

 As ICANN confronts a harsher geopolitical era, its long-delayed review of the UDRP has become a defining test of whether the multistakeholder model can still deliver legitimate, effective Internet governance and sustain confidence in its future.
As ICANN confronts a harsher geopolitical era, its long-delayed review of the UDRP has become a defining test of whether the multistakeholder model can still deliver legitimate, effective Internet governance and sustain confidence in its future.
 Canada's online pharmacy industry is urging a ban on unregulated peptide sales, warning that products marketed for weight loss, bodybuilding and other uses pose serious health risks, evade regulatory oversight, and are increasingly sold online without prescriptions.
Canada's online pharmacy industry is urging a ban on unregulated peptide sales, warning that products marketed for weight loss, bodybuilding and other uses pose serious health risks, evade regulatory oversight, and are increasingly sold online without prescriptions.
 Domains and DNS underpin modern business operations, yet security gaps remain widespread. CSC's latest research shows why stronger domain protections are essential to resilience, helping companies reduce disruption, safeguard trust, and maintain continuity when attacks strike.
Domains and DNS underpin modern business operations, yet security gaps remain widespread. CSC's latest research shows why stronger domain protections are essential to resilience, helping companies reduce disruption, safeguard trust, and maintain continuity when attacks strike.
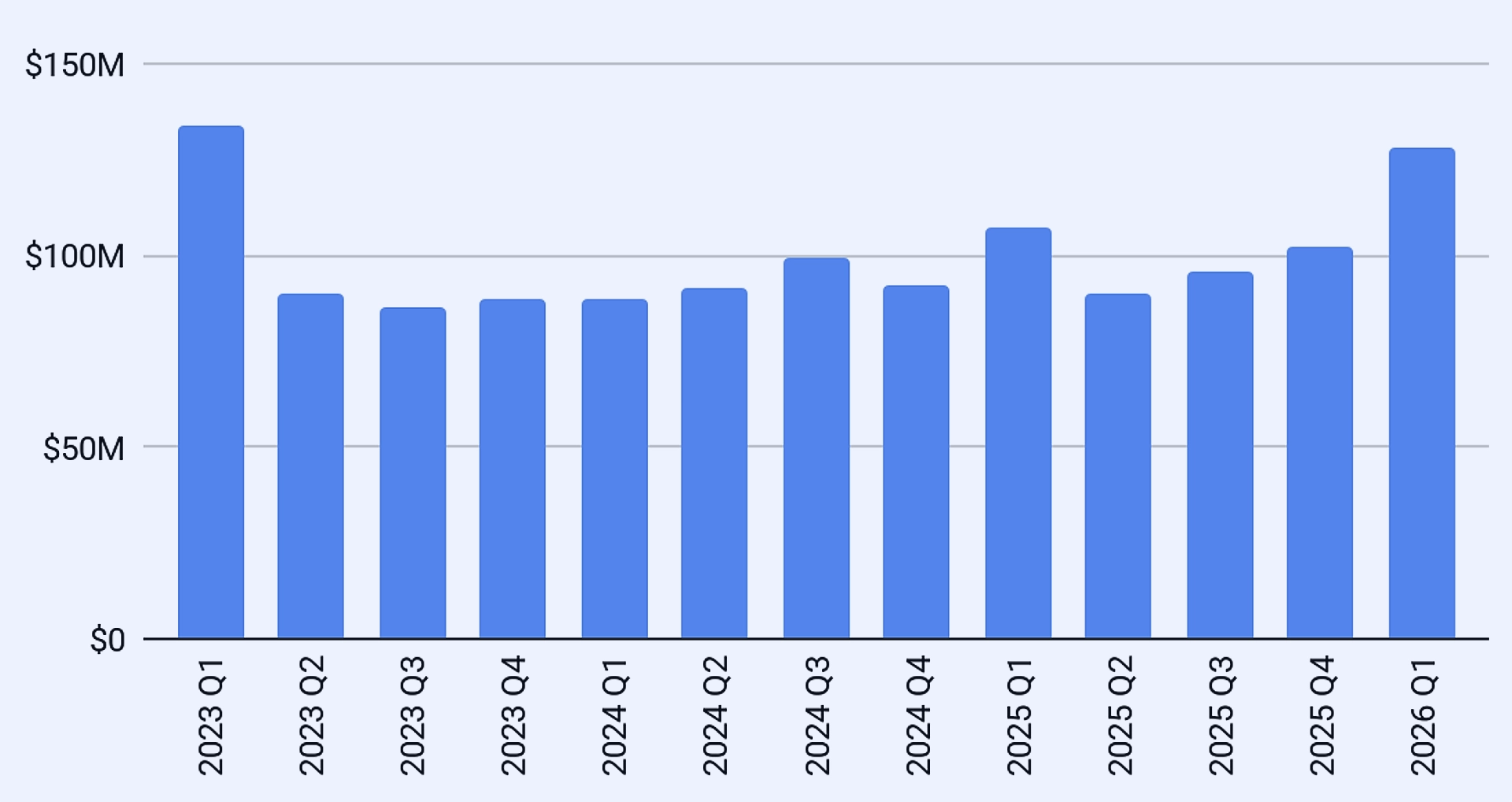
 After two years of falling prices, the IPv4 market has turned decisively. Surging transfer volumes, AI infrastructure demand and looming broadband expansion are tightening supply, pushing prices higher and leaving patient buyers facing a costlier reality.
After two years of falling prices, the IPv4 market has turned decisively. Surging transfer volumes, AI infrastructure demand and looming broadband expansion are tightening supply, pushing prices higher and leaving patient buyers facing a costlier reality.
 As the UN turns to AI governance, old lessons from internet governance loom large: multistakeholder rules matter, but sharper risks, geopolitical rivalry and machine autonomy make consensus harder and more urgent than before for all.
As the UN turns to AI governance, old lessons from internet governance loom large: multistakeholder rules matter, but sharper risks, geopolitical rivalry and machine autonomy make consensus harder and more urgent than before for all.
 Africa's data sovereignty debate focuses too heavily on where information is stored. Real sovereignty depends on control of cloud platforms, encryption, identity systems, and critical digital infrastructure that determine resilience, autonomy, and strategic power.
Africa's data sovereignty debate focuses too heavily on where information is stored. Real sovereignty depends on control of cloud platforms, encryption, identity systems, and critical digital infrastructure that determine resilience, autonomy, and strategic power.
 New data on DNS abuse reveals most malicious domains remain active beyond 24 hours, while a handful of registrars host the bulk of infrastructure, leaving India's population of first-generation internet users uniquely exposed to fraud.
New data on DNS abuse reveals most malicious domains remain active beyond 24 hours, while a handful of registrars host the bulk of infrastructure, leaving India's population of first-generation internet users uniquely exposed to fraud.
 As AI agents automate phishing, impersonation and domain abuse at machine scale, the Brand Registry Group argues that dotBrand domains are evolving from marketing assets into trust infrastructure underpinning cybersecurity, identity and interactions across the internet.
As AI agents automate phishing, impersonation and domain abuse at machine scale, the Brand Registry Group argues that dotBrand domains are evolving from marketing assets into trust infrastructure underpinning cybersecurity, identity and interactions across the internet.
 As power grids depend on microsecond precision, states must treat time synchronization as sovereign infrastructure, hardening satellite, fiber and orbital defenses against hybrid attacks that could trigger catastrophic blackouts through resilient sovereign time defense frameworks.
As power grids depend on microsecond precision, states must treat time synchronization as sovereign infrastructure, hardening satellite, fiber and orbital defenses against hybrid attacks that could trigger catastrophic blackouts through resilient sovereign time defense frameworks.
 ICANN's court intervention in AFRINIC's winding-up case widens a local corporate dispute into a global Internet governance test, exposing weaknesses in RIR protections and strengthening calls for ICP-2 reforms to safeguard registry continuity.
ICANN's court intervention in AFRINIC's winding-up case widens a local corporate dispute into a global Internet governance test, exposing weaknesses in RIR protections and strengthening calls for ICP-2 reforms to safeguard registry continuity.
 Africa is rapidly emerging as a critical testing ground for AI governance, where fast adoption, evolving digital ecosystems, and uneven institutional readiness are exposing regulatory gaps with global implications.
Africa is rapidly emerging as a critical testing ground for AI governance, where fast adoption, evolving digital ecosystems, and uneven institutional readiness are exposing regulatory gaps with global implications.
 ICANN's AFRINIC episode shows how support can harden into perceived authority. A standing RIR Boundary Protocol would force early warnings, role disclosure and procedural safeguards before regional engagement drifts into governance redesign.
ICANN's AFRINIC episode shows how support can harden into perceived authority. A standing RIR Boundary Protocol would force early warnings, role disclosure and procedural safeguards before regional engagement drifts into governance redesign.
 As AI reshapes the digital world, online safety depends on balancing smarter protection with growing risks. From cybersecurity to privacy concerns, understanding AI's role can help users stay secure, informed, and resilient online.
As AI reshapes the digital world, online safety depends on balancing smarter protection with growing risks. From cybersecurity to privacy concerns, understanding AI's role can help users stay secure, informed, and resilient online.
 The internet is fragmenting across cables, routing systems and governance. Most network engineers, focused on regional operations, are missing how technical infrastructure and state power are reshaping a once interoperable network.
The internet is fragmenting across cables, routing systems and governance. Most network engineers, focused on regional operations, are missing how technical infrastructure and state power are reshaping a once interoperable network.
 Fake news spreads quickly online, fueling distrust, manipulation, and conflict. As AI-generated content grows more sophisticated, media literacy, fact-checking, and vigilance are essential to protecting online safety and preserving trust in information.
Fake news spreads quickly online, fueling distrust, manipulation, and conflict. As AI-generated content grows more sophisticated, media literacy, fact-checking, and vigilance are essential to protecting online safety and preserving trust in information.
 An official-looking renewal notice reveals how open namespaces shift verification burdens onto users. Restricted government domains like .gov.au function as trust infrastructure, embedding authority into the namespace and reducing fraud, confusion, and verification costs.
An official-looking renewal notice reveals how open namespaces shift verification burdens onto users. Restricted government domains like .gov.au function as trust infrastructure, embedding authority into the namespace and reducing fraud, confusion, and verification costs.
 Mounting signs of consumer distress, from unpaid utility bills to rising loan delinquencies, are raising uncomfortable questions for internet providers about whether broadband remains recession-proof as households increasingly trade home connections for cheaper wireless alternatives.
Mounting signs of consumer distress, from unpaid utility bills to rising loan delinquencies, are raising uncomfortable questions for internet providers about whether broadband remains recession-proof as households increasingly trade home connections for cheaper wireless alternatives.
 ICANN's Smart Africa engagement shows how proposals can gain authority without formal endorsement, raising harder questions about CAIGA, ICP-2 and whether regional partnerships need earlier safeguards when RIR governance begins to shift under institutional cover.
ICANN's Smart Africa engagement shows how proposals can gain authority without formal endorsement, raising harder questions about CAIGA, ICP-2 and whether regional partnerships need earlier safeguards when RIR governance begins to shift under institutional cover.
 As cross-border cyber enforcement falters, critics argue Article 19's DNS abuse framework prioritizes procedural purity over user protection, leaving courts too slow to counter AI-driven phishing, rapid-flux domains, and increasingly automated online threats.
As cross-border cyber enforcement falters, critics argue Article 19's DNS abuse framework prioritizes procedural purity over user protection, leaving courts too slow to counter AI-driven phishing, rapid-flux domains, and increasingly automated online threats.
 As Africa digitises rapidly, control over data is emerging as a strategic contest. Foreign infrastructure dominance exposes economic and cybersecurity vulnerabilities, pushing governments to prioritise digital capability, regional cooperation, and stronger sovereignty over the systems powering the continent's future.
As Africa digitises rapidly, control over data is emerging as a strategic contest. Foreign infrastructure dominance exposes economic and cybersecurity vulnerabilities, pushing governments to prioritise digital capability, regional cooperation, and stronger sovereignty over the systems powering the continent's future.
Researchers have uncovered a browser-based technique that exploits SSD activity through local storage features, allowing malicious websites to infer user behavior, identify visited sites and applications, and potentially expand online tracking without special permissions. more
 Blank Domain Names Surpass Websites in Value for the First Time, Report Finds
Blank Domain Names Surpass Websites in Value for the First Time, Report Finds
The domain name market recorded its strongest quarter in three years as .com sales hit a record high and investors poured capital into undeveloped web assets, signaling growing demand for premium digital real estate and scarce online identities. more
The European Union plans to reserve most future satellite spectrum for regional firms while still allowing Starlink and Amazon to compete, reflecting Brussels' attempt to balance technological sovereignty with market openness in a strategically sensitive communications sector. more
 Iran Begins Restoring Internet After Record 88-Day Blackout
Iran Begins Restoring Internet After Record 88-Day Blackout
Iran has begun restoring internet access after an 88-day shutdown, but legal challenges and political divisions threaten the future of a reopening driven by economic strain and mounting pressure to reconnect the country. more
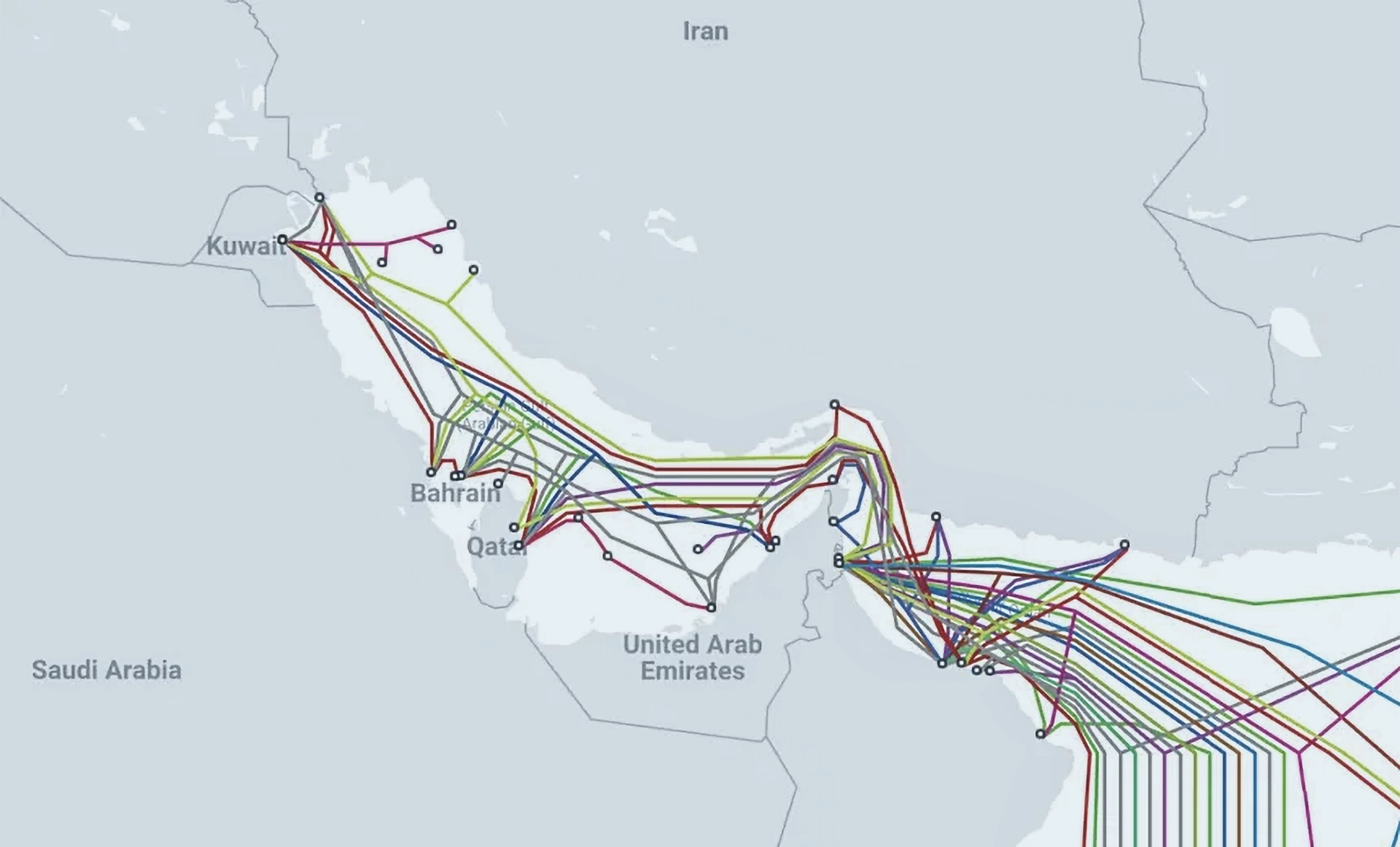 Iran Threatens Subsea Internet Cables in the Strait of Hormuz
Iran Threatens Subsea Internet Cables in the Strait of Hormuz
Iran is seeking to monetize and potentially weaponize subsea internet cables beneath the Strait of Hormuz, exposing how modern geopolitical conflicts increasingly threaten the digital infrastructure underpinning global finance, communications and trade. more
 Inside Iran’s Shift From Internet Shutdowns to Tiered Connectivity
Inside Iran’s Shift From Internet Shutdowns to Tiered Connectivity
Iran's wartime internet restrictions transformed online access into a costly, unequal system, according to researcher Imad Payande, with black markets, selective connectivity and institutional privilege reshaping how citizens reached the global web. more
Maria Xynou warns that internet censorship is becoming more sophisticated and less transparent as governments deploy targeted blocks, throttling and encrypted traffic interference, while OONI's crowdsourced measurements help researchers and human-rights groups expose restrictions and defend online freedoms worldwide. more
Google says cybercriminals and state-backed hackers are rapidly adopting generative AI to automate attacks, disguise malware, exploit vulnerabilities and spread disinformation, marking a shift from experimental use to industrial-scale cyber operations across the global threat landscape. more
Cybersecurity pioneer Steven Bellovin's new book strips away jargon and outdated online-safety advice, offering ordinary users practical guidance on passwords, phishing, privacy and digital habits in an era of constant cyber threats and increasingly sophisticated scams. more
ARTICLE 19 warns that governments are increasingly exploiting internet infrastructure to silence critics, using domain suspensions to block entire websites while regulators and registry operators debate how to balance online safety, technical abuse prevention and freedom of expression. more
A surge in massive cybersquatting disputes pushed UDRP domain-name cases sharply higher in early 2026, with two complaints alone accounting for more than a quarter of all disputed domains, according to a new report released by GigaLaw. more
 ICANN Opens New gTLD Applications for First Time Since 2012, With $227K Entry Fee and 27 Scripts
ICANN Opens New gTLD Applications for First Time Since 2012, With $227K Entry Fee and 27 Scripts
ICANN reopens applications for new top-level domains after 14 years, charging $227,000 per bid while tightening rules, as it seeks to expand multilingual access and reshape competition in the internet's naming system. more
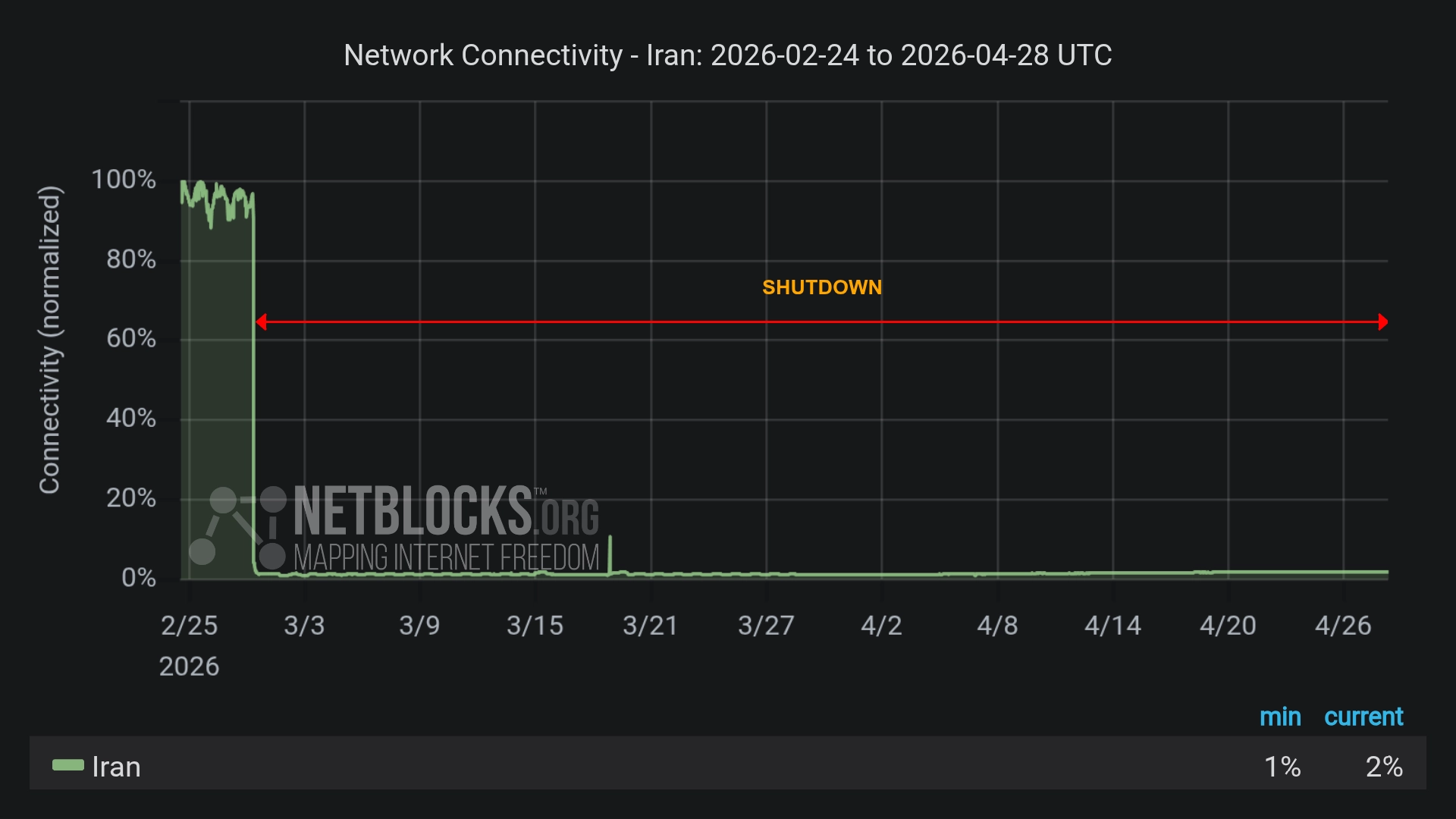 Iran’s Internet Blackout Hits 60 Days - Deepening Economic Crisis, Two-Tier Access
Iran’s Internet Blackout Hits 60 Days - Deepening Economic Crisis, Two-Tier Access
Iran's now 60-day internet blackout is inflicting heavy economic losses, disrupting exports and daily life, while a tiered access plan deepens inequality and signals a shift toward tighter state control of digital connectivity. more
Iran-linked hackers infiltrated US industrial control systems, disrupting energy and water infrastructure. The attacks highlight systemic vulnerabilities in internet-connected devices and signal an enduring cyber threat despite easing geopolitical tensions. more
Iran’s unprecedented internet blackout, imposed after February’s strikes, has reduced connectivity to near zero, tightened state control over information, and set a global precedent for wartime digital isolation with significant humanitarian consequences. more
 U.S. Blocks Foreign-Made Routers Over Cybersecurity Fears
U.S. Blocks Foreign-Made Routers Over Cybersecurity Fears
America has barred imports of new foreign-made routers, citing cybersecurity risks tied to espionage and infrastructure disruption, signalling a broader push to reduce reliance on Chinese technology in critical network systems. more
 Iran Targeted by Self-Propagating Malware in Supply-Chain Cyberattacks
Iran Targeted by Self-Propagating Malware in Supply-Chain Cyberattacks
Self-propagating malware hidden in open-source software is targeting Iranian systems, wiping data on infected machines while sparing others, signalling a shift towards precise, politically motivated cyber sabotage through widely trusted digital supply chains. more
ICANN is examining the widespread use of parked domains and zero-click redirection, seeking to understand how automated traffic routing and advertising practices affect transparency, consumer protection and trust in the global domain-name system. more
Security researchers have uncovered Kadnap malware infecting more than 14,000 routers worldwide, forming a resilient peer-to-peer botnet that exploits outdated edge devices and could enable covert communications, proxy traffic, and future cyber attacks. more
 Iranians Outsmart Internet Blackout to Broadcast Airstrikes
Iranians Outsmart Internet Blackout to Broadcast Airstrikes
After US and Israeli strikes, Iran imposed a near-total internet blackout, yet citizens used satellite links and decentralized tools to share footage, undermining state control and exposing a growing contest over information in wartime. more
 Iran Expands Digital Dragnet After Crushing Protests
Iran Expands Digital Dragnet After Crushing Protests
After quelling nationwide protests, Iran has intensified its use of digital surveillance, deploying phone tracking, facial recognition and online monitoring to identify, intimidate and detain dissenters through a vast state-controlled communications infrastructure. more
 David J. Farber, Early Architect of the Internet, Dies at 91
David J. Farber, Early Architect of the Internet, Dies at 91
David J. Farber, a pioneering computer scientist and mentor to key architects of the Internet Protocol, has died at 91, leaving a legacy that helped transform isolated machines into the global network underpinning modern communication. more
Despite the long-anticipated exhaustion of IPv4 addresses, the Internet continues to function through clever workarounds, market transfers, and cautious optimism, while IPv6 adoption remains slow and the future of global connectivity appears uncertain. more
Iran is finalizing a nationwide internet isolation system that would allow authorities to disconnect from the global web, as protests continue and external equipment sources, including Huawei, remain shrouded in secrecy. more
Iran's regime has all but nullified, for the most part, Elon Musk's Starlink satellite network using advanced jamming, legal threats, and raids, turning a promising tool for protestors into a cautionary tale of digital authoritarianism. more
Sponsored byWhoisXML API

Sponsored byDNIB.com

Sponsored byCSC

Sponsored byIPv4.Global

Sponsored byVerisign

Sponsored byVerisign

Sponsored byRadix

 A DNS-focused investigation into the Axios NPM supply chain attack uncovered typosquatting networks, victim-linked infrastructure, and hundreds of connected domains, revealing how malicious actors built and sustained a sprawling cyber campaign around compromised software dependencies. more
A DNS-focused investigation into the Axios NPM supply chain attack uncovered typosquatting networks, victim-linked infrastructure, and hundreds of connected domains, revealing how malicious actors built and sustained a sprawling cyber campaign around compromised software dependencies. more
 Hexastrike traced an AtlasCross RAT campaign linked to Silver Fox, uncovering spoofed domains, victim infrastructure, and malicious network artifacts that reveal how attackers exploited trusted software brands to widen compromise and persistence. more
Hexastrike traced an AtlasCross RAT campaign linked to Silver Fox, uncovering spoofed domains, victim infrastructure, and malicious network artifacts that reveal how attackers exploited trusted software brands to widen compromise and persistence. more
 Q1 2026 domain activity showed registrations concentrated in a handful of TLDs, with 6.7 million new domains flagged as malicious, offering fresh insight into global DNS patterns and cybersecurity risks as shifting registration trends reshape. more
Q1 2026 domain activity showed registrations concentrated in a handful of TLDs, with 6.7 million new domains flagged as malicious, offering fresh insight into global DNS patterns and cybersecurity risks as shifting registration trends reshape. more
 A retrospective analysis of 2025's top ransomware groups reveals how DNS traces, historical WHOIS records, and network IoCs exposed hidden infrastructure, affiliate activity, and thousands of potential victim connections linked to major cybercriminal operations. more
A retrospective analysis of 2025's top ransomware groups reveals how DNS traces, historical WHOIS records, and network IoCs exposed hidden infrastructure, affiliate activity, and thousands of potential victim connections linked to major cybercriminal operations. more
 After months of decline, the IPv4 market is showing signs of stabilization. April pricing held steady across block sizes as resilient demand, broader transaction activity, and improving buyer confidence pointed toward a more constructive market environment through 2026. more
After months of decline, the IPv4 market is showing signs of stabilization. April pricing held steady across block sizes as resilient demand, broader transaction activity, and improving buyer confidence pointed toward a more constructive market environment through 2026. more
 An analysis of 191 network indicators tied to eight Iran-affiliated APT groups uncovered malicious domains, active infrastructure, thousands of victim-linked IP interactions, and coordinated DNS activity, revealing the breadth and persistence of Tehran-linked cyber operations amid escalating regional tensions. more
An analysis of 191 network indicators tied to eight Iran-affiliated APT groups uncovered malicious domains, active infrastructure, thousands of victim-linked IP interactions, and coordinated DNS activity, revealing the breadth and persistence of Tehran-linked cyber operations amid escalating regional tensions. more
 Corporate domain strategies remain anchored in legacy extensions even as new domains proliferate, forcing firms to balance global reach, regional needs and rising fraud risks in an increasingly complex digital landscape. more
Corporate domain strategies remain anchored in legacy extensions even as new domains proliferate, forcing firms to balance global reach, regional needs and rising fraud risks in an increasingly complex digital landscape. more
 WhoisXML API analysis deepens understanding of the UAT-8099 campaign, uncovering expanded DNS infrastructure, early indicators of malicious intent, and thousands of linked artifacts, underscoring the group's evolving tactics and regional focus across Asia. more
WhoisXML API analysis deepens understanding of the UAT-8099 campaign, uncovering expanded DNS infrastructure, early indicators of malicious intent, and thousands of linked artifacts, underscoring the group's evolving tactics and regional focus across Asia. more
 The first quarter of 2026 closed with 392.5 million domain name registrations across all top-level domains (TLDs), an increase of 24.1 million domain name registrations compared to the first quarter of 2025, according to the latest issue of the Domain Name Industry Brief Quarterly Report released Thursday at DNIB.com. more
The first quarter of 2026 closed with 392.5 million domain name registrations across all top-level domains (TLDs), an increase of 24.1 million domain name registrations compared to the first quarter of 2025, according to the latest issue of the Domain Name Industry Brief Quarterly Report released Thursday at DNIB.com. more
 Researchers tracing the ForceMemo campaign uncover a sprawling DNS footprint, linking compromised GitHub repositories to suspicious domains, shared infrastructure and fresh artifacts, suggesting a coordinated operation that continues to evolve despite partial attribution. more
Researchers tracing the ForceMemo campaign uncover a sprawling DNS footprint, linking compromised GitHub repositories to suspicious domains, shared infrastructure and fresh artifacts, suggesting a coordinated operation that continues to evolve despite partial attribution. more
What is a Dedicated IP VPN? A Dedicated IP VPN is a Virtual Private Network (VPN) service that provides users with a unique, static IP address assigned exclusively to them. Unlike a shared IP address, which is used by multiple users simultaneously, a dedicated IP is reserved for a single user, offering greater control and security over their online activities. more
Starlink provides high-speed, low-latency satellite internet, making it ideal for rural and remote areas lacking traditional broadband. Installation is user-friendly, and coverage continues to expand globally. However, the service is relatively expensive, and performance can be impacted by adverse weather. Overall, Starlink is a reliable choice for those without access to conventional internet options. more
ISPs can see that you are using a VPN, as they can detect encrypted traffic and the IP address of the VPN server. However, they cannot see the content of your data or the websites you visit while the VPN is active because the data is encrypted. This provides privacy for your online activities, though the fact that you're using a VPN itself is visible to the ISP. more
Satellite internet is a broadband service that connects users via signals transmitted between orbiting satellites and a satellite dish at the user's location. Unlike fiber or cable, it doesn't require physical infrastructure, making it essential in rural and remote areas. Although historically slower with higher latency, advancements like Low Earth Orbit (LEO) satellites have improved speed and reduced delays, enhancing overall performance. more
Yes, NordVPN still works with Netflix in 2024. It effectively bypasses geo-restrictions, unlocking libraries from major regions like the U.S., UK, Japan, and more. However, occasional issues like blocked servers or slow connections may arise. Troubleshooting, such as switching servers or using SmartPlay, typically resolves problems and maintains reliable access to Netflix. more
NordVPN offers two ways to try the service risk-free: a 7-day free trial for Android users and a 30-day money-back guarantee for all users. Both options allow full access to NordVPN's premium features. The trial requires payment details but can be canceled before charges occur. NordVPN provides superior security, performance, and global content access compared to free alternatives. more
NordVPN stands out for its unique double encryption, adding an extra layer of privacy. With blazing-fast servers in 60 countries, it's perfect for streaming, gaming, and bypassing geo-blocks. Its strict no-logs policy and advanced features like CyberSec ad-blocker make it a top choice for anyone seeking strong security and seamless performance. more
The best countries for VPN server locations include Switzerland, Iceland, and Panama for privacy, Germany, Japan, and the United States for fast connections, and the U.S., U.K., and Canada for streaming. These countries offer strong privacy laws, advanced infrastructure, and optimal performance for various online activities. more
VPNs are critical for remote work because they secure data by encrypting internet connections, protecting sensitive company information from cyberattacks. They also enable remote access to company networks, ensuring employees can work safely from any location while maintaining privacy and compliance with security policies. more
A VPN protects you by encrypting your internet connection, hiding your IP address, and routing your data through a secure server. This shields your online activities from hackers, trackers, and surveillance, ensuring privacy and security, especially on public Wi-Fi or when accessing sensitive information. more