


|
||
|
||
On 12 June, the DFIR Report published an in-depth analysis of a Truebot intrusion that began with several page redirects via a Traffic Distribution System (TDS) and ended with dropping a Master Boot Record (MBR) killer wiper onto a victim’s computer. The result? The users’ data got exfiltrated to a threat actor-owned remote server and erased from the source. Worse, while some victims were prompted to reboot, more unfortunate ones were left with inoperable systems.
To collate as much DNS intel as possible, we pivoted off the researchers’ list of IoCs comprising three domains and five IP addresses for an expansion analysis. Our DNS deep dive uncovered the following:
A sample of the additional artifacts obtained from our analysis is available for download from our website.
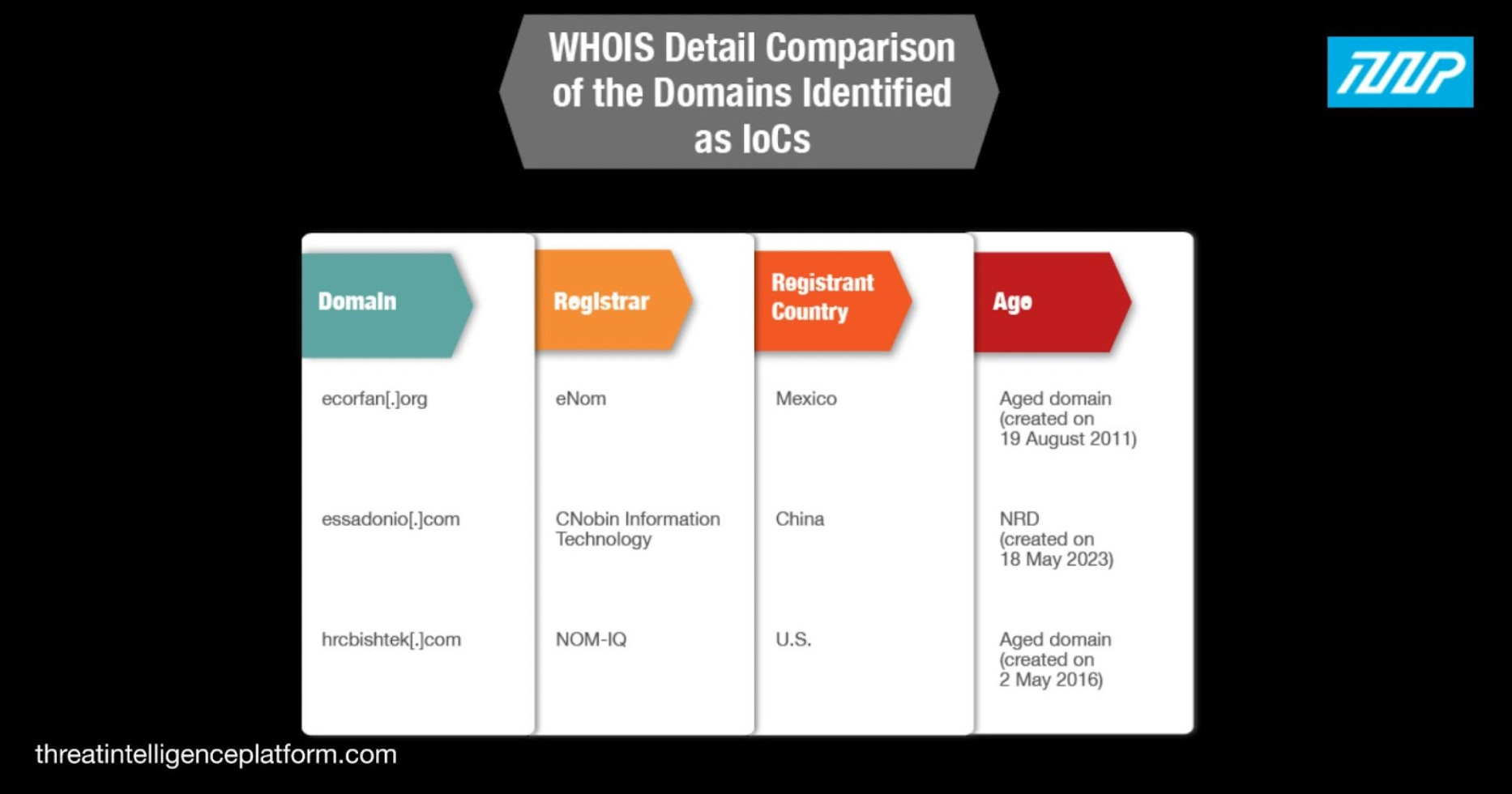
Based on the current WHOIS records of the three domains identified as IoCs, we found that:
Take a look at the comparison table below.
Further scrutiny of the domains’ historical WHOIS records allowed us to uncover an unredacted registrant email address for hrcbishtek[.]com. A historical reverse WHOIS lookup for the registrant email address uncovered 7,666 other domains, four of which have been categorized as malicious based on a Threat Intelligence Platform (TIP) bulk malware check.
While two of the malicious email-connected domains contained the string hardrock, one of them (hardrockjinan[.]com) couldn’t be definitively attributed to the entertainment chain based on a WHOIS record detail comparison.
DNS lookups for the four IoCs revealed that they resolved to three unique IP addresses, one of which (45[.]182[.]189[.]71) has already been identified as an IoC.
The DFIR Report identified five IP addresses as IoCs. Adding the two hosts we found—193[.]3[.]19[.]173 and 209[.]59[.]139[.]215—gave us a total of seven that we then subjected to further scrutiny. We found that:
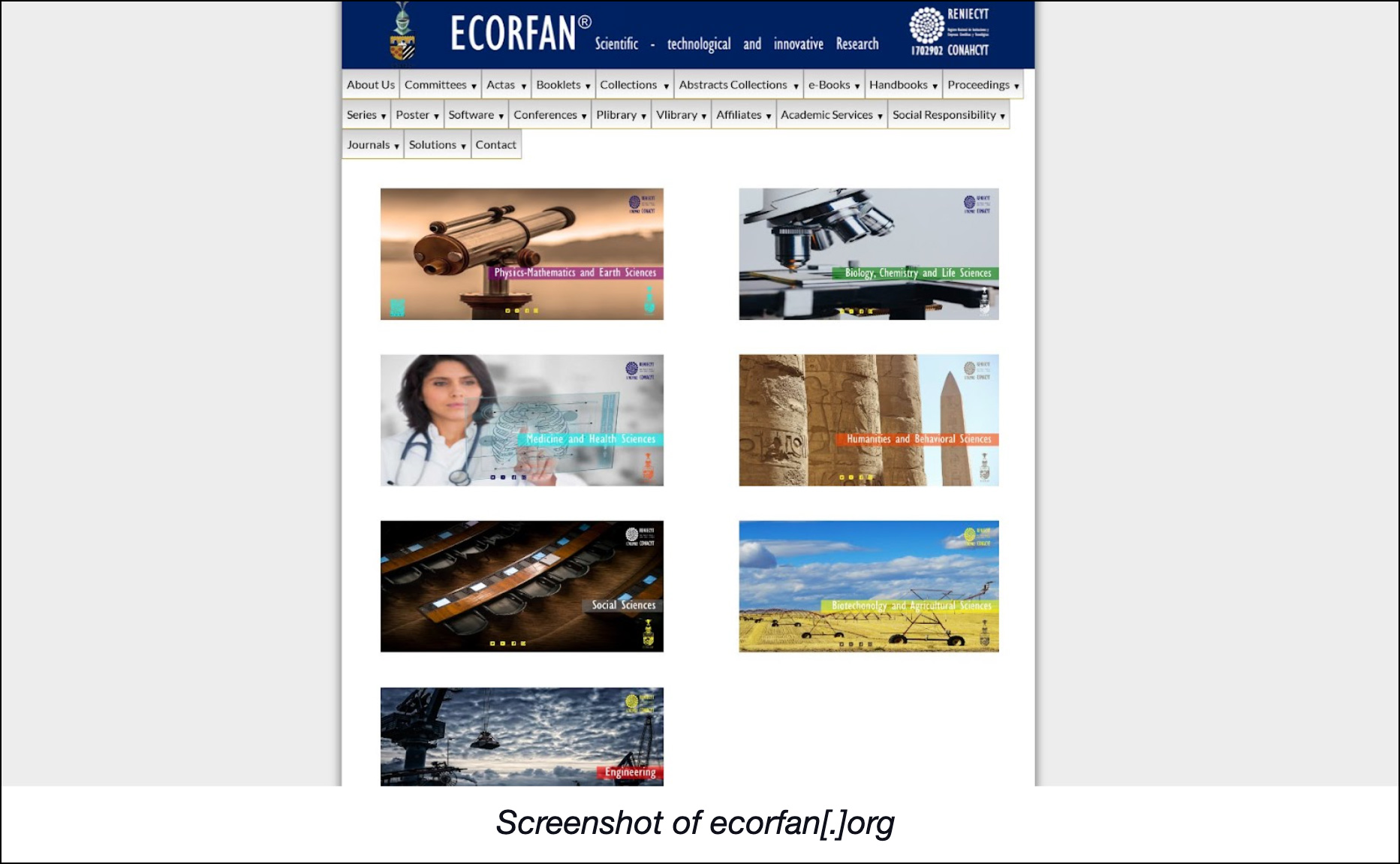
It’s also interesting to note that a string in one of the domains classified as an IoC—ecorfan—appeared in one other domain—ecorfan[.]com.
Both domains were created around the same time—ecorfan[.]org (identified as an IoC) on 14 June 2023 and ecorfan[.]com on 15 June 2023. But while ecorfan[.]com’s WHOIS record details weren’t publicly available, ecorfan[.]org’s was. Based on its current WHOIS record, the latter could belong to the Mexican government. A malware check, however, showed that it’s currently considered malicious. If it is a federal website, it could have been compromised to serve Truebot. The following screenshot also reveals that it continues to host live content.
The string hardrock, meanwhile, was present in several email-connected domains. As such, we scoured the DNS for domains containing the said string, which led to the discovery of more than 10,000 such web properties. While several of them could belong to the multinational company Hard Rock Cafe, Inc., some could be cybersquatting on the organization’s popularity. They didn’t indicate their registrant organizations and had different registrars compared to hardrock[.]com.
A TIP bulk malware check for the domains we found also showed that three were currently classified as malware hosts and one continues to host live content. Take a look at its screenshot below.
Note, too, that one of the malicious domains could belong to Hard Rock since it shared the registrant organization name (Hard Rock Cafe International U.S.A., Inc.) reflected in the current WHOIS record of the global corporation’s official website hardrock[.]com. Threat actors could have compromised the said site or mimicked the registrant organization name. The remaining two malicious hardrock-containing domains were likely owned by cybersquatters hoping to lure the company’s customers to their specially crafted malware-laden pages.
DNS deep dives via an IoC expansion analysis aided by comprehensive threat intelligence solutions like TIP can help organizations identify possible attack vectors as soon as they get registered, even before threat actors can weaponize them. Our in-depth investigation on Truebot allowed us to identify thousands of potentially connected artifacts that possibly mimicked companies like Hard Rock and may warrant their security teams’ attention.
If you wish to perform a similar investigation or learn more about the products used in this research, please don’t hesitate to contact us.
Disclaimer: We take a cautionary stance toward threat detection and aim to provide relevant information to help protect against potential dangers. Consequently, it is possible that some entities identified as “threats” or “malicious” may eventually be deemed harmless upon further investigation or changes in context. We strongly recommend conducting supplementary investigations to corroborate the information provided herein.
Sponsored byDNIB.com

Sponsored byRadix

Sponsored byWhoisXML API

Sponsored byVerisign

Sponsored byVerisign

Sponsored byCSC

Sponsored byIPv4.Global
