

The promises of quantum computing, artificial intelligence, and other advancing technologies sound like magic. However, even magic is subject to the laws of economics. And even quantum computers are “legal things…technological tools that are bound to affect our lives in a tangible manner,” as Valentin Jeutner explains in The Quantum Imperative: Addressing the Legal Dimension of Quantum Computers. Analogous to Asimov’s Three Laws of Robotics, Professor Jeutner proposes a three-part “quantum imperative,” which “provides that regulators and developers must ensure that the development of quantum computers. more
 I recently attended a workshop on Lessons Learned from 40 Years of the Internet, and the topic of the Internet as a Public Utility in the context of national regulatory frameworks came up. For me, 40 years is just enough time to try and phrase an answer to the big policy question: Has the Internet been a success in the experiment of using market forces to act as an efficient distributor of a public good? Or has it raised more issues than it has addressed? more
I recently attended a workshop on Lessons Learned from 40 Years of the Internet, and the topic of the Internet as a Public Utility in the context of national regulatory frameworks came up. For me, 40 years is just enough time to try and phrase an answer to the big policy question: Has the Internet been a success in the experiment of using market forces to act as an efficient distributor of a public good? Or has it raised more issues than it has addressed? more
More than 1,000 experts in the artificial intelligence community have called for an immediate pause on the development of "giant" AI systems like GPT-4 for at least six months. more
A new study conducted by British researchers has unveiled a potentially concerning form of cyber threat where hackers can extract personal data just by listening to someone type. more
 We all have a creative side, so consider meeting my friend Marlowe if you are an aspiring author. Authors.ai is a relatively new web property directly related to enhancing your novel's success or manuscript using Artificial Intelligence. Practically, Marlowe (the intelligent AI engine) reads and writes manuscripts in under an hour. Marlowe is labeled as a self-editing tool but's it is much more nuanced. more
We all have a creative side, so consider meeting my friend Marlowe if you are an aspiring author. Authors.ai is a relatively new web property directly related to enhancing your novel's success or manuscript using Artificial Intelligence. Practically, Marlowe (the intelligent AI engine) reads and writes manuscripts in under an hour. Marlowe is labeled as a self-editing tool but's it is much more nuanced. more
 One of the most common questions I've been asked lately is what I think the impact AI will have on the broadband industry. All of the big ISPs in the industry have actively been pursuing the use of AI. For example, AT&T Labs says it is investigating the use of AI to optimize the customer experience and auto-heal the network. Comcast says that it is using AI to help process petabytes of data every day. more
One of the most common questions I've been asked lately is what I think the impact AI will have on the broadband industry. All of the big ISPs in the industry have actively been pursuing the use of AI. For example, AT&T Labs says it is investigating the use of AI to optimize the customer experience and auto-heal the network. Comcast says that it is using AI to help process petabytes of data every day. more
 This is Part 4 of a series of articles published (here in CircleID) on the UDHR and human rights in the cyberspaces of the Internet Ecosystem. Here we discuss Articles 13-15 and touch on other topics such as the role of cyber governance, empowered digital citizenship, and whistleblowers. At this point in this series of articles on the UDHR in the digital age, it is useful to pause and remind ourselves of the purpose of this analysis. more
This is Part 4 of a series of articles published (here in CircleID) on the UDHR and human rights in the cyberspaces of the Internet Ecosystem. Here we discuss Articles 13-15 and touch on other topics such as the role of cyber governance, empowered digital citizenship, and whistleblowers. At this point in this series of articles on the UDHR in the digital age, it is useful to pause and remind ourselves of the purpose of this analysis. more
 As counterfeit networks grow more elusive, AI-driven clustering could revolutionize brand protection. By linking disparate findings, identifying serial infringers, and enabling bulk enforcement, AI offers a smarter approach to monitoring and takedown efforts. Yet, challenges remain - from data reliability to analyzing complex content. Companies that master AI-driven clustering may gain a significant advantage in the fight against brand abuse. more
As counterfeit networks grow more elusive, AI-driven clustering could revolutionize brand protection. By linking disparate findings, identifying serial infringers, and enabling bulk enforcement, AI offers a smarter approach to monitoring and takedown efforts. Yet, challenges remain - from data reliability to analyzing complex content. Companies that master AI-driven clustering may gain a significant advantage in the fight against brand abuse. more
DeepMind AI reduces energy used for cooling Google data centers by 40%, was announced today in a blog post by Google's Rich Evans, Research Engineer, DeepMind and Jim Gao, Data Center Engineer. more
Google's Threat Intelligence Group reveals that hackers are integrating AI models directly into malware, enabling live code mutation, stealthier operations, and dynamic payload execution while exploiting AI tools through deceptive prompts and underground marketplaces. more
 Popular media have recently reported a White House initiative asserting companies' "moral obligation" to limit the risks of AI products. True enough, but the issues are far broader. At the core of the debate around AI -- will it save us or destroy us? -- are questions of values. Can we tell AI how to behave safely for humans, even if in the future it has a "mind of its own"? It is often said that AI algorithms should be "aligned with human values." more
Popular media have recently reported a White House initiative asserting companies' "moral obligation" to limit the risks of AI products. True enough, but the issues are far broader. At the core of the debate around AI -- will it save us or destroy us? -- are questions of values. Can we tell AI how to behave safely for humans, even if in the future it has a "mind of its own"? It is often said that AI algorithms should be "aligned with human values." more
 What will the Internet look like in the next seven to 10 years? How will things like marketplace consolidation, changes to regulation, increases in cybercrime or the widespread deployment of the Internet of Things impact the Internet, its users and society? At the Internet Society, we are always thinking about what's next for the Internet. And now we want your help! more
What will the Internet look like in the next seven to 10 years? How will things like marketplace consolidation, changes to regulation, increases in cybercrime or the widespread deployment of the Internet of Things impact the Internet, its users and society? At the Internet Society, we are always thinking about what's next for the Internet. And now we want your help! more
 One of the central goals of a brand protection program is detecting infringing third-party activity that falls outside the firewall - that is, external to a brand owner's portfolio of official core and tactical domains. Brand threats occur across a range of internet channels, but domain name abuse is one of the most significant areas for concern, both in terms of the visibility and potential for confusion of branded domain names by potential customers, and the enforcement options available. For this reason, domain monitoring is considered a core component of a brand protection service. more
One of the central goals of a brand protection program is detecting infringing third-party activity that falls outside the firewall - that is, external to a brand owner's portfolio of official core and tactical domains. Brand threats occur across a range of internet channels, but domain name abuse is one of the most significant areas for concern, both in terms of the visibility and potential for confusion of branded domain names by potential customers, and the enforcement options available. For this reason, domain monitoring is considered a core component of a brand protection service. more
 This study analyzes the differences in domain name and IP address strategies among a number of current mainstream artificial intelligence (AI) service providers. We find that these technical choices not only reflect deployment decisions but also deep-seated corporate knowledge and capabilities in Internet infrastructure service provision, as well as brand positioning and market strategies. more
This study analyzes the differences in domain name and IP address strategies among a number of current mainstream artificial intelligence (AI) service providers. We find that these technical choices not only reflect deployment decisions but also deep-seated corporate knowledge and capabilities in Internet infrastructure service provision, as well as brand positioning and market strategies. more
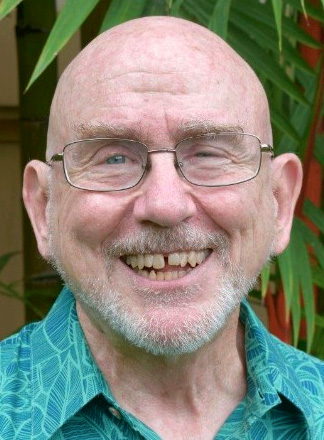
 My involvement in the ICT industry over the last 40 years has always been to look at the strategic advantages that new technologies have to offer. I entered the industry through a proto-internet development called videotext. I looked at this technology, at what organisations could do with it, and assisted, for example, in the 1980s when the Commonwealth Bank introduced the world's first national online banking service called Telebank. more
My involvement in the ICT industry over the last 40 years has always been to look at the strategic advantages that new technologies have to offer. I entered the industry through a proto-internet development called videotext. I looked at this technology, at what organisations could do with it, and assisted, for example, in the 1980s when the Commonwealth Bank introduced the world's first national online banking service called Telebank. more