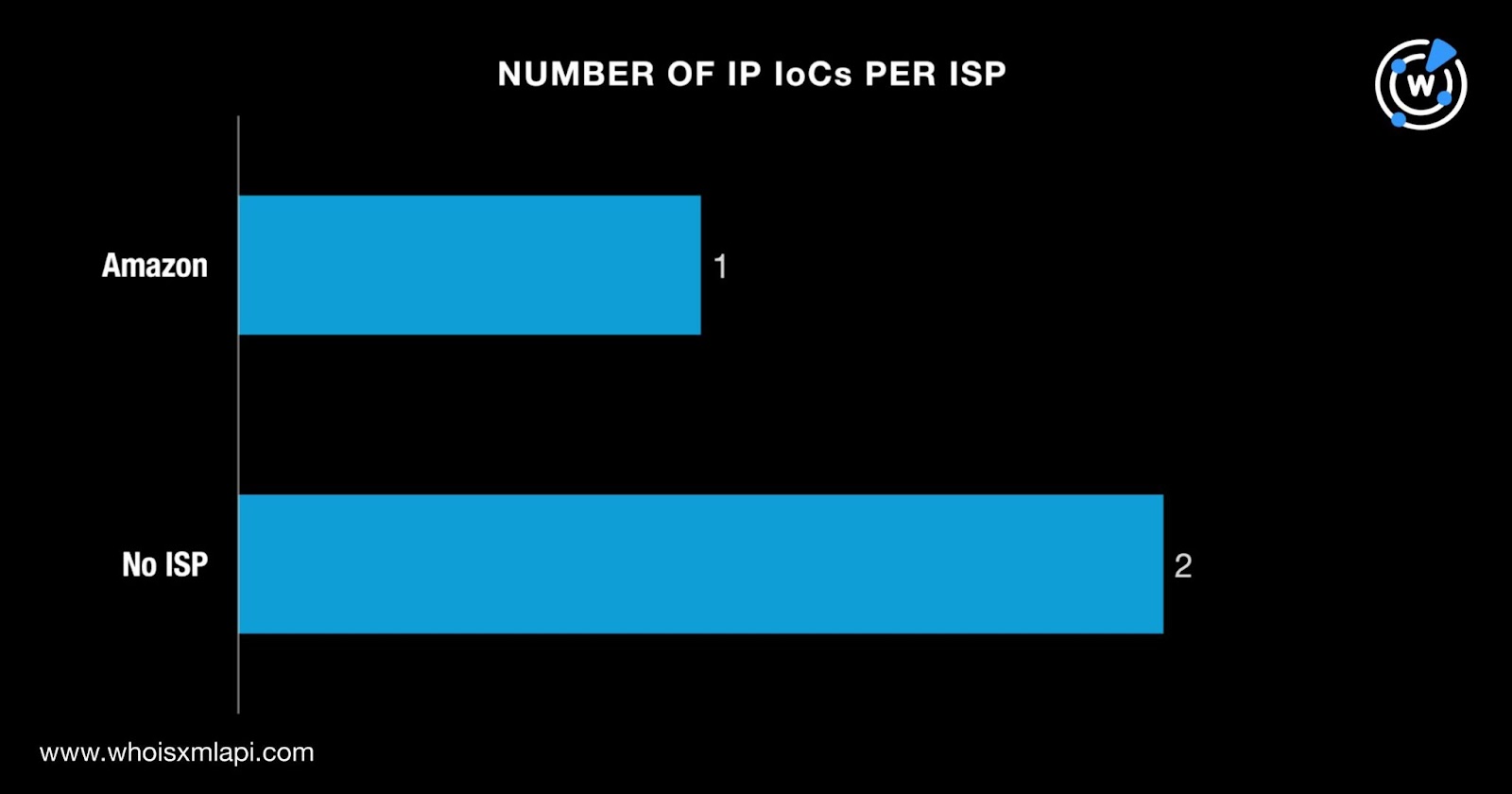
A Bulk IP Geolocation Lookup query for the three IP addresses identified as IoCs showed that:
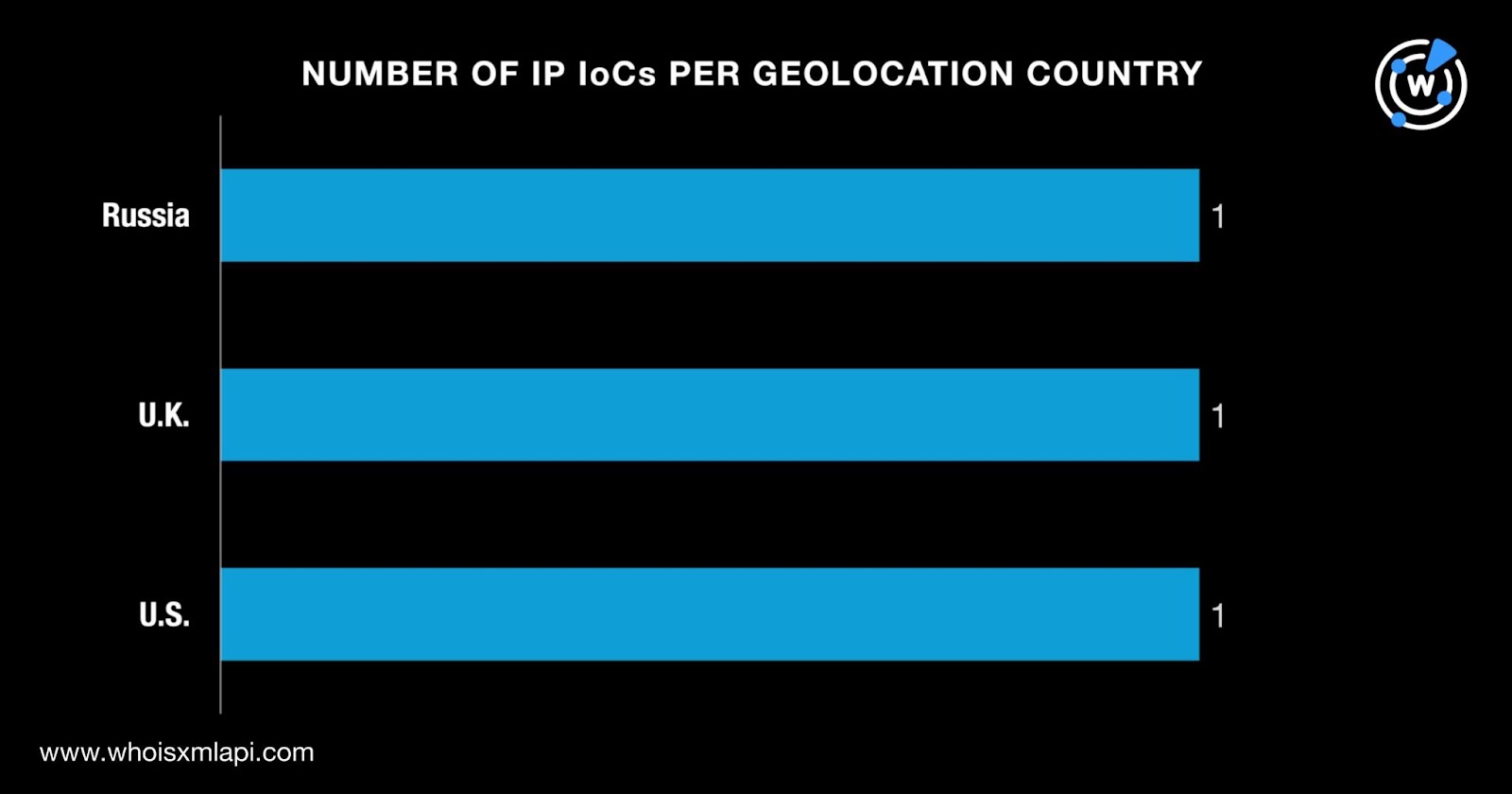
While two IP addresses did not have ISPs on record, one was administered by Amazon.
Our DNS Chronicle API query results for the three IP addresses identified as IoCs, meanwhile, revealed that two recorded 1,015 historical IP-to-domain resolutions over time. The IP address 194[.]169[.]163[.]140 recorded its first resolution on 23 January 2021.
We kicked off our search for new artifacts by querying the eight domains identified as IoCs on WHOIS History API. We discovered that six had 32 unique email addresses in their historical WHOIS records. Of these, 13 were public email addresses.
We then queried 13 email addresses on Reverse WHOIS API and found out that while none of them were present in current WHOIS records, all of them appeared in historical records. After excluding two email addresses that could belong to domainers, we uncovered 21,638 unique email-connected domains after those already identified as IoCs were filtered out.
Threat Intelligence API queries for the email-connected domains showed that four have already been weaponized for various attacks. An example is cp57[.]top, which was used to distribute malware from 9 March 2023 to 14 January 2026.
This post only contains a snapshot of the full research. Download the complete findings and a sample of the additional artifacts on our website or contact us to discuss your intelligence needs for threat detection and response or other cybersecurity use cases.
Disclaimer: We take a cautionary stance toward threat detection and aim to provide relevant information to help protect against potential dangers. Consequently, it is possible that some entities identified as “threats” or “malicious” may eventually be deemed harmless upon further investigation or changes in context. We strongly recommend conducting supplementary investigations to corroborate the information provided herein.
Sponsored byRadix

Sponsored byCSC

Sponsored byWhoisXML API

Sponsored byVerisign

Sponsored byIPv4.Global

Sponsored byDNIB.com

Sponsored byVerisign
