

 One major element of many brand-protection programmes is the use of an algorithm to sort the findings identified through monitoring, according to their relevance or level of potential threat. This prioritisation process offers a number of benefits, including the identification of priority targets for further analysis, content tracking, or enforcement. more
One major element of many brand-protection programmes is the use of an algorithm to sort the findings identified through monitoring, according to their relevance or level of potential threat. This prioritisation process offers a number of benefits, including the identification of priority targets for further analysis, content tracking, or enforcement. more
 In today's rapidly shifting digital landscape, the question of whether the Internet can retain its foundational values has never been more urgent. As it increasingly permeates every aspect of human activity - from communication and commerce to governance and geopolitics - the Internet has evolved into both a shared global commons and a contested arena of power. At stake are its core values: global connectivity, openness, interoperability, decentralization, the end-to-end principle, robustness and reliability, and freedom from harm. more
In today's rapidly shifting digital landscape, the question of whether the Internet can retain its foundational values has never been more urgent. As it increasingly permeates every aspect of human activity - from communication and commerce to governance and geopolitics - the Internet has evolved into both a shared global commons and a contested arena of power. At stake are its core values: global connectivity, openness, interoperability, decentralization, the end-to-end principle, robustness and reliability, and freedom from harm. more
 Artificial intelligence (AI) has become synonymous with innovation, transforming industries at an unprecedented pace. While some may frame AI as a groundbreaking development of our time, it's essential to acknowledge that its roots run deep. AI has evolved immensely from early tools like the abacus to present-day GPU-driven large language models. What sets the current landscape apart? The sheer scale of data, computational demand, and complexity of workloads. more
Artificial intelligence (AI) has become synonymous with innovation, transforming industries at an unprecedented pace. While some may frame AI as a groundbreaking development of our time, it's essential to acknowledge that its roots run deep. AI has evolved immensely from early tools like the abacus to present-day GPU-driven large language models. What sets the current landscape apart? The sheer scale of data, computational demand, and complexity of workloads. more
 The marketing area of the broadband industry spends a lot of time convincing folks that the most important part of a broadband product is download speed. This makes sense if fiber and cable are competing in a market against slower technologies. But it seems like most advertising about speed is to convince existing customers to upgrade to faster speeds. While download speed is performance, the industry doesn't spend much time talking about the other important attributes of broadband. more
The marketing area of the broadband industry spends a lot of time convincing folks that the most important part of a broadband product is download speed. This makes sense if fiber and cable are competing in a market against slower technologies. But it seems like most advertising about speed is to convince existing customers to upgrade to faster speeds. While download speed is performance, the industry doesn't spend much time talking about the other important attributes of broadband. more
 Today, the Supreme Court will consider a challenge to the universal service subsidy program established soon after the introduction of telephone service by the AT&T Bell System and later officially adopted by the FCC as mandated by a 1996 law.1, 2 Universal service funding supports access to telephone and broadband service by subscribers in rural locales that commercial ventures will not serve absent a subsidy. more
Today, the Supreme Court will consider a challenge to the universal service subsidy program established soon after the introduction of telephone service by the AT&T Bell System and later officially adopted by the FCC as mandated by a 1996 law.1, 2 Universal service funding supports access to telephone and broadband service by subscribers in rural locales that commercial ventures will not serve absent a subsidy. more
 As we navigate through 2025, the domain industry remains a critical focal point amid persistent geopolitical instabilities, inflation, and an ongoing energy crisis. These pressures have reshaped the landscape of domain registrations and the domain aftermarket. Despite these challenges, digitalization continues to drive innovation and efficiency across sectors. more
As we navigate through 2025, the domain industry remains a critical focal point amid persistent geopolitical instabilities, inflation, and an ongoing energy crisis. These pressures have reshaped the landscape of domain registrations and the domain aftermarket. Despite these challenges, digitalization continues to drive innovation and efficiency across sectors. more
 On Jan. 11, 2025, Verisign supported the Internet Corporation for Assigned Names and Numbers (ICANN) in taking a major step to ensure the continued security, stability, and resiliency of the Domain Name System (DNS). While imperceptible to most users, this action - specifically, the introduction of a new Domain Name System Security Extensions (DNSSEC) Key Signing Key (KSK) in the root zone - is the next step of a multi-year-long process to change, or "roll," the cryptographic key that secures the root of the DNS. more
On Jan. 11, 2025, Verisign supported the Internet Corporation for Assigned Names and Numbers (ICANN) in taking a major step to ensure the continued security, stability, and resiliency of the Domain Name System (DNS). While imperceptible to most users, this action - specifically, the introduction of a new Domain Name System Security Extensions (DNSSEC) Key Signing Key (KSK) in the root zone - is the next step of a multi-year-long process to change, or "roll," the cryptographic key that secures the root of the DNS. more
Experts at a CircleID and Edgemoor Research Institute webinar debated the challenges of domain registration data access in a post-GDPR world. Panelists explored the tension between privacy laws and legitimate data requests, the role of automation in disclosure decisions, and the need for a scalable, trust-based framework to balance compliance, cybersecurity, and enforcement interests. more
 At 4:04 am on February 26 Mykhailo Fedorov, Vice Prime Minister and Minister of Digital Transformation of Ukraine, requested Starlink service from Elon Musk, and at 2:45 pm on the 26th, Elon Musk tweeted "Starlink service is now active in Ukraine. More terminals en route." On February 28 at 12:29 pm, Fedorov posted a photo of a truckload of terminals. (Kyiv is 10 hours ahead of California) and an engineer, Oleg Kutkov, posted the first tweet from Ukraine. more
At 4:04 am on February 26 Mykhailo Fedorov, Vice Prime Minister and Minister of Digital Transformation of Ukraine, requested Starlink service from Elon Musk, and at 2:45 pm on the 26th, Elon Musk tweeted "Starlink service is now active in Ukraine. More terminals en route." On February 28 at 12:29 pm, Fedorov posted a photo of a truckload of terminals. (Kyiv is 10 hours ahead of California) and an engineer, Oleg Kutkov, posted the first tweet from Ukraine. more
 There was one unpleasant message from the 2025 Munich Security Conference (MSC), which will have probably far reaching consequences for the governance of the digital space: Cyberspace will be governed by the rules of geo-political conflicts. And it is a battlefield in the 21st century wars. Both in the "Bayerischer Hof" and in the "IHK Munich", where the 11th edition of the Munich Cybersecurity Conference (MCSC) took place, controversial debates circled around the question of how civilian and military use of digital services will interplay in the years to come. more
There was one unpleasant message from the 2025 Munich Security Conference (MSC), which will have probably far reaching consequences for the governance of the digital space: Cyberspace will be governed by the rules of geo-political conflicts. And it is a battlefield in the 21st century wars. Both in the "Bayerischer Hof" and in the "IHK Munich", where the 11th edition of the Munich Cybersecurity Conference (MCSC) took place, controversial debates circled around the question of how civilian and military use of digital services will interplay in the years to come. more
 Information and Communications (ICT) infrastructures rely on many globally shared critical resilience information resources for diverse essential functions such as identifiers, routing, and cyber security. However, this ICT ecosystem has rapidly become significantly less stable and collaborative with dramatically diminished respect for legal norms and values because of the new USA national Administration. The instability includes the vicarious, wholesale removal of essential public safety and scientific databases, as well as global collaboration with multiple global UN public safety bodies. One result is the scaling of Digital Sovereignty initiatives. more
Information and Communications (ICT) infrastructures rely on many globally shared critical resilience information resources for diverse essential functions such as identifiers, routing, and cyber security. However, this ICT ecosystem has rapidly become significantly less stable and collaborative with dramatically diminished respect for legal norms and values because of the new USA national Administration. The instability includes the vicarious, wholesale removal of essential public safety and scientific databases, as well as global collaboration with multiple global UN public safety bodies. One result is the scaling of Digital Sovereignty initiatives. more
 Between 2021 and 2023, the IPv4 market was a roller coaster ride - prices shot up in 2021, peaked in 2022, and plummeted in 2023. Those who expected a recovery in 2024 were sadly disappointed. Prices for IP addresses continued to decline, leveling out during the second half of the year. And yet, market activity remained remarkably unaffected - a sign, perhaps, that the market is settling into a new normal. more
Between 2021 and 2023, the IPv4 market was a roller coaster ride - prices shot up in 2021, peaked in 2022, and plummeted in 2023. Those who expected a recovery in 2024 were sadly disappointed. Prices for IP addresses continued to decline, leveling out during the second half of the year. And yet, market activity remained remarkably unaffected - a sign, perhaps, that the market is settling into a new normal. more
 As counterfeit networks grow more elusive, AI-driven clustering could revolutionize brand protection. By linking disparate findings, identifying serial infringers, and enabling bulk enforcement, AI offers a smarter approach to monitoring and takedown efforts. Yet, challenges remain - from data reliability to analyzing complex content. Companies that master AI-driven clustering may gain a significant advantage in the fight against brand abuse. more
As counterfeit networks grow more elusive, AI-driven clustering could revolutionize brand protection. By linking disparate findings, identifying serial infringers, and enabling bulk enforcement, AI offers a smarter approach to monitoring and takedown efforts. Yet, challenges remain - from data reliability to analyzing complex content. Companies that master AI-driven clustering may gain a significant advantage in the fight against brand abuse. more
 NVIDIA recently issued its third annual State of AI in Telecommunications report. The company manufactures many of the cards used in AI data centers, so the company is clearly focused on AI adoption. NVIDIA issues similar reports for other industries. The 2025 report is the result of a survey that NVIDIA administered to 450 telecom professionals across the globe. more
NVIDIA recently issued its third annual State of AI in Telecommunications report. The company manufactures many of the cards used in AI data centers, so the company is clearly focused on AI adoption. NVIDIA issues similar reports for other industries. The 2025 report is the result of a survey that NVIDIA administered to 450 telecom professionals across the globe. more
 In a contemporary era when the human rights, democracy, and the rule of law are under attack, Europe has asserted itself as the leading global digital steward for maintaining those values. However, doing so through its Digital Sovereignty initiatives is significantly dependent on the ability to produce timely technical standards that underpin the implementing legislation. more
In a contemporary era when the human rights, democracy, and the rule of law are under attack, Europe has asserted itself as the leading global digital steward for maintaining those values. However, doing so through its Digital Sovereignty initiatives is significantly dependent on the ability to produce timely technical standards that underpin the implementing legislation. more
Amid evolving privacy laws and rising cybersecurity threats, domain registration data disclosure remains a contentious issue. Beyond WHOIS: Filling the Gaps brings together experts to examine Project Jake's policy framework, aiming to balance privacy with legitimate access. Join industry leaders for insights on policy clarity, operational efficiency, and the future of domain name governance. more
 The terms Digital Sovereignty or Souveraineté numérique have recently risen in prominence to describe the international rule of law as it applies to information and communication technologies. At a time when disinformation is proliferating and the rule of law, democracy, and human rights, together with long-standing relationships, are being cast aside, digital sovereignty is scaling in importance as a key defensive measure among many nations. more
The terms Digital Sovereignty or Souveraineté numérique have recently risen in prominence to describe the international rule of law as it applies to information and communication technologies. At a time when disinformation is proliferating and the rule of law, democracy, and human rights, together with long-standing relationships, are being cast aside, digital sovereignty is scaling in importance as a key defensive measure among many nations. more
 In a 2024 end-of-year memo, Gary Bolton of the Fiber Broadband Association said that FBA had partnered with the consulting firm Cartesian to look at the pros and cons of Starlink in the U.S. FBA says that report shows that Starlink currently has 1.4 million customers in the U.S., and with the current satellite constellation has the capacity to serve 1.7 million customers. more
In a 2024 end-of-year memo, Gary Bolton of the Fiber Broadband Association said that FBA had partnered with the consulting firm Cartesian to look at the pros and cons of Starlink in the U.S. FBA says that report shows that Starlink currently has 1.4 million customers in the U.S., and with the current satellite constellation has the capacity to serve 1.7 million customers. more
The global debate over Internet privacy and security took center stage in a webinar hosted by CircleID in partnership with the Edgemoor Research Institute. The event marked the first in a series exploring the delicate balance between safeguarding personal data and ensuring legitimate access to domain name registration details. As governments, cybersecurity experts, law enforcement, and intellectual property holders grapple with the evolving regulatory landscape, Project Jake seeks to establish a framework that prioritizes policy clarity, efficiency, and adaptability. more
 Existing laws can address AI challenges without new regulations. Legal frameworks have adapted to past technologies, and AI should be no exception. The real issue lies in outdated legal immunities, like Section 230, shielding tech companies from AI-driven harms. Accountability should focus on those who create and benefit from AI, not AI itself. more
Existing laws can address AI challenges without new regulations. Legal frameworks have adapted to past technologies, and AI should be no exception. The real issue lies in outdated legal immunities, like Section 230, shielding tech companies from AI-driven harms. Accountability should focus on those who create and benefit from AI, not AI itself. more
 Africa’s Digital Darkness: Internet Shutdowns Reach Record High
Africa’s Digital Darkness: Internet Shutdowns Reach Record High
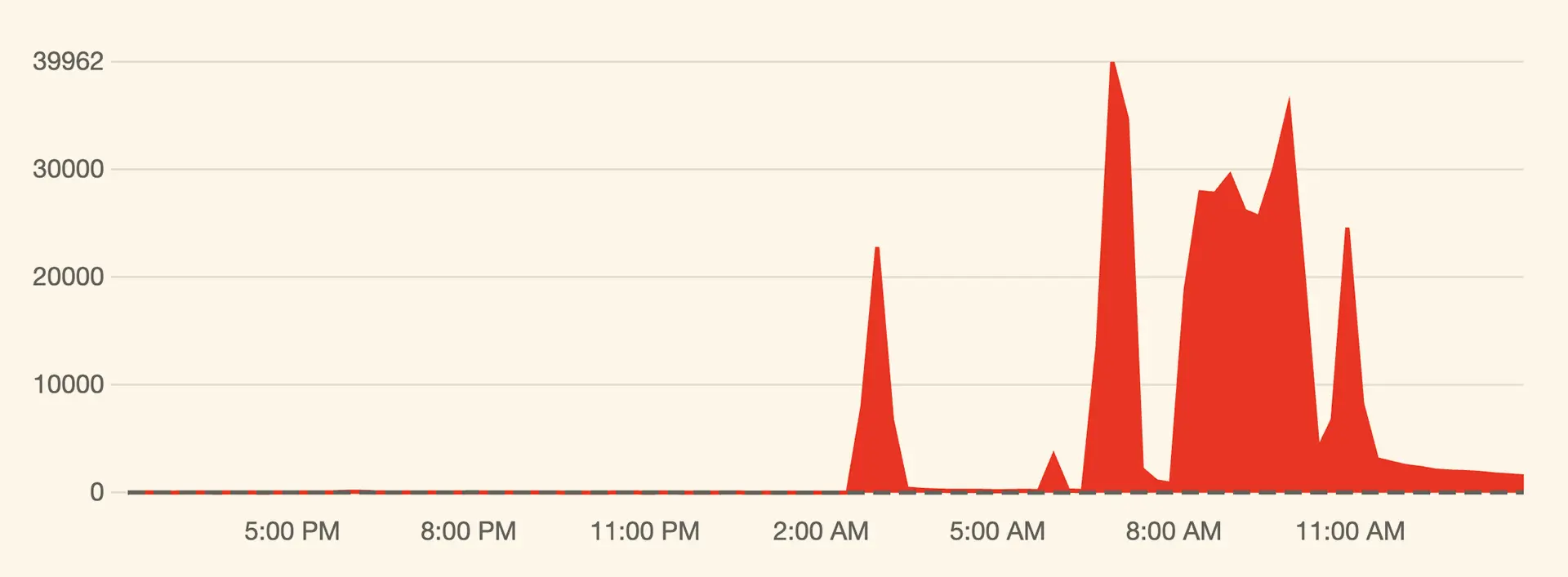 Massive Cyber Assault on X: Musk Hints at Foreign Involvement
Massive Cyber Assault on X: Musk Hints at Foreign Involvement
 Lack of Broadband Competition Leads to Higher Prices in Most U.S. Counties
Lack of Broadband Competition Leads to Higher Prices in Most U.S. Counties
 Meta’s Undersea Ambitions: A Cable to Power the AI Future
Meta’s Undersea Ambitions: A Cable to Power the AI Future
 India Launches ‘.bank.in’ and ‘.fin.in’ Domains to Deter Financial Fraud
India Launches ‘.bank.in’ and ‘.fin.in’ Domains to Deter Financial Fraud
 Baltic Sea Infrastructure Targeted Amid Rising Geopolitical Tensions
Baltic Sea Infrastructure Targeted Amid Rising Geopolitical Tensions
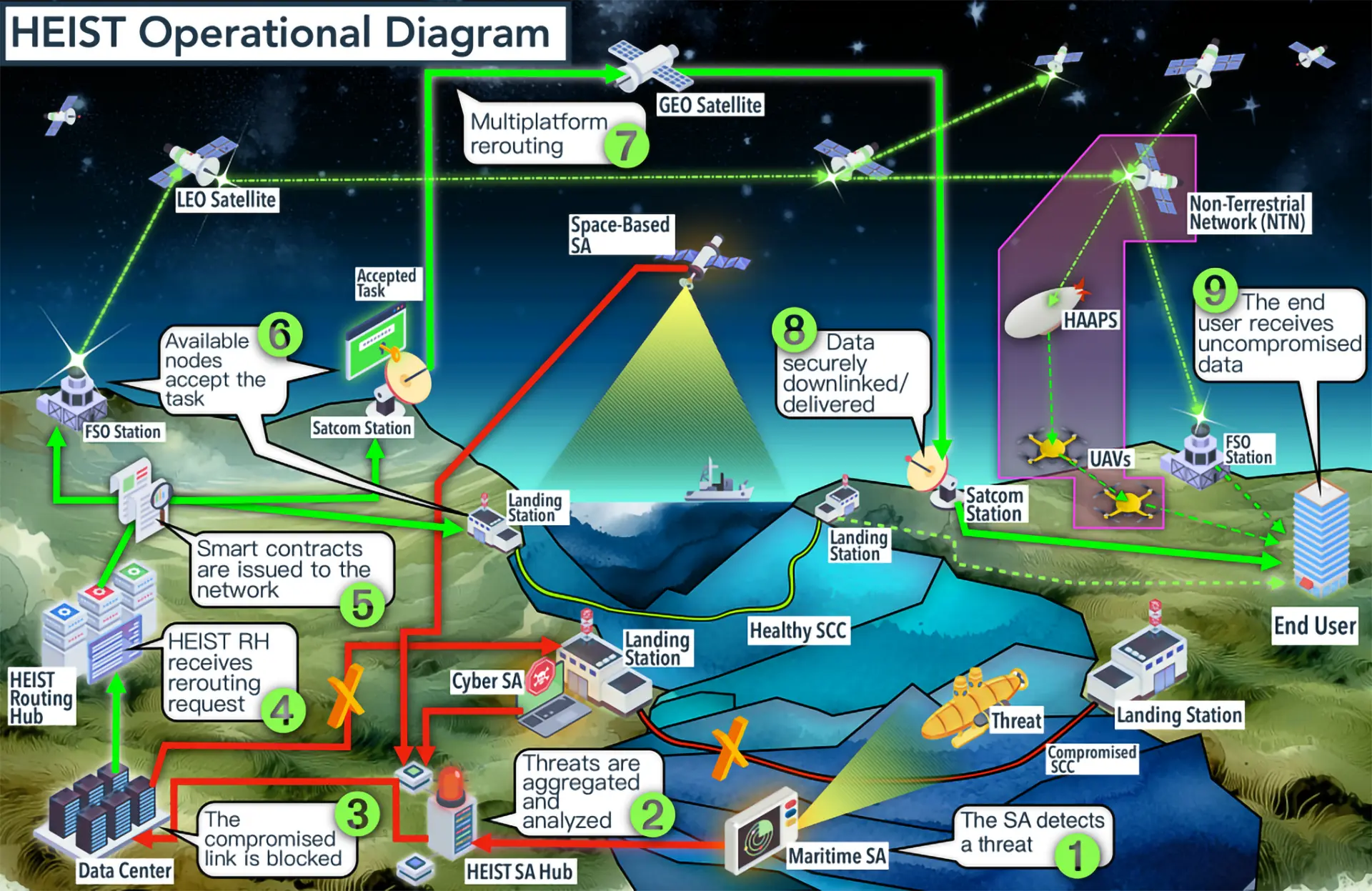 NATO’s Orbital Lifeline: A Backup Plan for the Internet
NATO’s Orbital Lifeline: A Backup Plan for the Internet
 Europe Seeks Space Independence with €10.6bn Iris² Satellite Network
Europe Seeks Space Independence with €10.6bn Iris² Satellite Network
 Domain Trends Signal Shifting Tides in 2024
Domain Trends Signal Shifting Tides in 2024
 Chinese Hackers Exploit U.S. Telecom Systems, Eviction Efforts Lag
Chinese Hackers Exploit U.S. Telecom Systems, Eviction Efforts Lag
 Meta’s $10 Billion Plan to Build the World’s Largest Subsea Cable Network
Meta’s $10 Billion Plan to Build the World’s Largest Subsea Cable Network
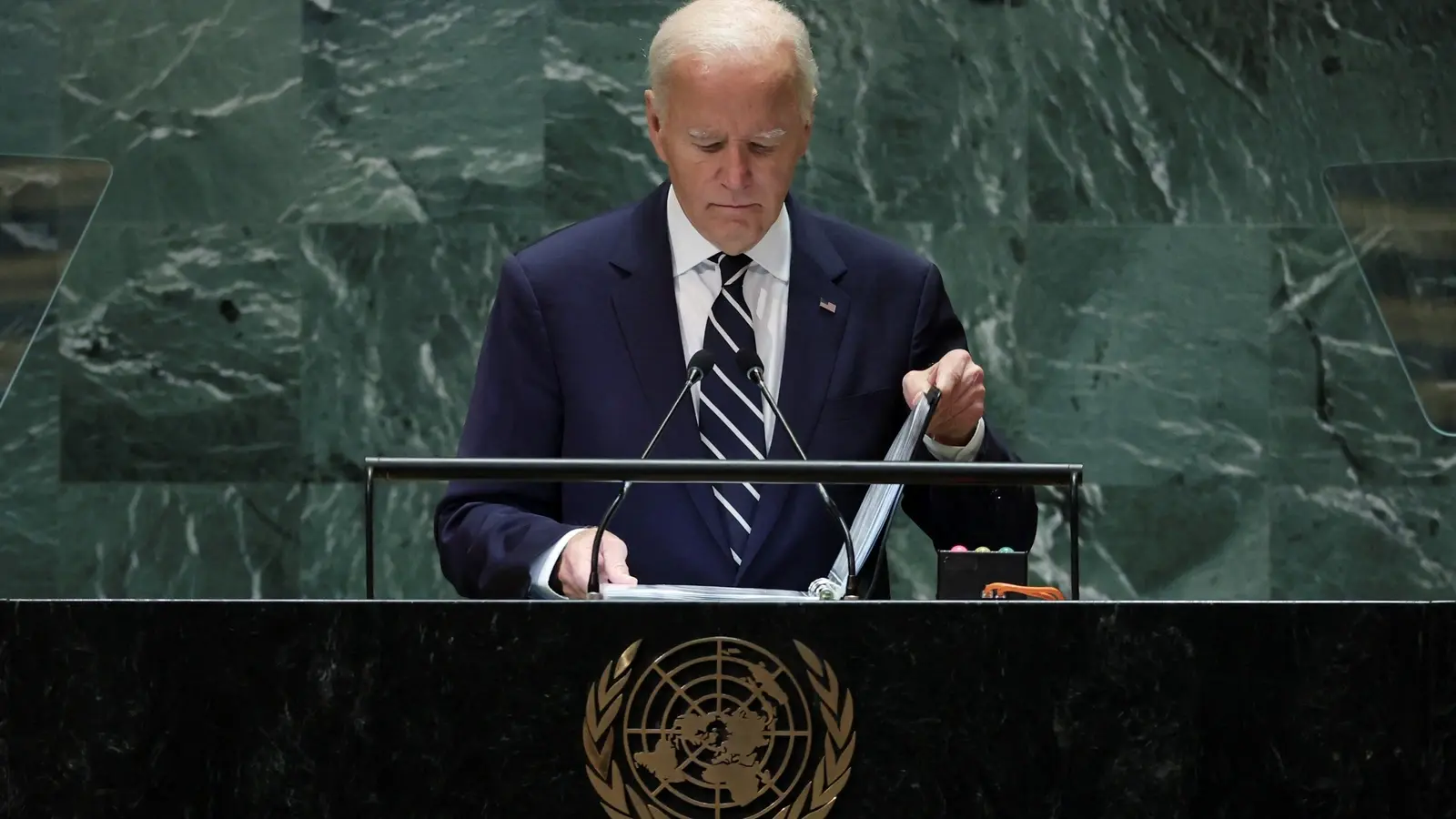 Biden Administration to Back UN Cybercrime Treaty Amid Controversy
Biden Administration to Back UN Cybercrime Treaty Amid Controversy
 PIR Reaches 11 Million .ORG Domains, Citing Growth and Online Safety Efforts
PIR Reaches 11 Million .ORG Domains, Citing Growth and Online Safety Efforts
 Internet Visionaries Honored with Postel Service Award
Internet Visionaries Honored with Postel Service Award
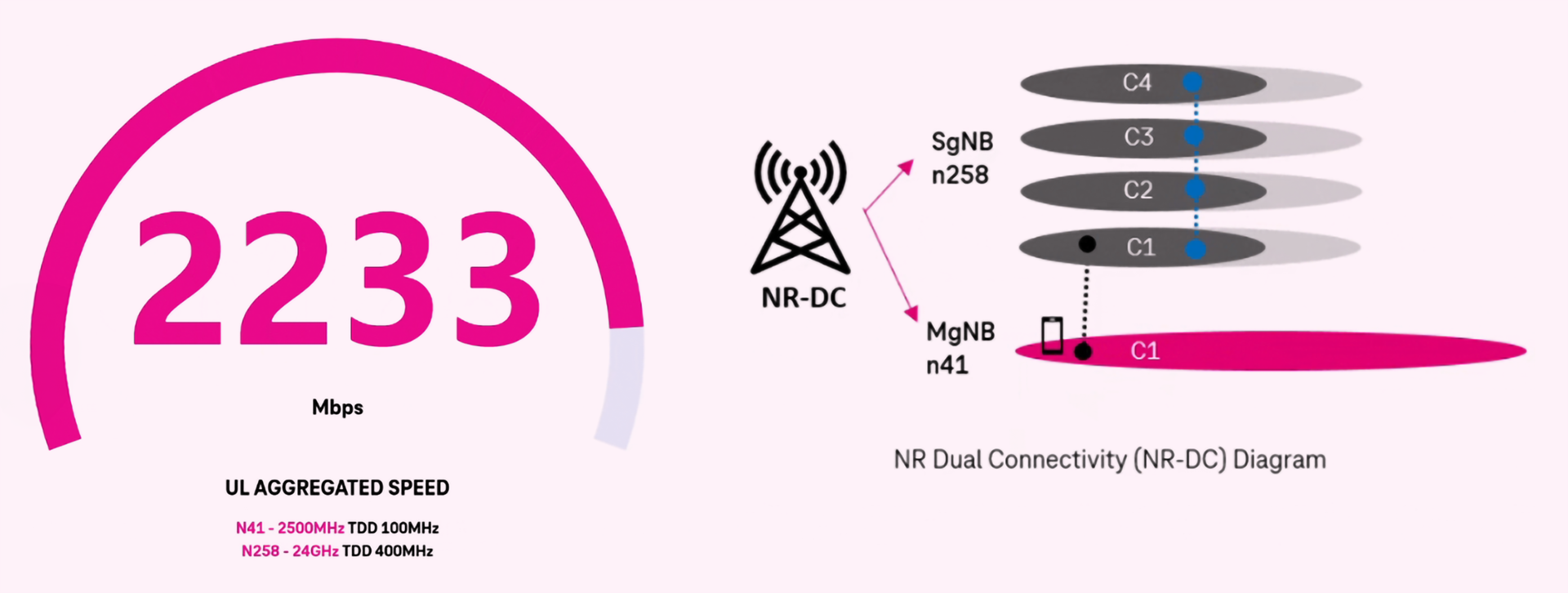 T-Mobile Breaks Upload Speed Record with New 5G Dual Connectivity
T-Mobile Breaks Upload Speed Record with New 5G Dual Connectivity
 OpenAI Buys Chat.com, Redirected to ChatGPT
OpenAI Buys Chat.com, Redirected to ChatGPT
 Chinese Hackers Had Access to Canadian Government Systems for Years, Report Reveals
Chinese Hackers Had Access to Canadian Government Systems for Years, Report Reveals
 EU Internet Advocates Push Back Against Telecom “Fair-Share” Fees
EU Internet Advocates Push Back Against Telecom “Fair-Share” Fees
Sponsored byVerisign

Sponsored byIPv4.Global

Sponsored byDNIB.com

Sponsored byVerisign

Sponsored byCSC

Sponsored byWhoisXML API

Sponsored byRadix

 Ransomware attacks have been plaguing individual users and organizations worldwide for years now. And that is not surprising because they work. In fact, ransomware victims were asked to pay an average of US$2.5 million in 2024. more
Ransomware attacks have been plaguing individual users and organizations worldwide for years now. And that is not surprising because they work. In fact, ransomware victims were asked to pay an average of US$2.5 million in 2024. more
 Trend Micro researchers recently uncovered a search engine optimization (SEO) manipulation campaign targeting users of Internet Information Services (IIS) with BadIIS. more
Trend Micro researchers recently uncovered a search engine optimization (SEO) manipulation campaign targeting users of Internet Information Services (IIS) with BadIIS. more
 The transition to IPv6 has reached a significant milestone in the United States. As of February 9, 2025, more than half of all traffic to Google's services from U.S. users is now conducted over IPv6. This marks a step forward for a country with deep historical ties to the Internet but one that still lags behind several others in adoption rates. more
The transition to IPv6 has reached a significant milestone in the United States. As of February 9, 2025, more than half of all traffic to Google's services from U.S. users is now conducted over IPv6. This marks a step forward for a country with deep historical ties to the Internet but one that still lags behind several others in adoption rates. more
 Microsoft and Google almost always land on the list of most-phished brands, and that is not surprising given their huge market presence. And phishers are often the most likely threat actors to bank on the brands' popularity for the success of their attacks. more
Microsoft and Google almost always land on the list of most-phished brands, and that is not surprising given their huge market presence. And phishers are often the most likely threat actors to bank on the brands' popularity for the success of their attacks. more
 Sneaky 2FA, believed to be sold via the phishing-as-a-service (PhaaS) business model, recently figured in an adversary-in-the-middle (AitM) attack targeting Microsoft 365 users. Marketed as Sneaky Log by a full-featured bot on Telegram, Sneaky 2FA reportedly used fake Microsoft authentication pages with automatically filled-in email address fields to add to its sense of authenticity. more
Sneaky 2FA, believed to be sold via the phishing-as-a-service (PhaaS) business model, recently figured in an adversary-in-the-middle (AitM) attack targeting Microsoft 365 users. Marketed as Sneaky Log by a full-featured bot on Telegram, Sneaky 2FA reportedly used fake Microsoft authentication pages with automatically filled-in email address fields to add to its sense of authenticity. more
 The extension includes custom features in terms of location and size on your browser and links directly to the IPv4.Global marketplace if something scrolls by that interests you. more
The extension includes custom features in terms of location and size on your browser and links directly to the IPv4.Global marketplace if something scrolls by that interests you. more
 IPv4.Global, the world's largest, most trusted and transparent IPv4 marketplace, today announced a first-of-its kind loan facility backed by the borrower's IPv4 addresses as collateral. more
IPv4.Global, the world's largest, most trusted and transparent IPv4 marketplace, today announced a first-of-its kind loan facility backed by the borrower's IPv4 addresses as collateral. more
 The market for IPv4 addresses continues to exhibit stability, albeit at significantly lower prices than in previous peak periods. Data from IPv4.Global by Hilco Streambank suggests that while there is a notable spread in pricing - often reaching a 30% difference between high and low valuations - the overall trend points to a subdued yet steady marketplace. more
The market for IPv4 addresses continues to exhibit stability, albeit at significantly lower prices than in previous peak periods. Data from IPv4.Global by Hilco Streambank suggests that while there is a notable spread in pricing - often reaching a 30% difference between high and low valuations - the overall trend points to a subdued yet steady marketplace. more
 Radix's latest Premium Domains Report for the second half of 2024 highlights a strong performance across its portfolio, with .fun domains experiencing exceptional growth. Premium domain registrations increased by 11% year-on-year, while premium renewals rose by 16%. more
Radix's latest Premium Domains Report for the second half of 2024 highlights a strong performance across its portfolio, with .fun domains experiencing exceptional growth. Premium domain registrations increased by 11% year-on-year, while premium renewals rose by 16%. more
 Several American and European organizations across the energy, oil and gas, and legal sectors were recently targeted by a campaign leveraging MintsLoader, a malware loader that delivers malicious software to a victim's device. more
Several American and European organizations across the energy, oil and gas, and legal sectors were recently targeted by a campaign leveraging MintsLoader, a malware loader that delivers malicious software to a victim's device. more
What is a Dedicated IP VPN? A Dedicated IP VPN is a Virtual Private Network (VPN) service that provides users with a unique, static IP address assigned exclusively to them. Unlike a shared IP address, which is used by multiple users simultaneously, a dedicated IP is reserved for a single user, offering greater control and security over their online activities. more
Starlink provides high-speed, low-latency satellite internet, making it ideal for rural and remote areas lacking traditional broadband. Installation is user-friendly, and coverage continues to expand globally. However, the service is relatively expensive, and performance can be impacted by adverse weather. Overall, Starlink is a reliable choice for those without access to conventional internet options. more
ISPs can see that you are using a VPN, as they can detect encrypted traffic and the IP address of the VPN server. However, they cannot see the content of your data or the websites you visit while the VPN is active because the data is encrypted. This provides privacy for your online activities, though the fact that you're using a VPN itself is visible to the ISP. more
Satellite internet is a broadband service that connects users via signals transmitted between orbiting satellites and a satellite dish at the user's location. Unlike fiber or cable, it doesn't require physical infrastructure, making it essential in rural and remote areas. Although historically slower with higher latency, advancements like Low Earth Orbit (LEO) satellites have improved speed and reduced delays, enhancing overall performance. more
Yes, NordVPN still works with Netflix in 2024. It effectively bypasses geo-restrictions, unlocking libraries from major regions like the U.S., UK, Japan, and more. However, occasional issues like blocked servers or slow connections may arise. Troubleshooting, such as switching servers or using SmartPlay, typically resolves problems and maintains reliable access to Netflix. more
NordVPN offers two ways to try the service risk-free: a 7-day free trial for Android users and a 30-day money-back guarantee for all users. Both options allow full access to NordVPN's premium features. The trial requires payment details but can be canceled before charges occur. NordVPN provides superior security, performance, and global content access compared to free alternatives. more
NordVPN stands out for its unique double encryption, adding an extra layer of privacy. With blazing-fast servers in 60 countries, it's perfect for streaming, gaming, and bypassing geo-blocks. Its strict no-logs policy and advanced features like CyberSec ad-blocker make it a top choice for anyone seeking strong security and seamless performance. more
The best countries for VPN server locations include Switzerland, Iceland, and Panama for privacy, Germany, Japan, and the United States for fast connections, and the U.S., U.K., and Canada for streaming. These countries offer strong privacy laws, advanced infrastructure, and optimal performance for various online activities. more
VPNs are critical for remote work because they secure data by encrypting internet connections, protecting sensitive company information from cyberattacks. They also enable remote access to company networks, ensuring employees can work safely from any location while maintaining privacy and compliance with security policies. more
A VPN protects you by encrypting your internet connection, hiding your IP address, and routing your data through a secure server. This shields your online activities from hackers, trackers, and surveillance, ensuring privacy and security, especially on public Wi-Fi or when accessing sensitive information. more