

 As if we didn't have a long enough list of problems to worry about, Lumen researchers at its Black Lotus Labs recently released a blog that said that it knows of three U.S. ISPs and one in India was hacked this summer. Lumen said the hackers took advantage of flaws in software provided by Versa Networks being used to manage wide-area networks.
As if we didn't have a long enough list of problems to worry about, Lumen researchers at its Black Lotus Labs recently released a blog that said that it knows of three U.S. ISPs and one in India was hacked this summer. Lumen said the hackers took advantage of flaws in software provided by Versa Networks being used to manage wide-area networks.
 On 29 March 2024, an announcement was posted notifying the world that the Open-Source Software (OSS) package "xz-utils," which includes the xz data compression program and a library of software routines called "liblzma" and which is present in most Linux distributions, had been compromised. The insertion of the compromised code was done by "Jia Tan", the official maintainer of the xz-utils package.
On 29 March 2024, an announcement was posted notifying the world that the Open-Source Software (OSS) package "xz-utils," which includes the xz data compression program and a library of software routines called "liblzma" and which is present in most Linux distributions, had been compromised. The insertion of the compromised code was done by "Jia Tan", the official maintainer of the xz-utils package.
 Satellites make it possible for governments to provide essential services, such as national defense, navigation, and weather forecasting. Private ventures use satellites to offer highly desired services that include video program distribution, telecommunications, and Internet access. The Russian launch of a satellite, with nuclear power and the likely ability to disable satellites, underscores how satellites are quite vulnerable to both natural and manmade ruin.
Satellites make it possible for governments to provide essential services, such as national defense, navigation, and weather forecasting. Private ventures use satellites to offer highly desired services that include video program distribution, telecommunications, and Internet access. The Russian launch of a satellite, with nuclear power and the likely ability to disable satellites, underscores how satellites are quite vulnerable to both natural and manmade ruin.
 Last month, the Russian state-sponsored hacking group "Midnight Blizzard" gained access to the email accounts of Microsoft leadership, even exfiltrating documents and messages. The group reportedly used a simple brute-force style attack to access a forgotten test account and then exploited the permissions on that account to access the emails of employees in the cybersecurity and legal teams.
Last month, the Russian state-sponsored hacking group "Midnight Blizzard" gained access to the email accounts of Microsoft leadership, even exfiltrating documents and messages. The group reportedly used a simple brute-force style attack to access a forgotten test account and then exploited the permissions on that account to access the emails of employees in the cybersecurity and legal teams.
 From the creation of DNSAI Compass ("Compass"), we knew that measuring DNS Abuse1 would be difficult and that it would be beneficial to anticipate the challenges we would encounter. With more than a year of published reports, we are sharing insights into one of the obstacles we have faced. One of our core principles is transparency and we've worked hard to provide this with our methodology.
From the creation of DNSAI Compass ("Compass"), we knew that measuring DNS Abuse1 would be difficult and that it would be beneficial to anticipate the challenges we would encounter. With more than a year of published reports, we are sharing insights into one of the obstacles we have faced. One of our core principles is transparency and we've worked hard to provide this with our methodology.
 The Uptime Institute (UI) is an IT industry research firm best known for certifying that data centers meet industry standards. UI issues an annual report that analyzes the cause of data center outages. The causes for data center outages are relevant to the broadband industry because the same kinds of issues shut down switching hubs and Network Operations Centers.
The Uptime Institute (UI) is an IT industry research firm best known for certifying that data centers meet industry standards. UI issues an annual report that analyzes the cause of data center outages. The causes for data center outages are relevant to the broadband industry because the same kinds of issues shut down switching hubs and Network Operations Centers.
 Unsuspecting website visitors are often unaware when they have landed on a spoofed page or are re-directed to malware-hosting web servers designed to steal their sensitive data and information. This attack is known as subdomain hijacking, or subdomain takeover. A web user's private information is then traded on the dark web, and cybercriminals profit, further fueling the expansion of identity theft in the online world.
Unsuspecting website visitors are often unaware when they have landed on a spoofed page or are re-directed to malware-hosting web servers designed to steal their sensitive data and information. This attack is known as subdomain hijacking, or subdomain takeover. A web user's private information is then traded on the dark web, and cybercriminals profit, further fueling the expansion of identity theft in the online world.
 In today's digital age, securing your website and ensuring your users' safety has never been more critical. Secure sockets layer (SSL) certificates are the go-to solution for securing websites by encrypting the data transmitted between web servers and browsers. Historically, SSL digital certificates could be valid for years, after which they had to be renewed or replaced.
In today's digital age, securing your website and ensuring your users' safety has never been more critical. Secure sockets layer (SSL) certificates are the go-to solution for securing websites by encrypting the data transmitted between web servers and browsers. Historically, SSL digital certificates could be valid for years, after which they had to be renewed or replaced.
 OARC held a 2-day meeting in February, with presentations on various DNS topics. Here are some observations I picked up from the presentations in that meeting... In a world where every DNS name is DNSSEC-signed, and every DNS client validates all received DNS responses, we wouldn't necessarily have the problem of DNS spoofing. Even if we concede that universal use of DNSSEC is a long time off ...
OARC held a 2-day meeting in February, with presentations on various DNS topics. Here are some observations I picked up from the presentations in that meeting... In a world where every DNS name is DNSSEC-signed, and every DNS client validates all received DNS responses, we wouldn't necessarily have the problem of DNS spoofing. Even if we concede that universal use of DNSSEC is a long time off ...
 Brand impersonation happens much more often than people realize. In CSC's latest Domain Security Report, we found that 75% of domains for the Global 2000 that contained more than six characters from the brand names were not actually owned by the brands themselves. The intent of these fake domain registrations is to leverage the trust placed on the targeted brands to launch phishing attacks, other forms of digital brand abuse, or IP infringement...
Brand impersonation happens much more often than people realize. In CSC's latest Domain Security Report, we found that 75% of domains for the Global 2000 that contained more than six characters from the brand names were not actually owned by the brands themselves. The intent of these fake domain registrations is to leverage the trust placed on the targeted brands to launch phishing attacks, other forms of digital brand abuse, or IP infringement...
 The DNS Abuse Institute recently published our sixth monthly report for our project to measure DNS Abuse: DNSAI Compass ('Compass'). Compass is an initiative of the DNS Abuse Institute to measure the use of the DNS for phishing and malware. The intention is to establish a credible source of metrics for addressing DNS Abuse. We hope this will enable focused conversations, and identify opportunities for improvement.
The DNS Abuse Institute recently published our sixth monthly report for our project to measure DNS Abuse: DNSAI Compass ('Compass'). Compass is an initiative of the DNS Abuse Institute to measure the use of the DNS for phishing and malware. The intention is to establish a credible source of metrics for addressing DNS Abuse. We hope this will enable focused conversations, and identify opportunities for improvement.
 New York Post has been "hacked" by an employee. To protect themselves from insider threats, companies can deploy zero trust and restrict access. On October 27, the New York Post published a string of racist and sexist articles on its website. Fabricated news about politicians, such as pieces concerning racist comments of a New York City mayor, has been headlining the publication.
New York Post has been "hacked" by an employee. To protect themselves from insider threats, companies can deploy zero trust and restrict access. On October 27, the New York Post published a string of racist and sexist articles on its website. Fabricated news about politicians, such as pieces concerning racist comments of a New York City mayor, has been headlining the publication.
 More and more information is becoming available about the breach of Optus (Australia's second-largest telco). It looks like the hacker is more of an amateur than a professional criminal or a "state actor." This makes the hack even more worrisome. It looks as though Optus didn't have its security house in order. This makes the issue all the more painful for the company. It will dent its reputation, and customers could become somewhat wary about dealing with the company.
More and more information is becoming available about the breach of Optus (Australia's second-largest telco). It looks like the hacker is more of an amateur than a professional criminal or a "state actor." This makes the hack even more worrisome. It looks as though Optus didn't have its security house in order. This makes the issue all the more painful for the company. It will dent its reputation, and customers could become somewhat wary about dealing with the company.
 As a long-established online attack strategy, phishing remains a popular tool for fraudsters because of its effectiveness. The Anti-Phishing Working Group reported more than 300,000 distinct phishing attacks in December 2021 -- more than three times the number reported in early 2020, and the highest monthly total ever identified.
As a long-established online attack strategy, phishing remains a popular tool for fraudsters because of its effectiveness. The Anti-Phishing Working Group reported more than 300,000 distinct phishing attacks in December 2021 -- more than three times the number reported in early 2020, and the highest monthly total ever identified.
 We've all heard the term, "you're only as strong as your weakest link." Whether talking about a tug of war on the playground, a sports team, or a business, this rings as true as ever. Every business relies on a series of suppliers and vendors -- be it the dairy farm supplying milk to the multinational food manufacturer or the payment systems that retailers use. These links form supply chains that every business, large and small, deals with. There is simply no way around it.
We've all heard the term, "you're only as strong as your weakest link." Whether talking about a tug of war on the playground, a sports team, or a business, this rings as true as ever. Every business relies on a series of suppliers and vendors -- be it the dairy farm supplying milk to the multinational food manufacturer or the payment systems that retailers use. These links form supply chains that every business, large and small, deals with. There is simply no way around it.
 Chinese Hackers Had Access to Canadian Government Systems for Years, Report Reveals
Chinese Hackers Had Access to Canadian Government Systems for Years, Report Reveals Sudanese Nationals Charged in Global Cyberattack Campaign
Sudanese Nationals Charged in Global Cyberattack Campaign Over 2 Million VPN Passwords Compromised by Malware Attacks
Over 2 Million VPN Passwords Compromised by Malware Attacks FBI Takes Down China-Backed Botnet, Facilitates Ransomware Negotiations
FBI Takes Down China-Backed Botnet, Facilitates Ransomware Negotiations Mystery Malware Takes Down 600,000 Windstream Routers in Coordinated Attack
Mystery Malware Takes Down 600,000 Windstream Routers in Coordinated Attack Biden Administration Alerts Governors to Rising Cyber Threats on U.S. Water Systems
Biden Administration Alerts Governors to Rising Cyber Threats on U.S. Water Systems Ransomware Crisis in U.S. Healthcare
Ransomware Crisis in U.S. Healthcare Global Law Enforcement Strikes Major Blow Against LockBit Ransomware Operation
Global Law Enforcement Strikes Major Blow Against LockBit Ransomware Operation Millions of Smart Toothbrushes Hijacked in Cyberattack on Swiss Firm
Millions of Smart Toothbrushes Hijacked in Cyberattack on Swiss Firm Ukraine’s Leading Mobile Operator Struck by War’s Largest Cyberattack
Ukraine’s Leading Mobile Operator Struck by War’s Largest Cyberattack Denmark Encounters Largest Cyber Attack on Its Critical Infrastructure to Date
Denmark Encounters Largest Cyber Attack on Its Critical Infrastructure to Date Activist Hackers Target Government Websites Amid Escalating Israel-Hamas War
Activist Hackers Target Government Websites Amid Escalating Israel-Hamas War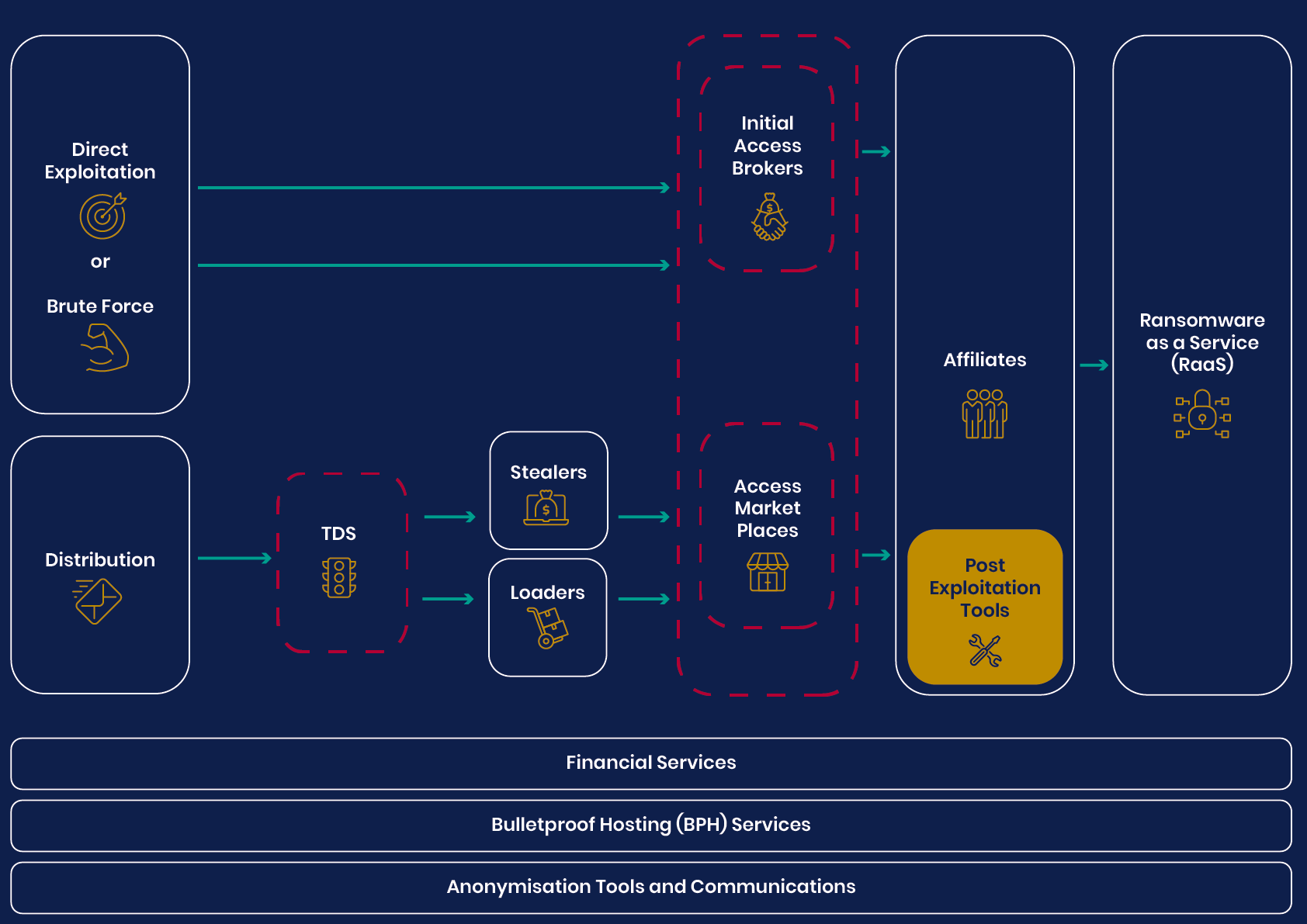 UK’s National Agencies Release White Paper on Evolving Cyber Crime Ecosystem
UK’s National Agencies Release White Paper on Evolving Cyber Crime Ecosystem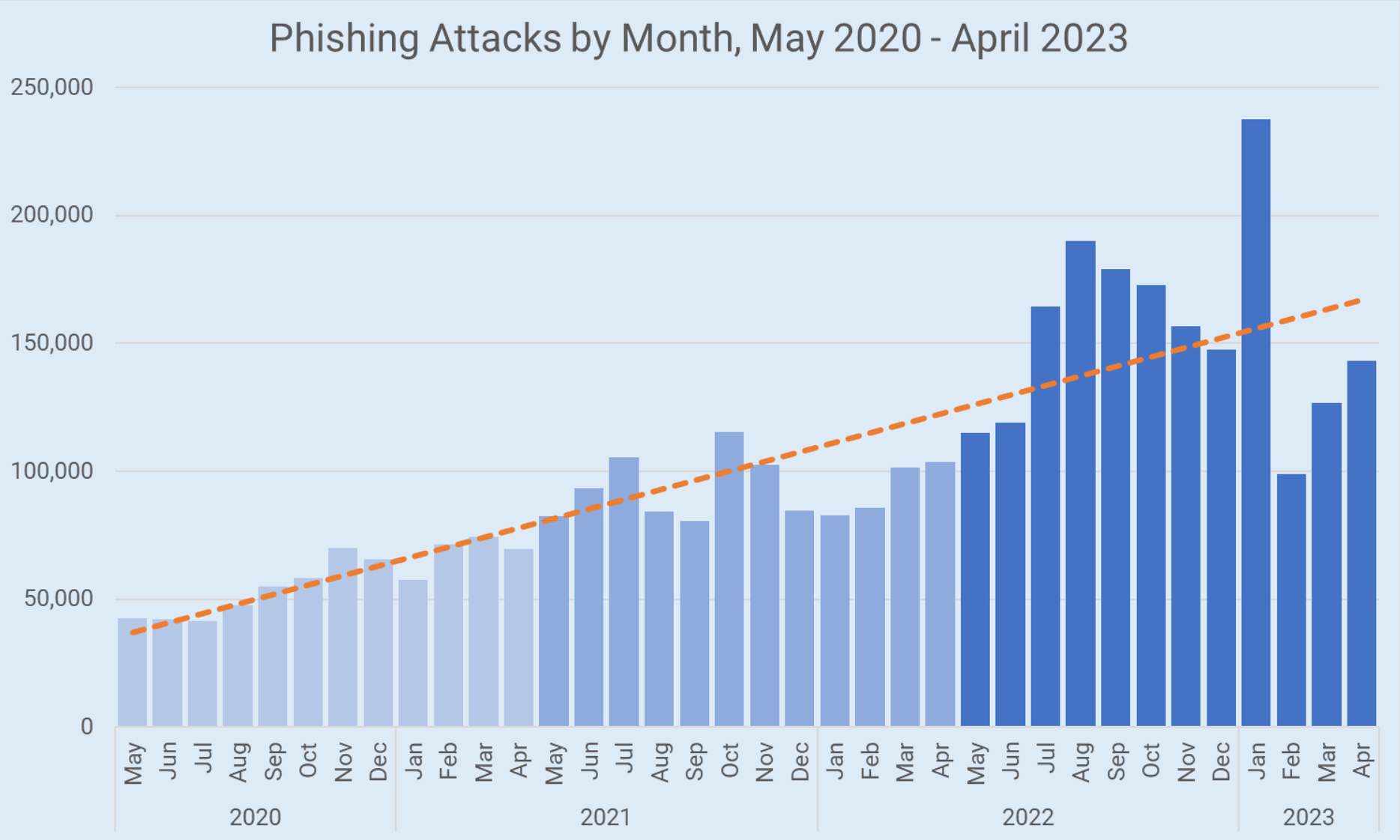 Phishing Attacks Surge Despite Increased Awareness, New Strategies Needed
Phishing Attacks Surge Despite Increased Awareness, New Strategies Needed British Researchers Discover AI-Powered Technique That Can Extract Data Through Typing Sounds
British Researchers Discover AI-Powered Technique That Can Extract Data Through Typing Sounds Widespread Cyberattack Paralyzes US Hospital Systems, Interrupting Critical Healthcare Services
Widespread Cyberattack Paralyzes US Hospital Systems, Interrupting Critical Healthcare Services